We’ve identified a huge social-engineering campaign designed to steer people into online gambling sites under the impression they’re installing a legitimate app.
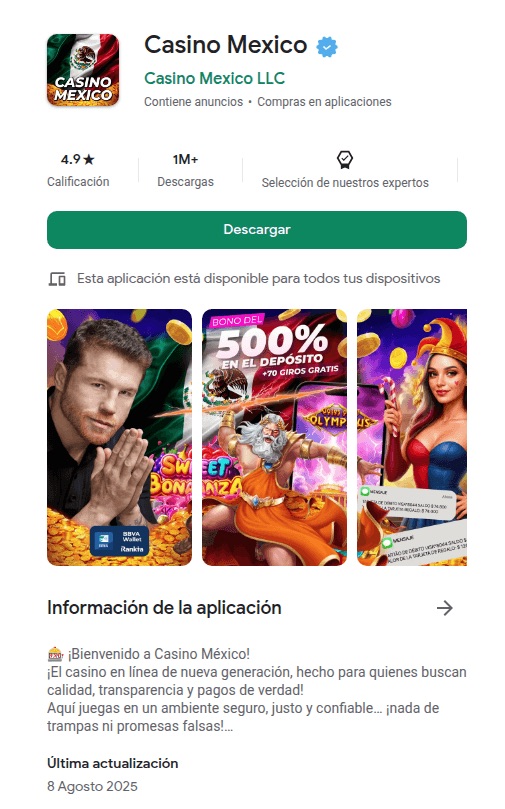
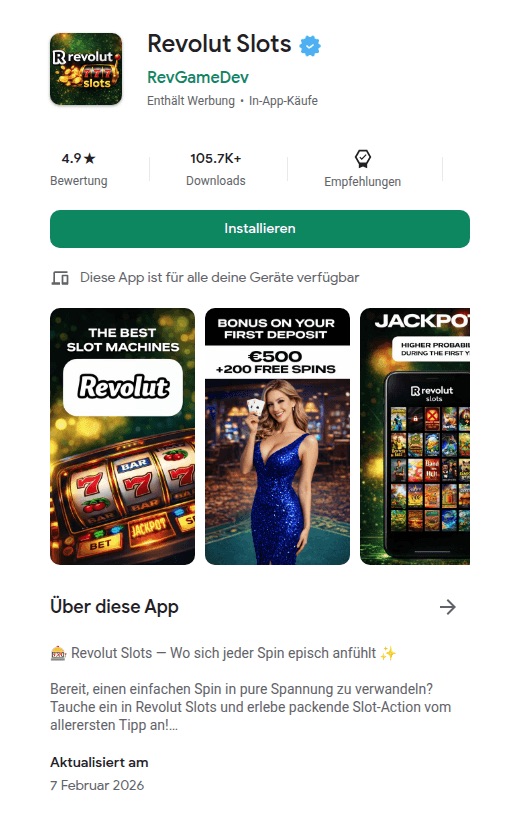
We’re calling it FriendlyDealer. It’s been observed across at least 1,500 domains, each hosting a website that impersonates the Google Play or Apple App Store. Users think they’re downloading a gambling app from a trusted source, with all the checks, reviews, and safeguards that implies. But they’re actually still on a website, installing a web app that then redirects them to casino offers through affiliate links.
The campaign doesn’t steal passwords or install traditional malware. Instead, it makes money through commissions every time someone signs up or deposits money at one of these sites.
That might sound less serious than a banking Trojan, but the end result is people being funneled into unregulated gambling sites with no age verification, no deposit limits, and no consumer protections. And it comes at a time when gambling addiction is being called the fastest explosion of gambling the country has ever seen.
One kit, dozens of apps, built to mimic real app stores
FriendlyDealer is built as a single, reusable kit that can generate many different fake app listings.
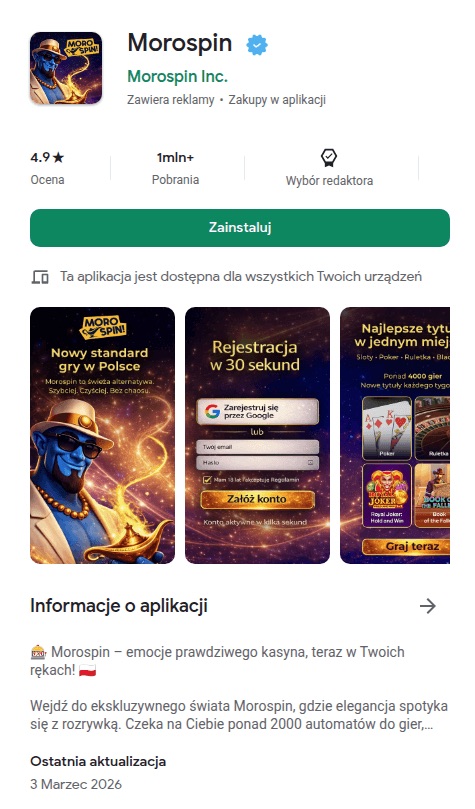
The kit detects what device you’re using and shows you a different fake store accordingly. Android users see a fake Google Play Store. iPhone users see a fake Apple App Store. The kit even loads the correct system fonts for each platform (Google Sans on Android, San Francisco on iOS) so the typography matches what you’d expect on your own phone.
Under the hood, it’s a single web application that reads all of its content from one configuration file embedded in the page. Change that file, and you get a completely different app listing running on the same code.
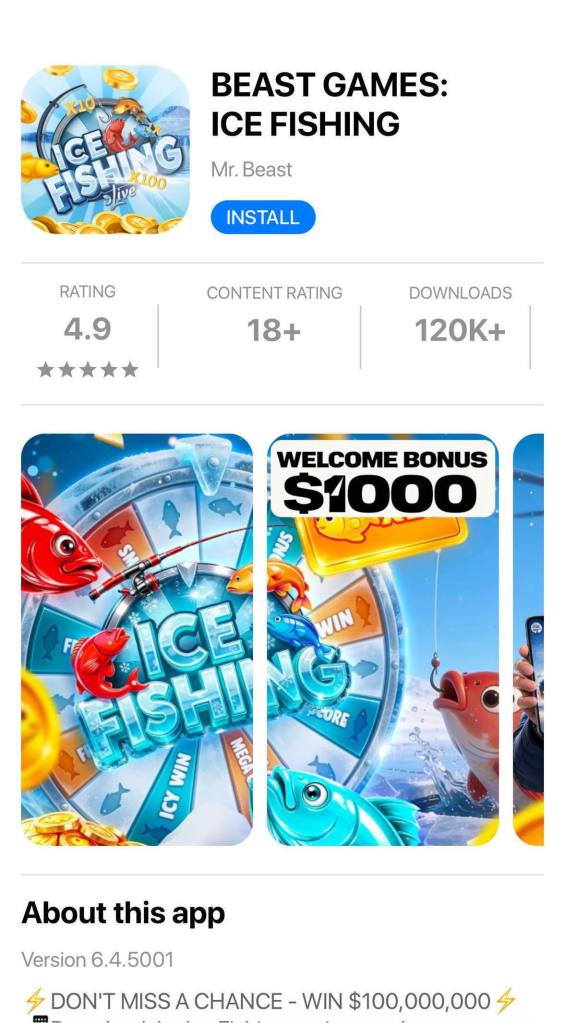
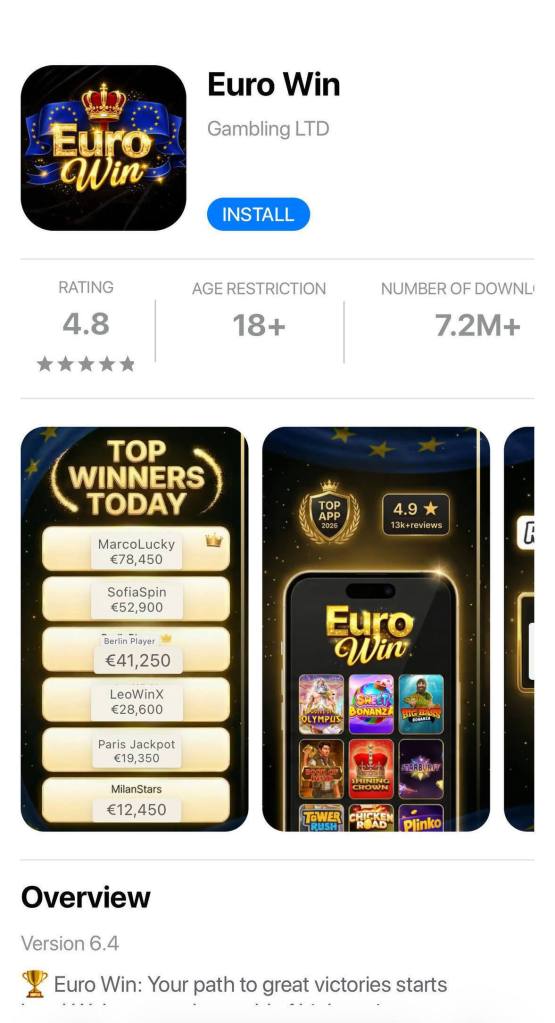
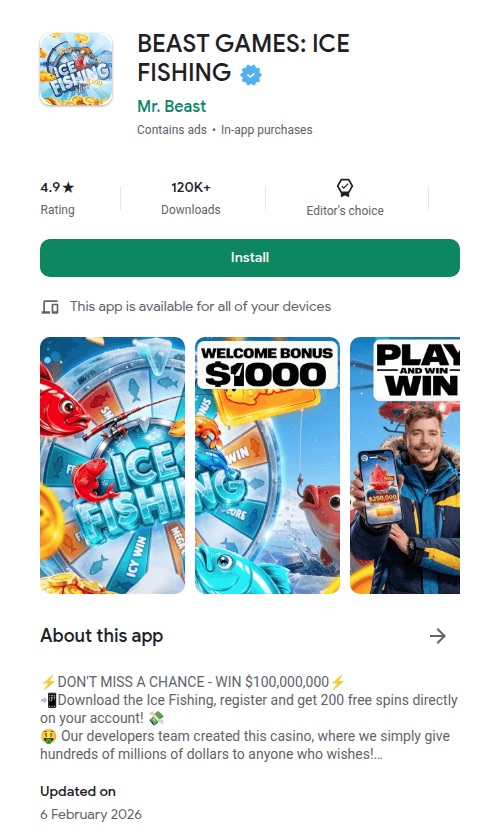
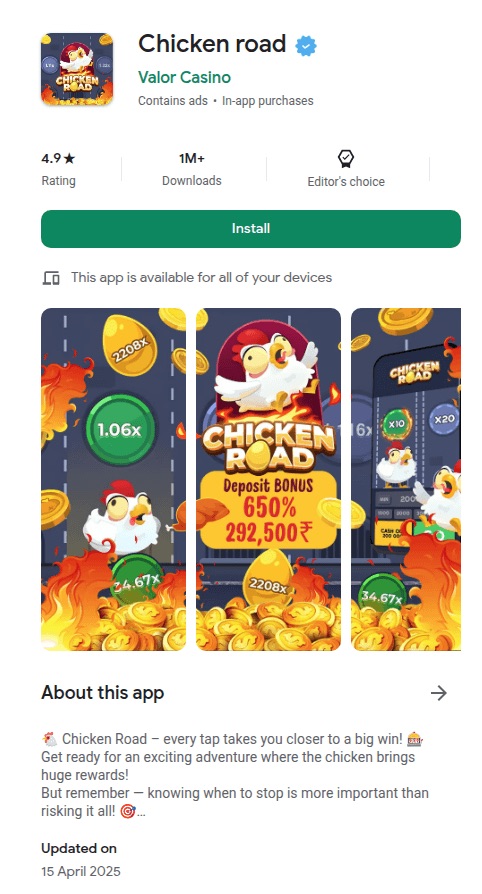
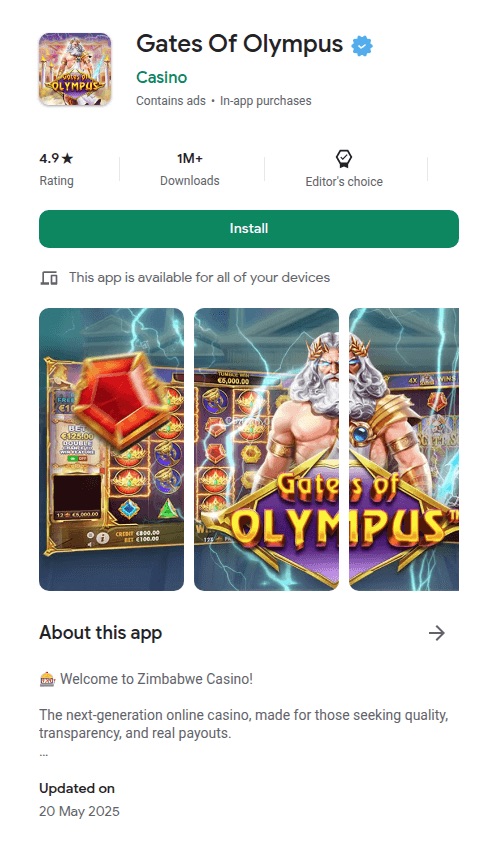
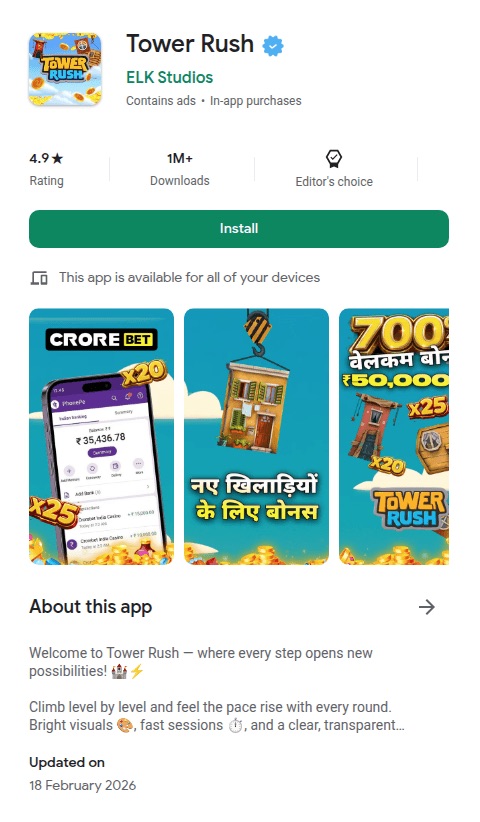
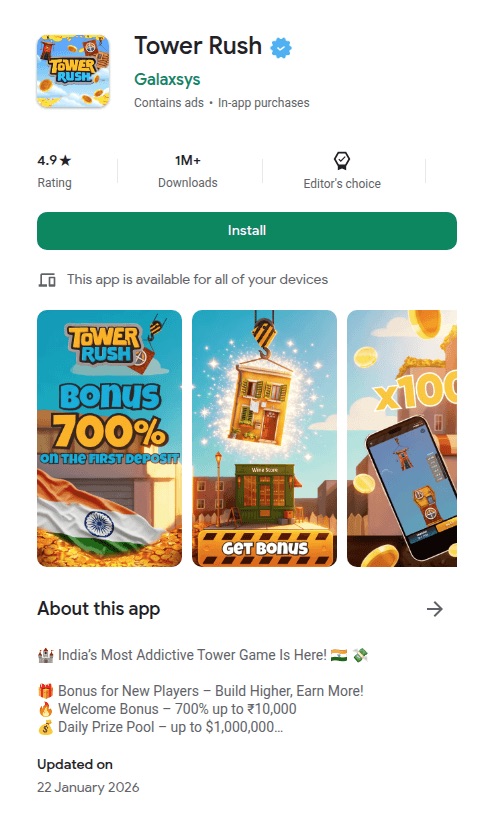
The operators have used this to spin up at least twenty casino brands, from “Tower Rush” (189 deployments) to “Chicken Road” (97) to “BEAST GAMES: ICE FISHING” (43), which impersonates YouTube creator MrBeast. (It’s worth noting that some skins reuse the names of some legitimate gambling brands but none of these are affiliated with the operation.)
The reviews are fake. Different apps reuse identical usernames, profile photos, text, and developer replies, and they’re repeated across multiple brands. Before showing the fake store, the kit can also display a simple casino mini-game to build engagement.
The fake “Install” button on Android relies on a Chrome feature that only works on mobile. It captures Chrome’s install prompt and triggers it when tapped, so a real installation dialog appears. The usual warning about installing apps from unknown sources does not appear. Previous research has shown that apps installed this way can even display “Installed from Google Play Store” in your phone’s settings.
The code goes to extraordinary lengths to get you into the right browser. If you arrive through a Facebook or Instagram ad, you’re inside those apps’ built-in browser, which can’t trigger the install. On Android, the kit generates a special link that forces the page to reopen in Chrome. On iOS, it does the same thing but for Safari. If Chrome isn’t installed, the fallback sends you to the real Play Store to download it. There’s even a separate handler for Samsung’s browser. The browser-specific engineering is unusually detailed.
The page disables zooming, making close inspection harder. The kit assigns a per-user tracking ID and reuses it across analytics, event, push-registration, and offer-routing flows.
The kit is wired for paid advertising. The configuration includes empty slots for tracking pixels from four ad platforms: Google, Yandex, Facebook, and TikTok. The app and background script can forward Facebook-style ad identifiers (_fbc / _fbp) when those values are available. The code references Yandex telemetry fields and ships with Russian-language comments and debug strings, which is consistent with a Russian-speaking development context, though those artefacts could also have been inherited from a reused or purchased kit.
The flow is straightforward: buy ad traffic, detect the device, show a fake app store, trigger a real-looking install, and redirect to a casino through an affiliate link.
You’re not installing an app
When a user taps Install, the page doesn’t actually download an app. Instead, the browser creates what’s called a Progressive Web App (PWA). It’s essentially a website that behaves like an app, with its own icon on your home screen and its own splash screen. To most people it’s indistinguishable from a real app.
Once installed, the app can keep running in the background using browser features called service workers (keeping a persistent connection to your device). The samples include the main PWA worker and code to register a separate push worker (to send you notifications) when enabled.
The kit also knows when you’ve already installed it. It checks your device for its own PWA, and if it finds it, it skips the fake store entirely and sends you straight to the casino.
One domain ties it all together
Every FriendlyDealer deployment phones home to the same domain: ihavefriendseverywhere[.]xyz. This is the campaign’s data-collection server, and the name that inspired our tracking name for the operation.
The background script and app code send telemetry to this domain including browser language, timezone, user-agent data, optional user-agent client hints, campaign identifiers, and ad identifiers when those values are available. Much of this is sent via custom request headers.
Some requests use the HEAD method to stay lightweight.
The application code also sends something the background script doesn’t: JavaScript error reports. Every crash, every failed resource load, every unhandled exception that occurs on the victim’s device is caught, packaged into a structured error object with a timestamp and context, and posted to ihavefriendseverywhere[.]xyz/api/log_standard_err. In effect, the operators are collecting both user data and production error telemetry from real devices.
If a request fails (for example, due to poor signal), the background script stores it locally and retries later. Once the connection returns, the data is sent automatically.
The fake app also asks for notification permission. If the user grants it, the kit can register a push subscription and create a direct channel for future notifications. These appear like normal app notifications, giving the operators a direct line back to the user even after the app is closed.
Follow the money: affiliate commissions, not malware
FriendlyDealer doesn’t spread viruses or take over devices. The entire operation runs on affiliate commissions. Each fake app store page contains a hidden redirect to an affiliate tracking network. When a user signs up or deposits money, the operator gets paid.
We found multiple affiliate tracking networks in the code. A per-user ID appears across the kit’s analytics, event, push, and offer-routing logic, allowing activity to be correlated across multiple stages of the funnel.
This model explains the campaign’s enormous scale. Each domain is disposable. The kit is a template; change one configuration file and you have a new casino brand on a new domain in minutes. With gambling affiliate payouts reportedly ranging from $50 to $400 per depositing user, even a small conversion rate across a thousand domains adds up fast.
Who’s behind this?
We can’t attribute the campaign to a specific group, but there are clues. The source code contains Russian-language comments (for example, “Создаем таймер для измерения времени загрузки Vue “). One of the builds shipped with unstripped Russian debug strings that were scrubbed from the production version. The code integrates with Yandex Metrica, which is popular in Russia and the former Soviet states.
These point to a Russian-speaking development context, although the code could have been reused or purchased.
The code also contains affiliate marketing tags—preland-alias and preland-final-action—where a “pre-lander” is the page a visitor sees before the actual offer. The application code shows this tag controls the kit’s behavior: a value of 0 triggers a PWA install, while 1 redirects to an app store. Combined with plug-and-play ad pixel slots, per-deployment configuration, and staging/production logic, this strongly suggests a reusable kit built for multiple campaigns or operators, not a one-off project.
We found multiple builds of the same kit. The production version has debug messages removed, but other builds include full Russian-language error messages and support for Arabic numerals across the interface—download counts, ratings, review dates, and more. This does not look like a kit built for a single market; it appears designed to support regional variants at build time.
A familiar trick with a different payoff
Fake app store pages are a known technique, often used to steal banking credentials or deliver spyware. FriendlyDealer uses the same playbook, a convincing fake store and a real-looking install flow, but with a different goal. It doesn’t take over your phone or steal your passwords. It steers you toward gambling platforms and earns a commission when you spend money.
The harm is financial rather than technical: victims are funneled toward gambling offers through deceptive install and redirect flows, and may end up depositing money at sites they did not intentionally choose.
It’s also s a reminder that not every scam is after your passwords. Affiliate fraud, especially in online gambling, can fund enormous operations without ever touching a single credential. The people behind this built a factory: one template, twenty brands, more than 1,500 domains. Paid ads bring the traffic. The fake app stores seal the deal. The affiliate network pays the bills.
What makes this effective is that it abuses things that are supposed to be trustworthy. Chrome’s app installation flow on Android and Safari’s “Add to Home Screen” on iPhone are both legitimate features, doing what they were designed to do. The problem is that the page triggering the install is a lie. The kit is carefully engineered so only the right users, on the right devices, coming from the right ads, ever see it.
What to do if you installed one of these apps
On Android:
- Remove the app: Long-press the icon and tap Uninstall, or go to Settings > Apps and remove anything you don’t recognize.
- Clear the site data in Chrome: The app may leave data behind in your browser. Open Chrome > Settings > Site settings > All sites, find the site, and tap Clear & reset.
- Check notification permissions: Go to Chrome > Settings > Notifications and remove any sites you don’t recognize. Uninstalling the app does not remove notification access.
- Check other browsers: If you use Edge, Brave, or another Chromium-based browser, repeat the same steps there.
On iPhone:
- Remove the app: Long-press the app icon on your home screen and tap Remove App. On iOS, PWAs don’t install a background script the way they do on Android, so removing the icon also removes the cached site data.
- Clear the site data in Safari: Go to Settings > Safari > Advanced > Website Data, and search for the domain. Swipe to delete it. This clears any remaining cookies and stored data.
- Check notification permissions: Go to Settings > Apps > Safari. Scroll to the Settings for Websites section and tap Notifications. Find the site and remove or deny access.
If you deposited money after being routed through one of these pages and believe you were deceived, contact your bank or payment provider promptly.
Indicators of Compromise (IOCs)
Domains
ihavefriendseverywhere[.]xyz—Data exfiltration and error-logging servervalor[.]bet—Gate/checkpoint URL (/__pwa_gate path)wikis[.]lifestyle—Hardcoded domain reference in application code
Scammers know more about you than you think.
Malwarebytes Mobile Security protects you from phishing, scam texts, malicious sites, and more. With real-time AI-powered Scam Guard built right in.