We mapped a sprawling fake shop operation of over 20,000 domains, dozens of shared IP addresses and identical storefronts with different names pasted on top. They exist for one purpose: to steal your payment details and personal data. The thread that ties them all together is a browser tab title most people would never think twice about: “Unrivaled selection only for you.”
Polished storefronts, empty warehouses
Fake shops are fraudulent websites designed to look and feel like legitimate online retailers. They have product listings, brand logos, customer reviews, shopping carts, and functional-looking checkout pages. They just never deliver what they promise. In some cases, victims receive nothing at all. In others, they get a cheap knockoff worth a fraction of the advertised price.
Either way, the product being sold is your data: these fake shops harvest your payment credentials, billing addresses, and personal details and then resell them on criminal marketplaces or use them directly for identity fraud.
The scale of the problem has exploded. According to recent threat intelligence data, fake e-shop scams rose by 790% in the first quarter of 2025 compared to the same period the year before, driven in part by economic anxiety around trade tariffs pushing consumers toward bargain alternatives.
During the 2024 holiday season alone, researchers identified over 80,000 fake stores, many of which disappeared or rebranded within days. Industry telemetry from late 2025 found that fake shops accounted for 65% of all threats blocked on social media, with Facebook and YouTube as the primary launchpads.
These operations are increasingly industrialized. Researchers recently documented FraudWear, a coordinated campaign involving over 30,000 fraudulent stores impersonating more than 350 fashion brands worldwide.
Another investigation uncovered BogusBazaar, a franchise-style network where a core team maintained the servers, payment processing, and template infrastructure, while decentralized operators spun up individual shops on top of it. That network processed over a million orders across 75,000 domains since 2021.
Fake shops succeed because they use familiar shopping behavior: clicking on ads, following search results, and landing on polished-looking sites. They layer psychological pressure on top, with limited-time offers, countdown timers, and disappearing stock warnings.
Same storefront, different names
While investigating suspicious e-commerce domains, we identified a cluster of more than 20,000 sites sharing common infrastructure patterns.
Most used the .shop top-level domain (TLD), which has become a favourite among scammers thanks to cheap registration fees and a plausible-looking name. The .shop extension now ranks among the top TLDs associated with spam and malicious activity, according to Cloudflare’s email security data.
Digging into the page source revealed what ties these sites together. All run on WordPress and are powered by Sellvia, a legitimate US-based e-commerce platform that allows users to launch a dropshipping store quickly with ready-made templates, product catalogs, and payment processing.
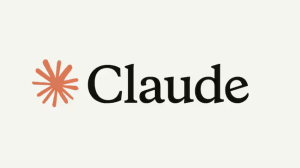
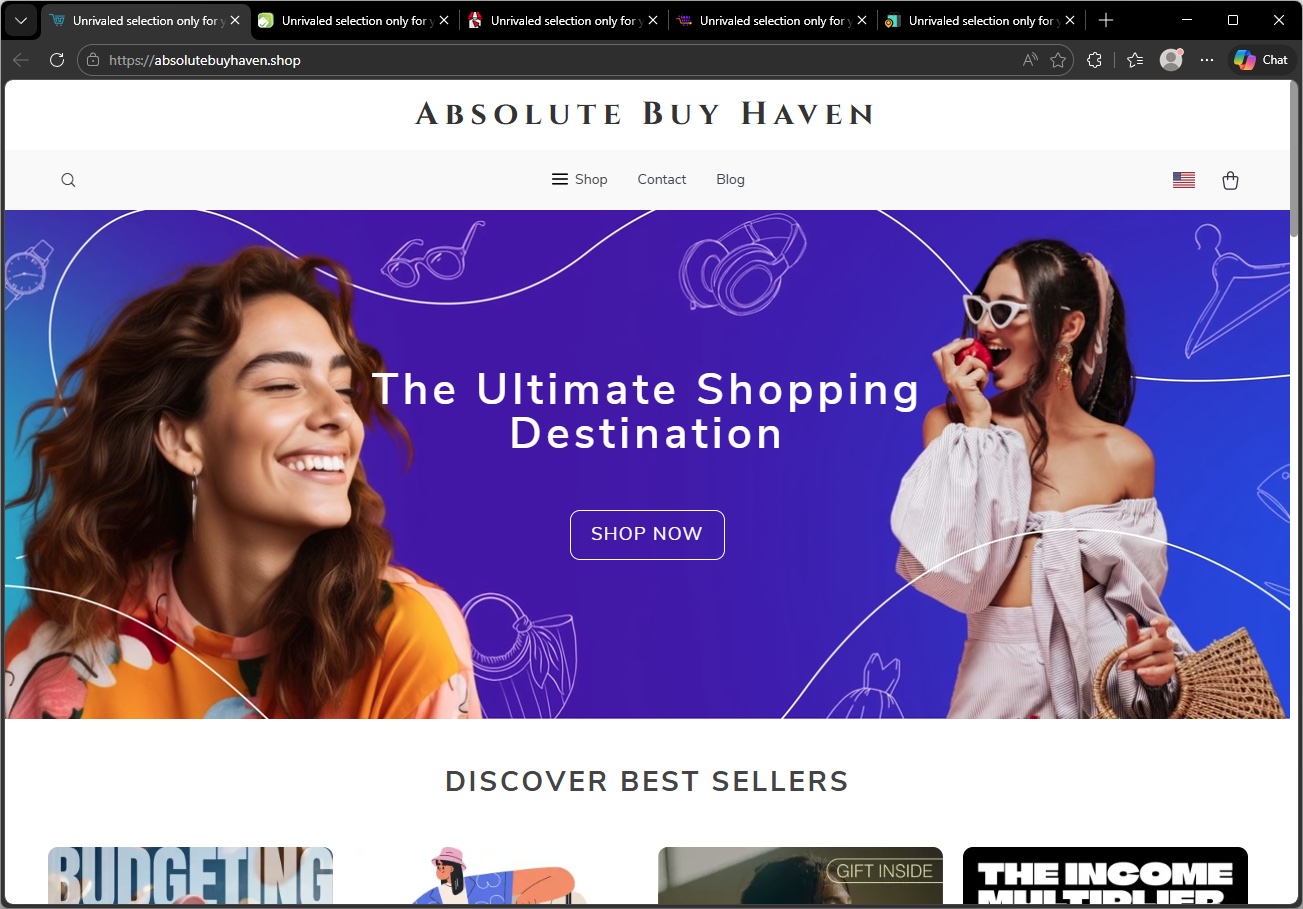
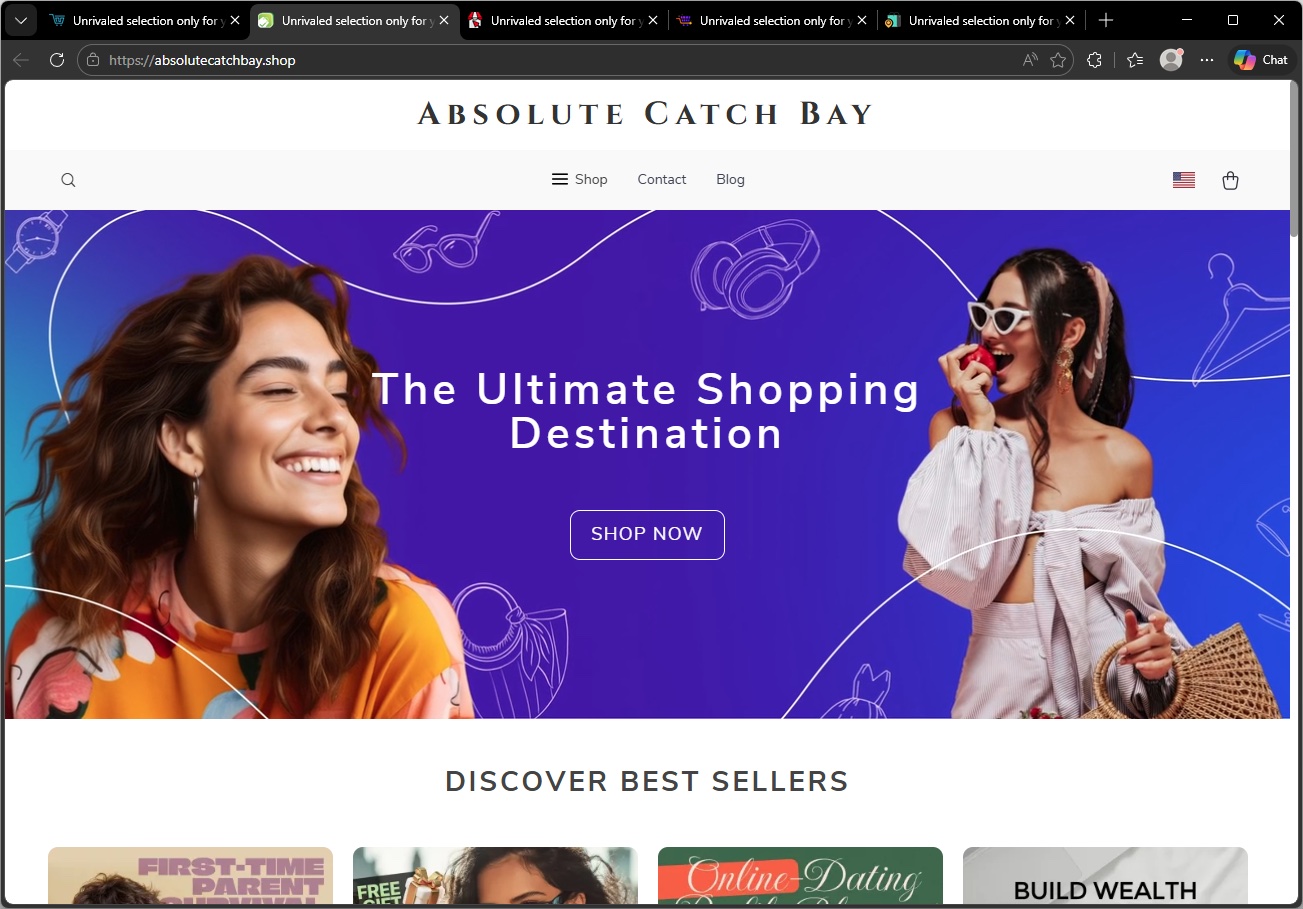
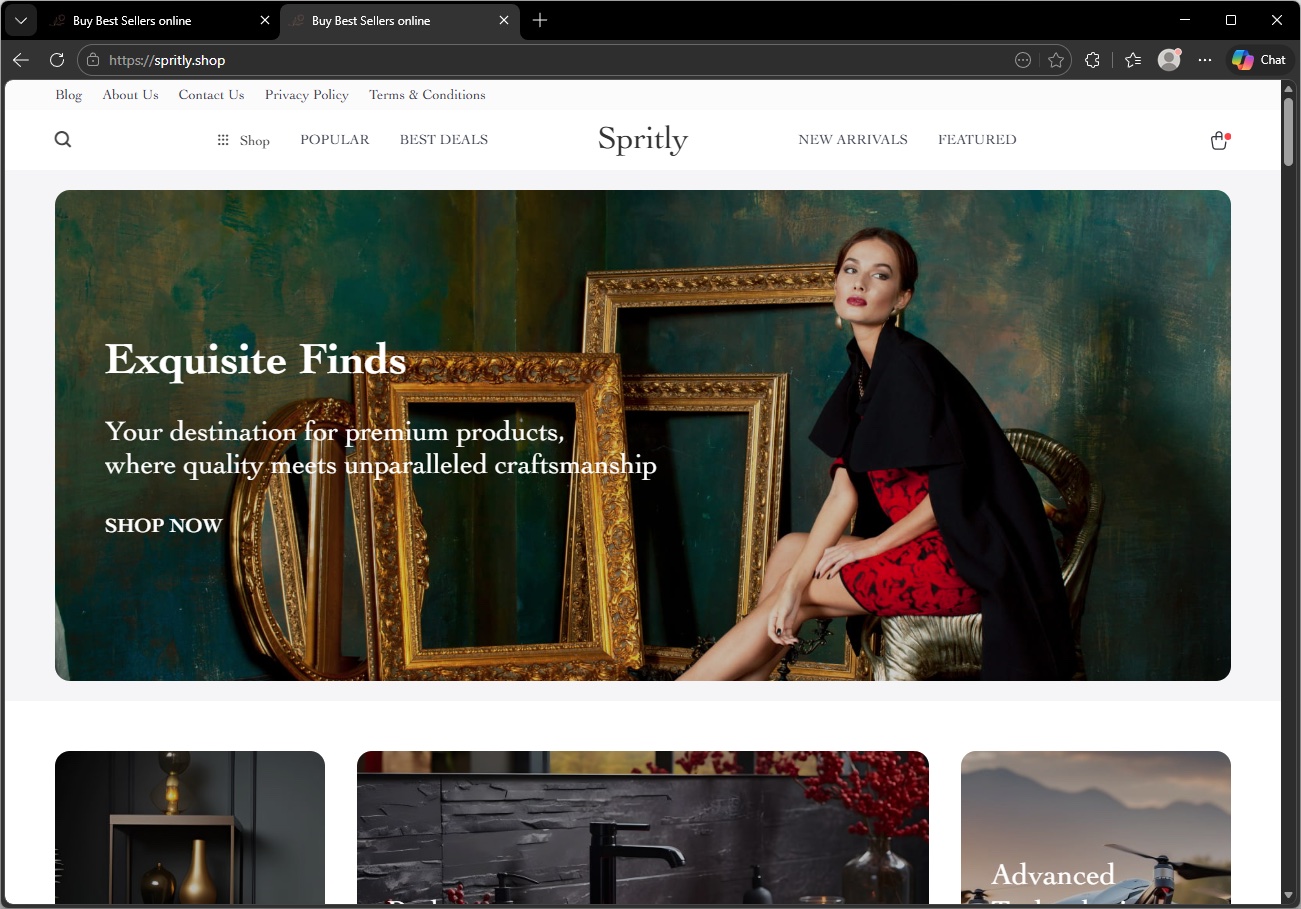
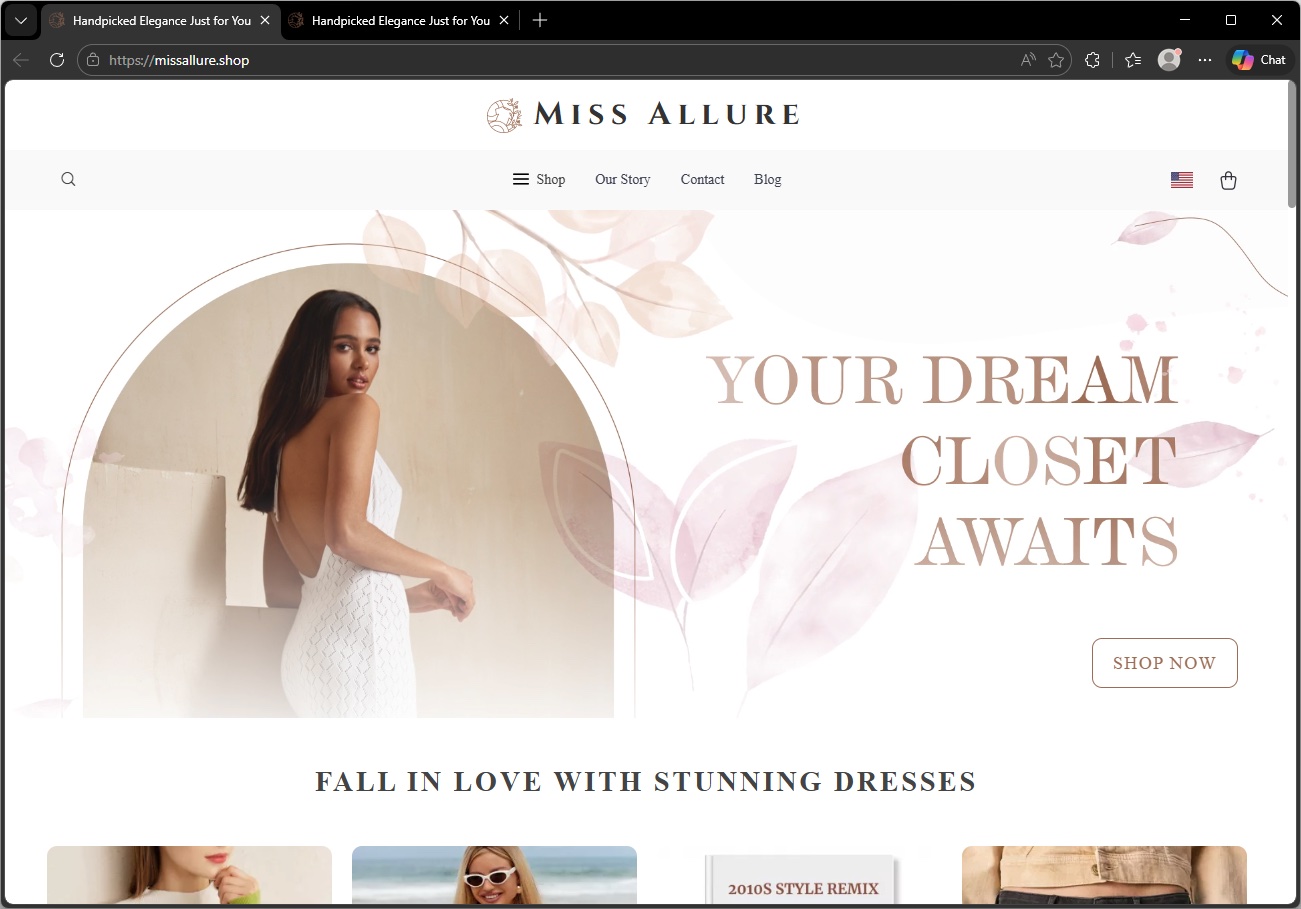
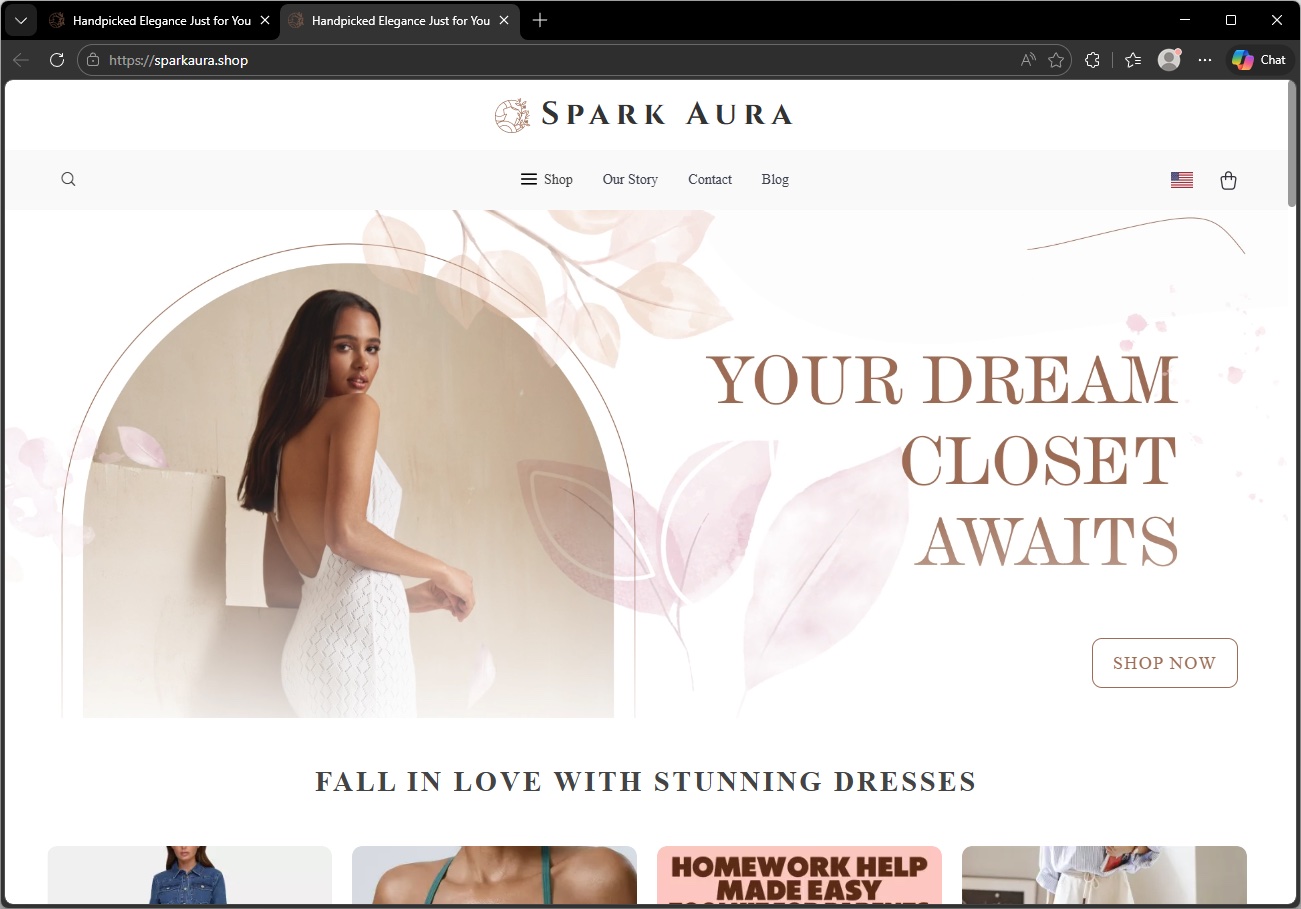
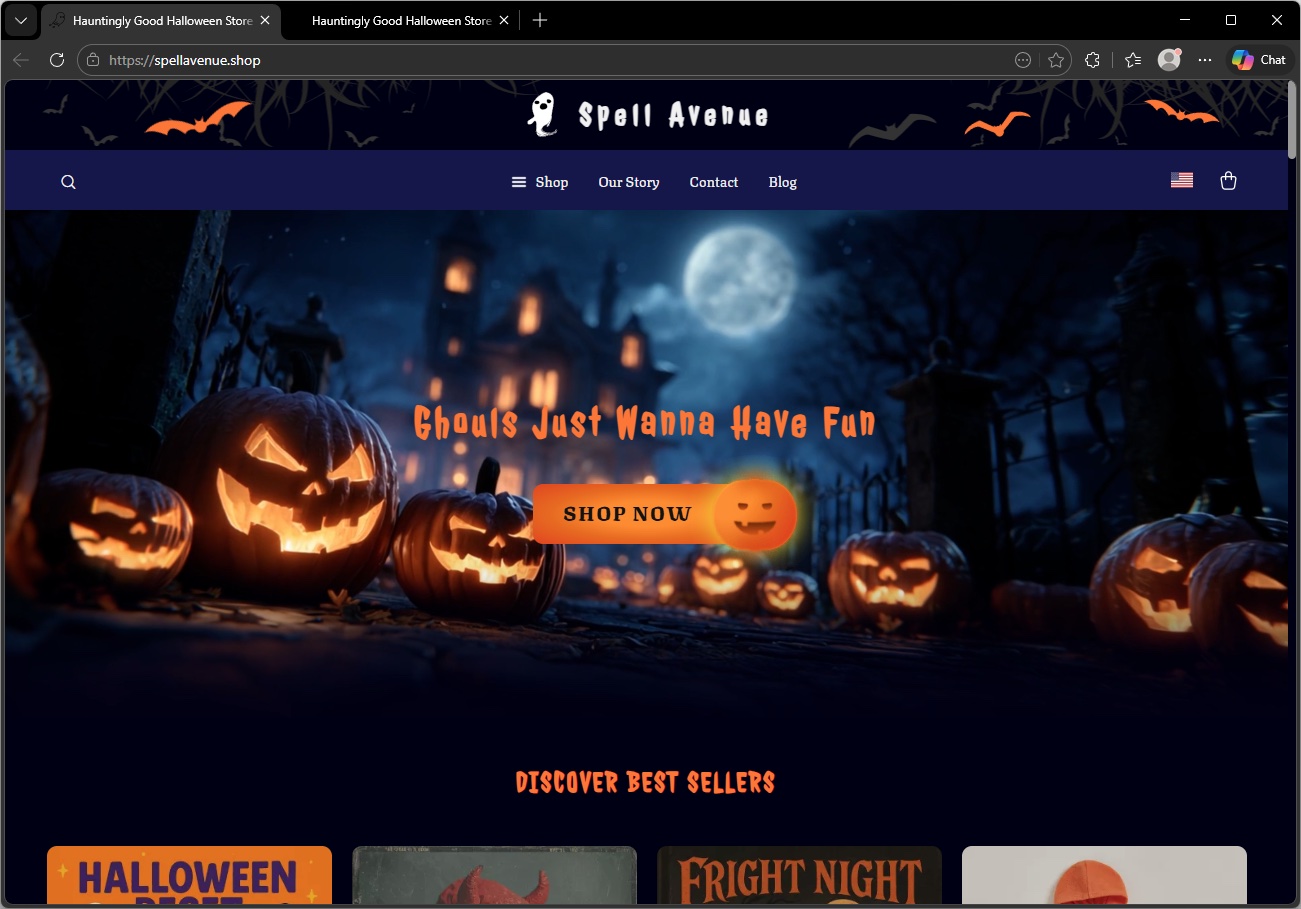
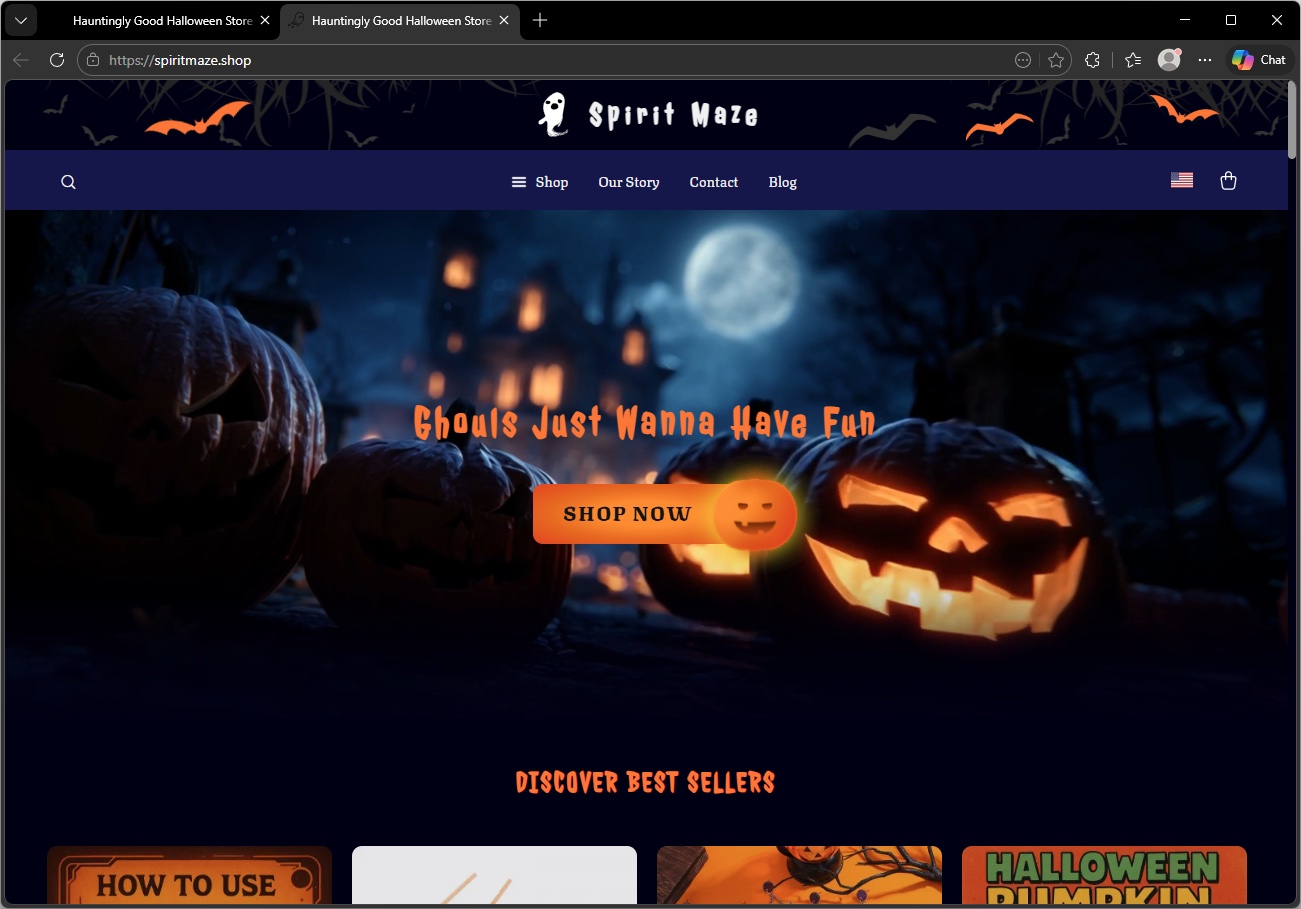
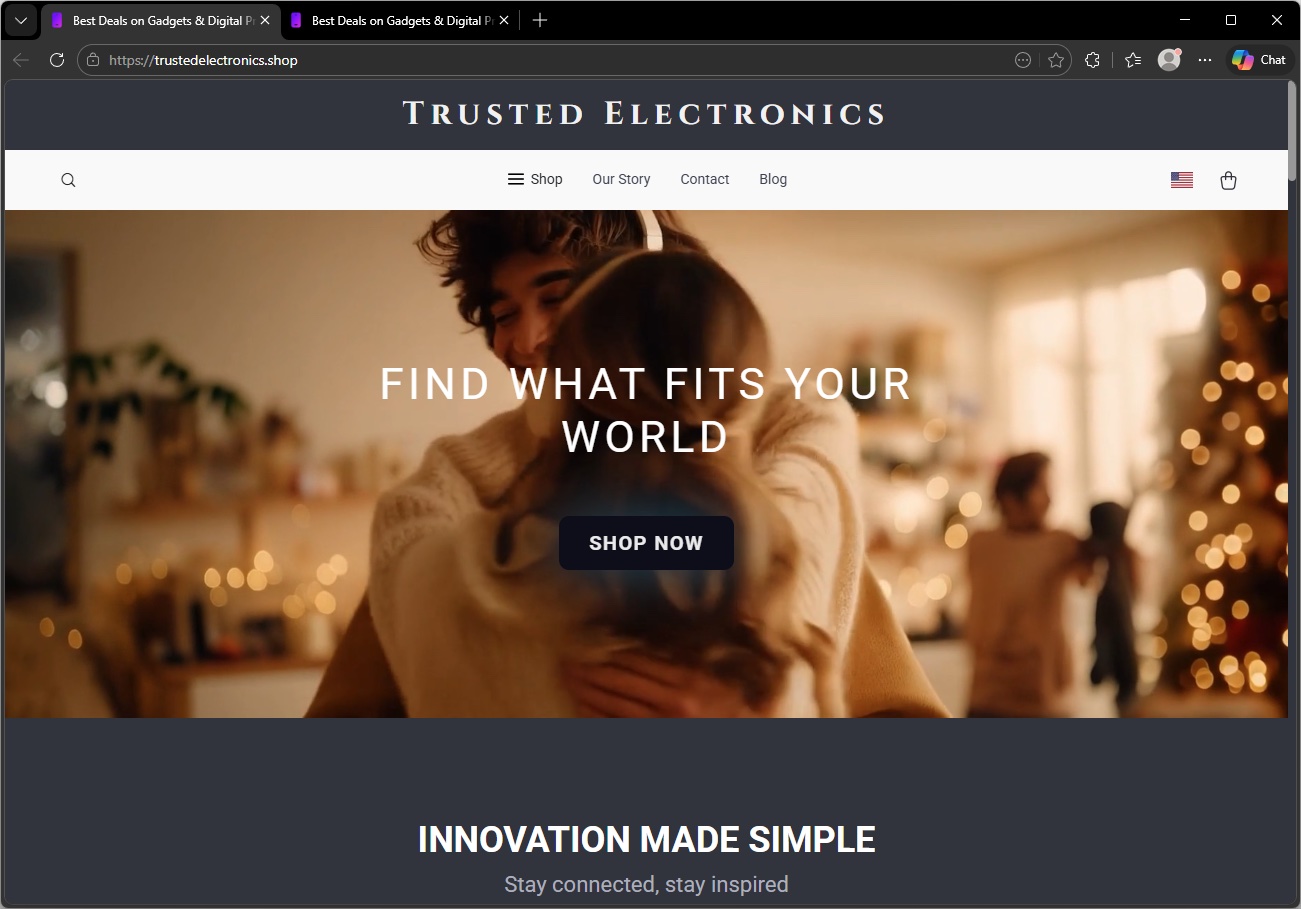
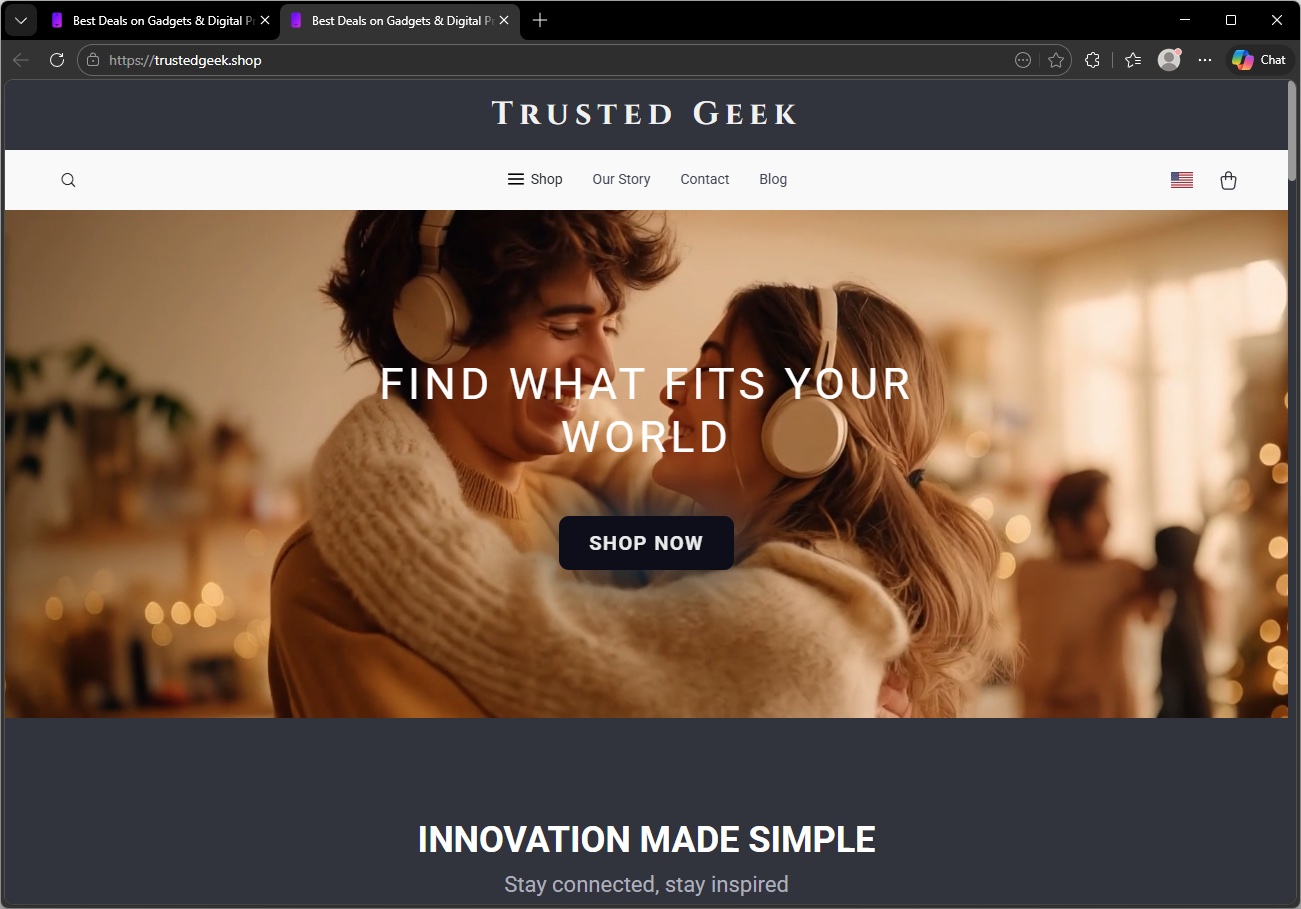
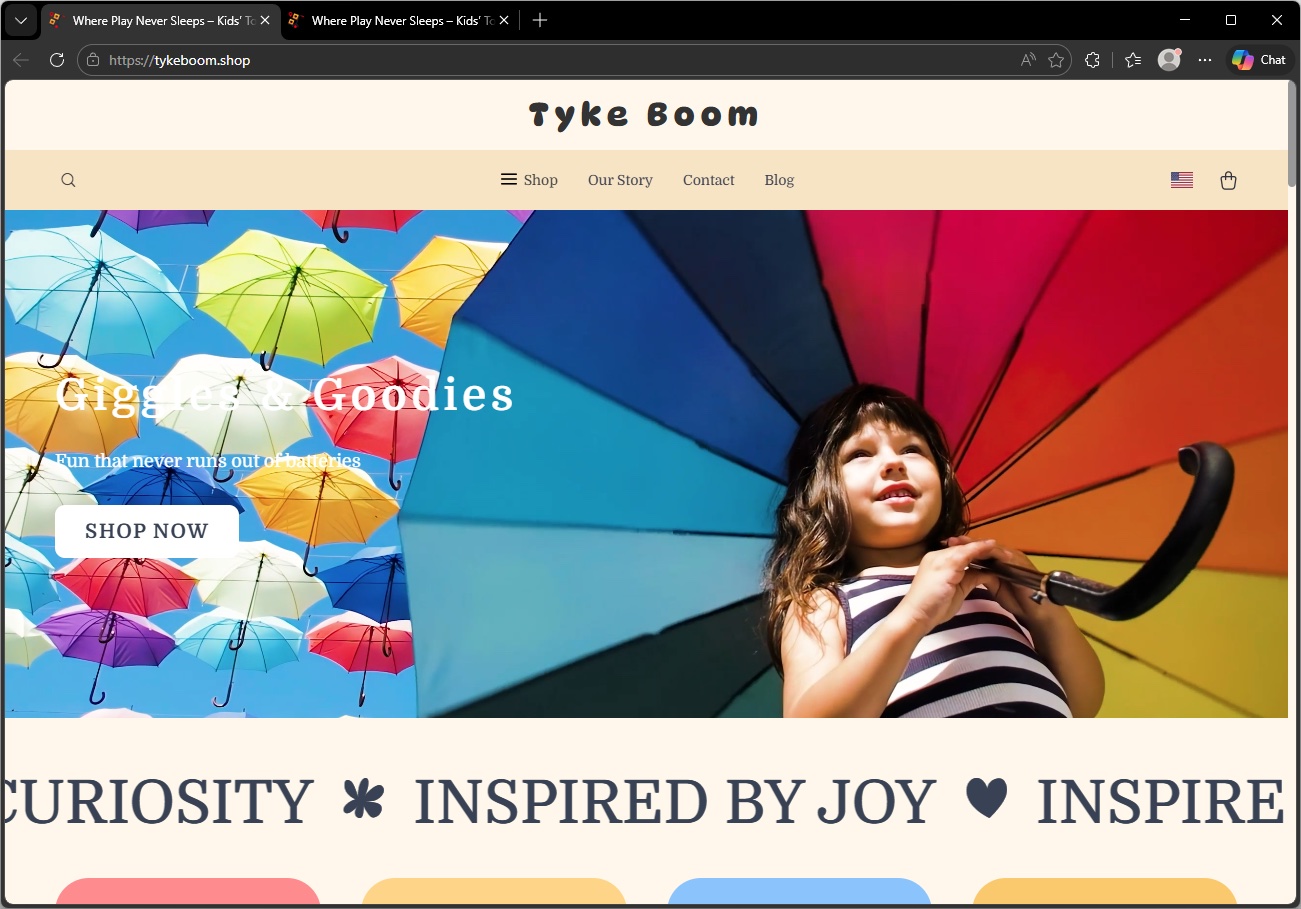
The storefronts reuse Sellvia’s themes and pull product images from its network. The six “different” templates we observed are really just two base themes with cosmetic variations. Here are some examples, shown in pairs to illustrate how the same template appears under completely different brand names.

20,000 domains, 36 IP addresses
Behind the visual similarities, these fake shops share a common infrastructure backbone. All 20,000+ domains resolve to a set of just 36 IP addresses.
That level of concentration isn’t typical for legitimate online retailers. It’s a hallmark of bulk fraud operations where one group manages the servers and templates while individual operators spin up domains on top.
Much of this activity clusters around a small number of IP ranges, including blocks in the 207.244.x.x and 23.105.x.x space. That clustering points to a preference for specific hosting providers, and a setup designed for speed: spin up a domain, attach a template, go live.
This mirrors the franchise-style model seen in other fake shop networks. A core group manages the servers, templates, and payment setup, while operators register domains and launch storefronts on top. When one site is flagged or taken down, another takes its place.
But the same clustering is also a weakness. Disrupt a small number of servers, and you can take thousands of sites offline.
How to stay safe from fake shops
These fake shops aren’t independent businesses. They’re part of large, repeatable operations designed to look convincing, move fast, and disappear just as quickly.
If a site feels unfamiliar, rushed, or too good to be true, treat it that way. A few extra seconds of checking can save you from handing over your money and your data to cybercriminals.
- Use browser protection. Tools like Malwarebytes Browser Guard can block known scam sites before you ever reach checkout.
- Check the domain carefully. Be cautious with unfamiliar endings like .shop, .top, .store, and .xyz, especially when paired with generic, brand-sounding names. If you’ve never heard of the retailer, that’s your first signal.
- Be skeptical of deep discounts. If an item is sold out everywhere else but heavily discounted on one unknown site, it’s bait.
- Watch for copy-paste storefronts. If multiple sites have identical layouts, product images, and banners under different names, they’re likely using the same template. Legitimate stores don’t operate like that.
- Look for independent reviews. Search the store name with terms like “review” or “scam.” If the only results are the site itself, that tells you something.
- Don’t ignore your instincts. If something feels off, stop. Don’t enter your payment details just to “see what happens.”
- Use safer payment methods. Credit cards offer better protection than debit. Virtual cards or payment services can add an extra layer between your details and the seller.
Pro tip: Malwarebytes blocks these domains as fraudulent.
Indicators of Compromise (IOCs)
IP addresses
- 108[.]59[.]1[.]151
- 108[.]59[.]12[.]118
- 108[.]59[.]14[.]13
- 108[.]59[.]8[.]97
- 108[.]62[.]0[.]220
- 108[.]62[.]116[.]82
- 108[.]62[.]117[.]45
- 162[.]210[.]195[.]105
- 162[.]210[.]195[.]113
- 162[.]210[.]198[.]37
- 162[.]210[.]199[.]12
- 162[.]210[.]199[.]183
- 162[.]210[.]199[.]235
- 192[.]96[.]200[.]81
- 198[.]7[.]58[.]168
- 198[.]7[.]58[.]87
- 199[.]115[.]115[.]2
- 207[.]244[.]102[.]13
- 207[.]244[.]109[.]109
- 207[.]244[.]126[.]106
- 207[.]244[.]126[.]19
- 207[.]244[.]126[.]21
- 207[.]244[.]67[.]158
- 207[.]244[.]69[.]201
- 207[.]244[.]71[.]143
- 207[.]244[.]89[.]198
- 207[.]244[.]91[.]203
- 23[.]105[.]160[.]43
- 23[.]105[.]172[.]14
- 23[.]105[.]8[.]15
- 23[.]105[.]8[.]17
- 23[.]105[.]8[.]19
- 23[.]82[.]11[.]26
- 23[.]82[.]13[.]161
- 23[.]82[.]13[.]34
- 5[.]79[.]69[.]45
Something feel off? Check it before you click.
Malwarebytes Scam Guard helps you analyze suspicious links, texts, and screenshots instantly.
Available with Malwarebytes Premium Security for all your devices, and in the Malwarebytes app for iOS and Android.