HP has released a patch to fix a flaw in the HP OMEN driver.
As far as we know the flaw isn’t being actively exploited, but it’s worth applying the patch as soon as you can.
The flaw, the fix
The driver vulnerability, which is tracked as CVE-2021-3437, was found by Kasif Dekel, a senior security researcher at SentinelLabs.
If exploited, the vulnerability could allow a malicious threat actor to escalate privileges to kernel mode. This would enable the actor to perform tasks within affected systems, such as disabling security solutions, running malicious code in kernel mode, and elevating privileges of other users, and more. Exploiting this flaw could also allow the actor to trigger a denial-of-service (DoS) condition, which prevents traffic from going to the device.
The driver, HpPortIox64.sys, is used by the HP OMEN Gaming Hub (previously called HP OMEN Command Center), software that comes pre-installed in HP OMEN systems. Although this SYS file is created by HP, according to Dekel, it is actually “a partial copy of another problematic driver, WinRing0.sys, developed by OpenLibSys.”
HpPortIox64.sys essentially inherited the privilege kernel-mode problem from
WinRing0.sys“It’s worth mentioning that the impact of this vulnerability is platform dependent,” continues Dekel in the report, “It can potentially be used to attack device firmware or perform legacy PCI access by accessing ports 0xCF8/0xCFC. Some laptops may have embedded controllers which are reachable via IO port access.”
The flawed HP driver accepts IOCTL (Input/Output Control) requests from non-privileged users, who aren’t subjected to access control rules. Because of this, such drivers can be abused, “by design.”
Road 96 and OMEN
It’s worth mentioning that HP’s first official video game, Road 96, gives its video game players and fans the option to download the OMEN Gaming Hub in a section of the game.
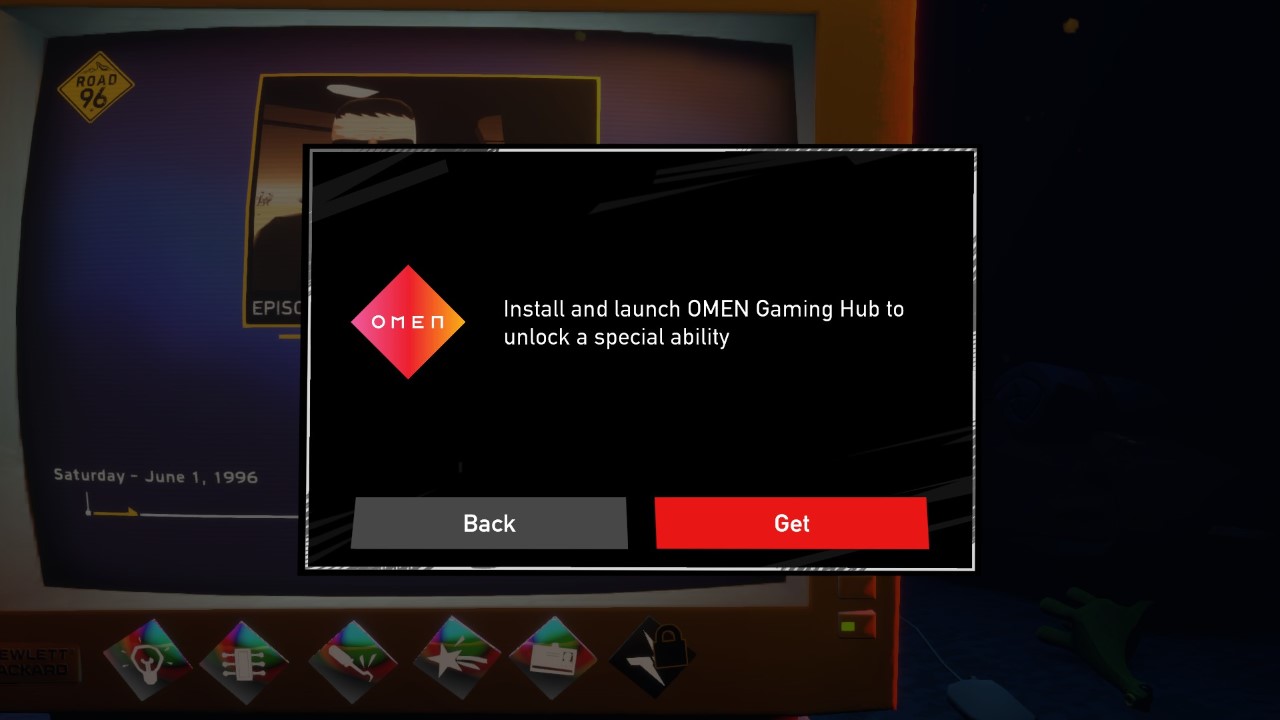
Although we can’t say for sure if the driver problem will pose a threat to non-HP users should they agree to install the Hub, we do note another threat to consider. According to Chris Boyd, lead malware intelligence analyst for Malwarebytes, “Certain games offer additional skills or abilities in return for installing OMEN, such as the award-winning, Road 96. As a result, many people will have it on their system even if they have no intention of ever using it. Where updates aren’t taking place, this could be dangerous should an exploit arise in the wild.”










