Researchers at Intezer have published a technical analysis of Lightning Framework, a previously undocumented and undetected Linux threat. Lightning is a modular framework that is very versatile and something we don’t see very often in the Linux space.
The old argument that Linux systems (or Macs for that matter) don’t get malware has never been true. Linux servers often play a key role in corporate networks, and are also very popular in cloud-based systems, making them attractive targets for criminals.
The Lightening Framework
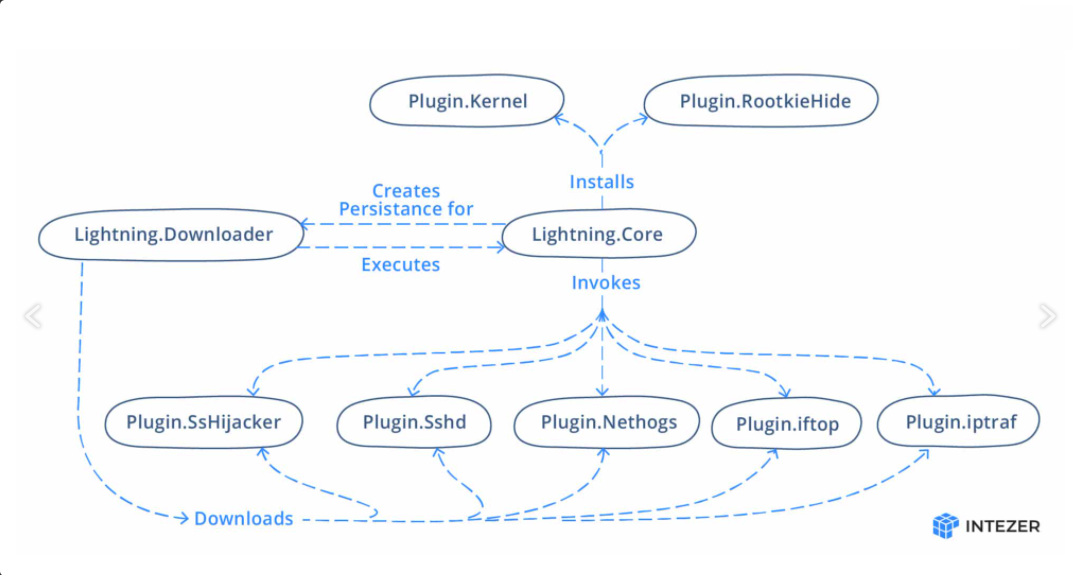
The Lightning Framework has a modular structure, consisting of a downloader (Lightning.Downloader) and a core module (Lightning.Core), with a number of plugins.
A modular architecture can make adding new capabilities or improvements easier, since an update to a plugin should not affect the core or any other plugins. It is also potentially useful to malware authors because if detection is based on one of the plugins then replacing the plugin that triggered the detection may allow the malware to go under the radar for a bit longer.
While some of the modules are known tools, it is rare to see such a complex and versatile framework target Linux systems.
How Lightening hides
The main function of the downloader module is to fetch the other components and execute the core module. The framework makes heavy use of typo-squatting and masquerading in order to remain undetected. Intezer reports that the downloader module is located in the working directory /usr/lib64/seahorses/ so anyone performing a quick inspection might think the directory belongs to the password and key manager software seahorse.
One of the tasks of the core module is to set up persistence. It does this by creating a script that gets executed upon system boot. The boot execution is achieved by first creating a file located at /etc/rc.d/init.d/elastisearch, an obvious attempt to typosquat elasticsearch.
The malware uses a timestomping technique to change the timestamp of the script so that it matches the timestamp of one of a few core Linux files. So that, without closer inspection an investigator might think it was created when the system was initially set up.
The framework also uses a rootkit to hide its Process ID (PID) and any related network ports. The rootkit can scrub any reference to files running in the framework.
Communication
Network communication in the core and downloader modules is performed over TCP sockets. The C2 server is stored in an encoded configuration file that is unique for every single creation.
The Linux.Plugin.Lightning.Sshd plugin is an OpenSSH daemon that includes hardcoded private and host keys, allowing the attacker to SSH into the machine with their own SSH key, creating a secondary backdoor.
For a deeper analysis of the malware and its plugins, and a list of IOCs, check out the full write up by Intezer.











