On his blog, Troy Hunt has announced a major milestone in the ‘Have I Been Pwned?’ project, thanks to the contributions of two of the world’s foremost law enforcement agencies, the FBI and the NCA (the UK equivalent of the FBI, the National Crime Agency).
This enormous injection of used passwords has puffed up the world’s largest publicly available password database by 38%, according to Hunt.
‘Have I Been Pwned?’
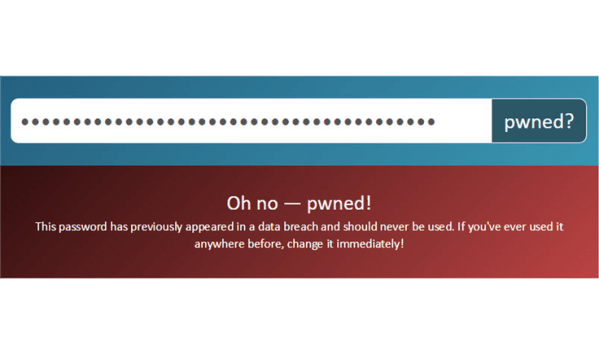
‘Have I Been Pwned?’ (HIBP) allows users to type in an email address, phone number or password and find out how many times they’ve been involved in a data breach. So, if HIBP says your email address was involved in the great big LinkedIn breach of 2012, the Canva breach of 2019, or any other notable episode of credential theft, you know to change your passwords on those systems, and not use them anywhere else. If it says a password you use has breached, you know to never use it again.
In recent years, HIBP has been integrated with a number of third-party systems like password managers and web browsers, so they can alert users immediately if they attempt to use a credential that might already be in the hands of cybercriminals.
The site has been around for almost a decade, and through the years it has proven itself to be an extremely useful tool for everyday Internet users, governments, and organizations alike. The project is run by Troy Hunt with support from the community. The model he uses makes sure that privacy is maintained and passwords can safely be checked without any risk of disclosure. And it’s extremely well used. To give you some perspective, in the last month, there were 1,260,000,000 occasions where a service somewhere checked a password against HIBP’s Pwned Password API.
Hunt says the system stores minimal information about each user, and it only stores SHA-1 hashes of passwords (because you can generate a hash from a password, but you can’t generate a password from a hash). If you enter a password to see if it’s been pwned, it’s immediately turned into a SHA-1 hash and checked against the database.
Police pipeline
In May of 2021, Hunt announced that the FBI had reached out to him and discussed what it might look like if the FBI were to feed compromised passwords into HIBP and surface them via the Pwned Passwords feature.
Over the last few months the HIBP project has been revamped to allow data be fed into the system as they are made available by law enforcement. This new pipeline enables the ingestion of passwords from law enforcement agencies, like the FBI and the NCA.
The NCA contribution has been enormous. At some point the NCA indicated it had hundreds of millions of passwords it believed weren’t already in the Pwned Passwords store of 613 million password hashes. After cross-checking, 225,665,425 turned out to be brand new. Adding them has inflated the total Pwned Passwords count to 847,223,402.
Have you been pwned?
While it is useful to know whether your personal details or credentials have been leaked, it is much more important to act on the information. So, what do you do now, knowing that your account might have been compromised?
For starters, change your password. Your new password needs to be hard to guess, and the best way to ensure that is to let a password manager do it for you. If you’re doing it yourself, pick something that is hard to guess: Avoid individual words, and avoid passwords that look like words with a few numb3r5 sprinkled in them. Instead, go for lengthy pass phrases or long, meaningless combinations of letters, numbers, and other characters.
Lastly, use two-factor authentication (2FA) to add a layer of protection to your accounts. We strongly suggest using a hardware key like a YubiKey. The next best option is a one-time password (OTP) app like Google Authenticator. Take note that some big-name companies like Facebook have already started giving their users the option to use a hardware key. So if you want to do that, check if your online service provider offers it, too, and take advantage of it.
Stay safe!