Ramnit.Virus.FileInfector.DDS
Short bio
Ramnit.Virus.FileInfector.DDS is Malwarebytes’ detection name for a family of viruses detected by Malwarebytes’ Katana engine. Ramnit is a versatile family that holds viruses, worms, and Trojans. They are capable of infecting EXE, DLL, and HTML files on an affected system.
The detection names are produced by Malwarebytes 4 and Malwarebytes business products. These generic malware detections are due to our new automated signature system called BytesTotal and specifically the DDS engine that are based on Machine Learning technology with 100% autonomous learning which don’t require any human interaction to correctly identify malware. These techniques are part of Malwarebytes’ Katana engine and were developed for automated mass detection of wide ranges of malware and adware.
Type and source of infection
Ramnit searches local and removable drives for suitable files which are then infected by adding a new section that contains the virus code. Ramnit is often spread via malspam campaigns and infected removable drives.
Aftermath
After removal of the infected files the system may be missing vital files for programs to run, which often makes a re-format of the system necessary. All removable drives that have been used on an infected system should be checked for the presence of the virus as well.
Protection
The Malwarebytes’ Katana engine detects unknown threats as Ramnit.Virus.FileInfector.DDS by using generic detections, Machine Learning, and other Artificial Intelligence techniques to protect users from malware.
Home remediation
Malwarebytes can detect and remove Ramnit.Virus.FileInfector.DDS without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
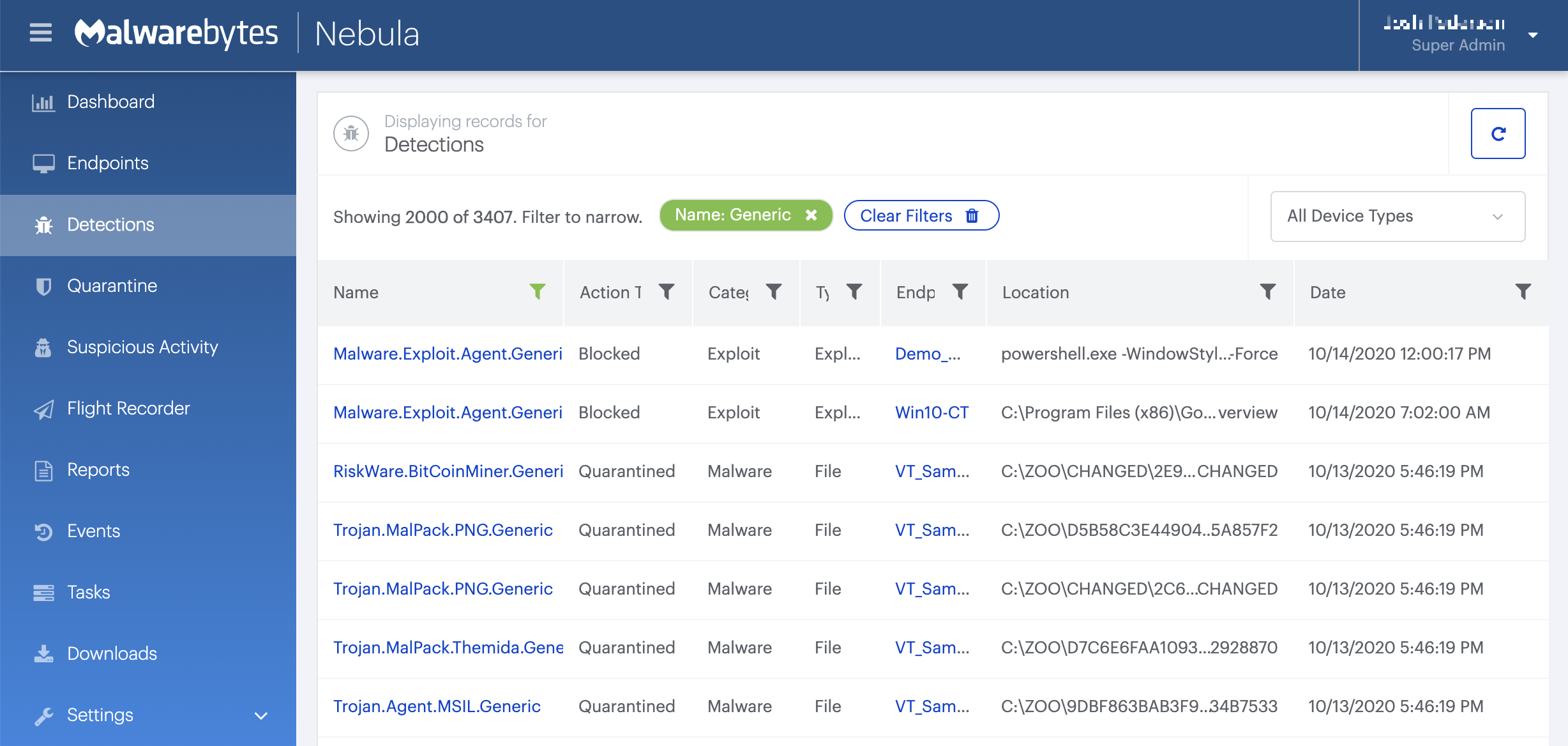
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
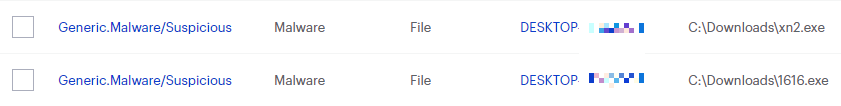
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.