Malwarebytes welcomes and encourages independent researchers reporting vulnerabilities in our products, and has run a bug bounty program for several years.
Our security team has spent the last few months modernizing the program and we thought you’d like to hear about it.
What is a bug bounty program?
To encourage everyone to share security vulnerabilities in a responsible manner, a bug bounty program provides an official procedure for informing a company about vulnerabilities in its products and services. It often consists of the following steps:
- A researcher submits a report about a security vulnerability
- The vendor’s security team triages the report and reaches out to the researcher
- The vendor creates a fix, which is shared with the researcher for validation
- The security team rewards the researcher according to the severity of the vulnerability
This process can be complex, time consuming, and prone to errors. That’s why the reward is important: It incentivizes everyone to work towards the same goal, and places a value on the researcher’s time and skills.
Increased bounties
Our bug bounty program was launched in 2017 and to date it has allowed us to fix 133 vulnerabilities in our products: Four critical, 46 high, and 83 informative, and we have awareded $47,435 to 115 external researchers!
We regularly update the rewards we offer, and we recently increased them again. The scale now offers up to $5,000 for a critical vulnerability. (And we may consider increased amounts on a case-by-case basis.)
| Severity | Reward scale | |
|---|---|---|
| Critical | $2,000-$5,000 | |
| High | $500-$2,000 | |
| Medium | $100-$500 | |
| Low | $20-$100 | |
Submitting a vulnerability report
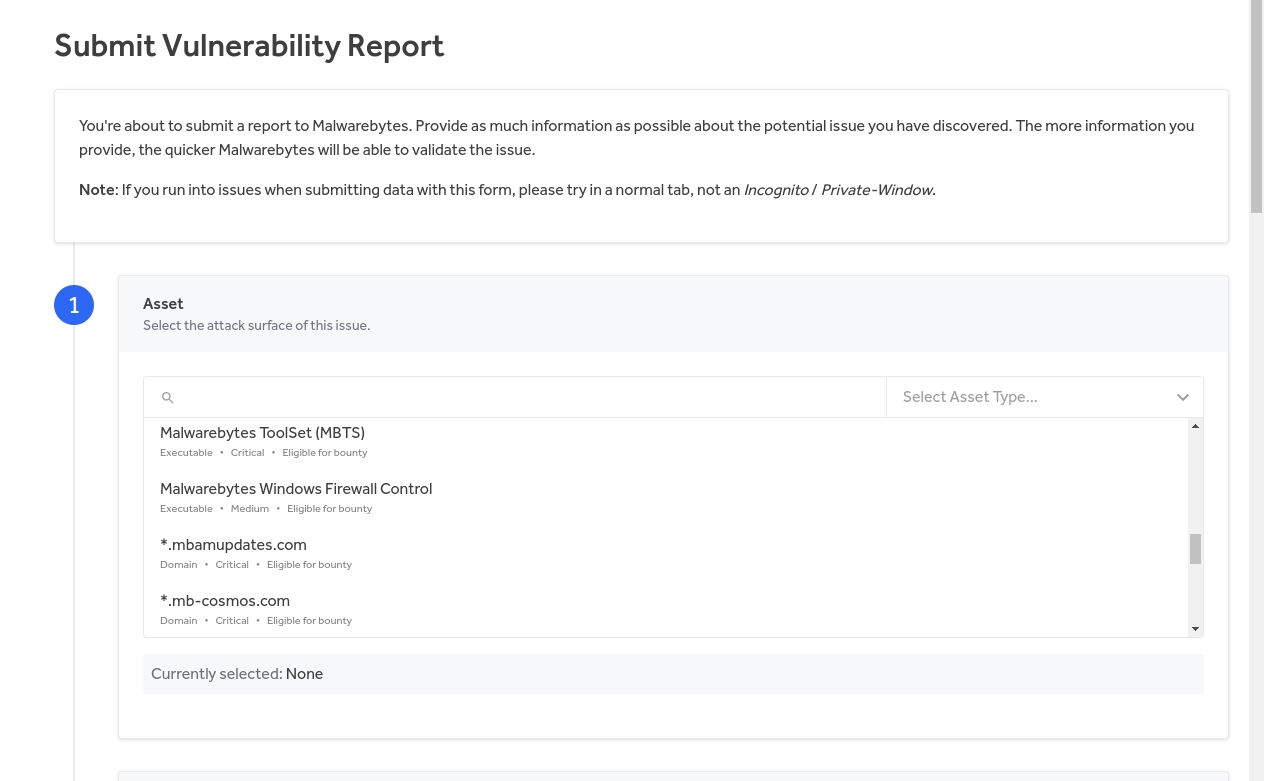
To ease the complex bug bounty process, we rely on HackerOne, which provides an interface between researchers and our security team. We have deprecated the email address we previously asked researchers to use and replaced it with a vulnerability disclosure form on our website.
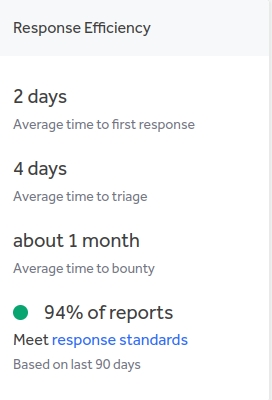
This change has improved our response efficiency to two days, and we’re working on getting that even lower:
security.txt
To make it easier to submit security vulnerabilities online, we now use the security.txt file standard defined by RFC, 9116. Malwarebytes has many different online services, and we needed an easy, standardized way for researchers to reach us.
The RFC defines a machine-parsable file called security.txt that describes a vendor’s vulnerability disclosure practices.
We are in the process of deploying a security.txt file to all of our web endpoints, either at /security.txt or at
/.well-known/security.txt- https://cloud.malwarebytes.com/.well-known/security.txt
- https://adwcleaner.malwarebytes.com/security.txt
Our security.txt documents contain a link to our vulnerability disclosure form at https://malwarebytes.com/secure; our careers page; our bug bounty policy; our preferred language, and an expiration date.
This standard has been adopted by many prominent companies already, including the likes of Google and GitHub, and we have high hopes that it will help researchers navigate our bug bounty program more easily.
In security, we believe deeply that collaboration is key. The changes we have made to our bounty program over the last few months are made with this motto in mind, and we look forward to receiving your reports!











