Worm.Forbix
Short bio
Worm.Forbix is Malwarebytes’ detection name for a specific worm that is written in Visual Basic. Worms automatically spread to other PC’s and other connected devices by copying themselves to removable drives, network shares, and other protocols such as IRC and email.
Symptoms
Worm.Forbix may run silently in the background and may not provide any indication of infection to the user. Worm.Forbix will seek out connected devices and attempt to copies itself to any system found. Worm.Forbix may create shortcut files (.lnk) using a naming convention similar to files found on the infected system. Shortcut files created by Worm.Forbix will contain the malware code and will be used to infect future systems and devices.
Type and source of infection
Worm.Forbix may be distributed using various methods. This software may be spread through USB devices or any connected network device. This software may be packaged with free online software, or could be disguised as a harmless program and distributed by email. Alternatively, this software may be installed by websites using software vulnerabilities. Infections that occur in this manner are usually silent and happen without user knowledge or consent.
Protection
Worm.Forbix is a detection-only rule since the worm is no longer actively spread and the C2 servers are down. Despite this it still manages to show up now and then.
Home remediation
Malwarebytes can detect and remove many Worm.Forbix infections without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get started button.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Worm.Forbix with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
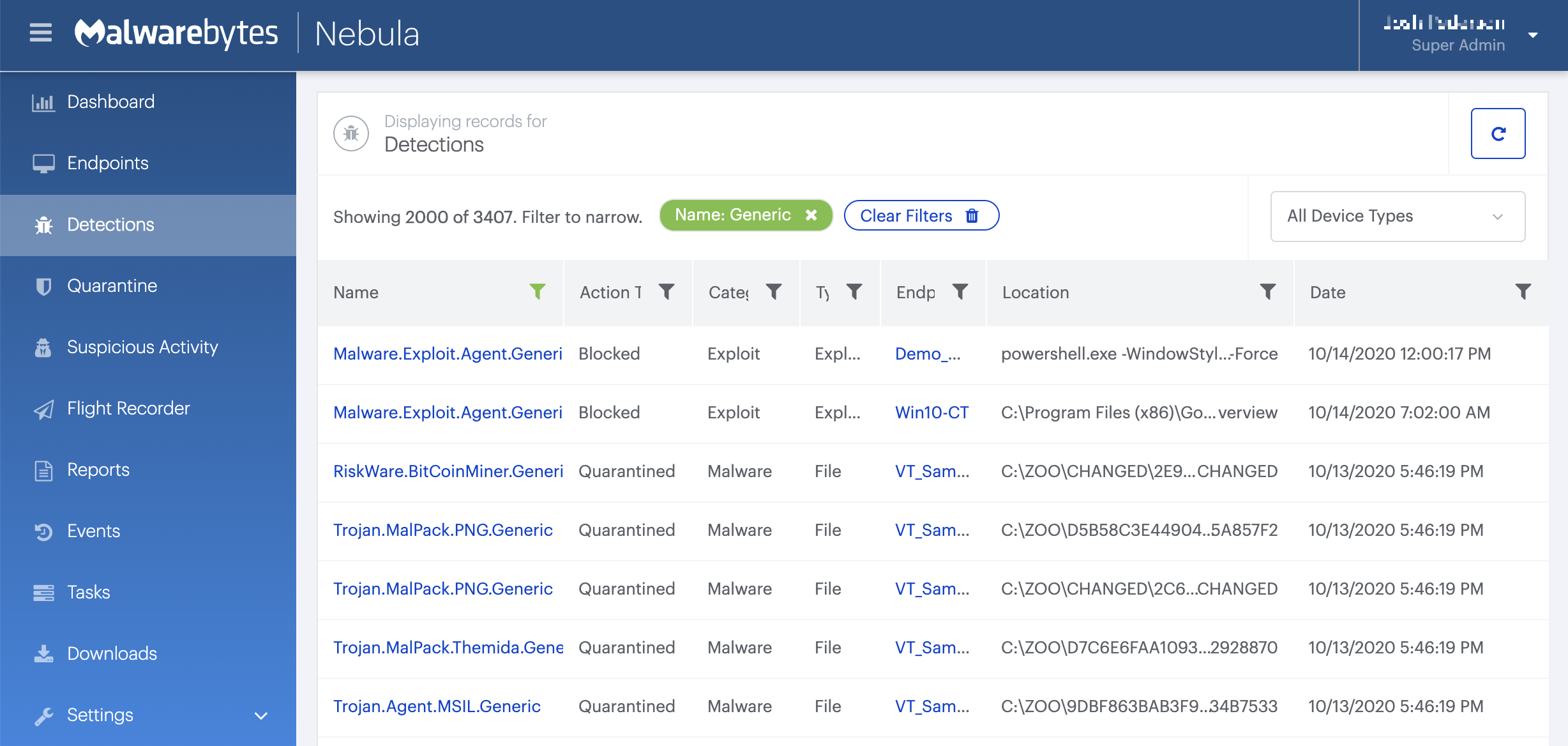
On the Quarantine page you can see which threats were quarantined and restore them if necessary.