About one year ago, Malwarebytes gained a new weapon in the fight against cyber-crime to accomplish things it had not been able to before, by releasing a tool known as “Chameleon”. Since then, very few changes have been made to the tool in helping it continue to evade the offensive efforts of malware against Malwarebytes software. In this blog post, we will look back at what Chameleon is, why it was necessary to create it and what changes we have made to it over the last year. In addition, we will also go over some of the inspiration that Chameleon has given us and how it is going to affect the fighting power of Malwarebytes in the future.
Chameleon
For those of you who do not know, Chameleon is a tool designed by the same people who brought you Malwarebytes Anti-Malware. It was developed to fight back against malware that tried to block Malwarebytes Anti-Malware from doing its job. Malware accomplished this by killing the process of Malwarebytes Anti-Malware or modifying the scanners ability to detect malicious files.
Once the developers and researchers here at Malwarebytes realized what was going on, development began on what would later become Chameleon. Chameleon uses various tactics of self-protection, file renaming and other sneaky tricks to make Malwarebytes Anti-Malware invisible from the malware trying to stop it. It is truly a tool that was well thought out and developed with an eye towards the future and has stood the test of time.
Chameleon has been included with every version of Malwarebytes Anti-Malware from 1.60. It is also available as a stand-alone application through our website, just in case malware prevents you from installing Malwarebytes Anti-Malware. To find out more about Chameleon and the story of its origin, check out the blog post from our VP of Development, Doug Swanson: “The Cat-and-Mouse Game: The Story of Malwarebytes Chameleon”
Obstacles
The adaptations we’ve had to make in order to keep Chameleon effective as a countermeasure against the nastiest threats that try and try again to prevent Malwarebytes Anti-Malware from running have been surprisingly few, illustrating just how novel and effective this tool really is.
One such nasty threat took place several months ago when some malware began using new types of functions to disable Chameleon by modifying certain policies from the system registry. The result was effectively blocking Chameleon from activating and allowing the malware to disable the Anti-Malware scanner. Once this threat was discovered, Malwarebytes developers modified Chameleon to overcome this one flaw. Since then, Chameleon has been incredibly resilient and will continue to evade the offensive functions of old and new malware.
Inspiration
A few weeks back, I discussed our newest tool in the fight against malware Malwarebytes Anti-Rootkit, or MBAR, one of our most ambitious projects to date, which is designed to go after infections so nasty that many anti-malware tools will not even touch them. The idea for MBAR actually stemmed from the work on Chameleon, due to its purpose of keeping our malware fighting methods relevant to the newest and most dangerous types of malware currently in the wild.
Likewise, we learned that malware was now using a combination of infection vectors to compromise systems and keep them infected, one of the most prevalent of which was rootkits. The rootkits were becoming increasingly common, even alongside threats we had not previously seen them bundled with, threats such as rogue/fake AVs/Trojans and other malware of almost every type. This meant that once again, in order to remain effective, our company would need to adapt, thus Malwarebytes Anti-Rootkit was born.
This parallels how we address Malwarebytes Anti-Malware itself, constantly adapting to change in the threat landscape and trying to stay a step ahead of the bad guys through the use of heuristics, threat analysis and forecasting potential future attack vectors and methods that the bad guys might use, even if they aren’t already. This same line of thinking affects everything from the engine of Malwarebytes Anti-Malware and the database it uses, the real-time protection module with its malicious file execution blocking and malicious website blocking and all the other technologies and products that we have planned for the future. We want to continue to make our name by using clever tactics and brilliant developers and researchers to be proactive by attacking the latest threats, no matter what form those threats might take.
How to use Chameleon
While all up-to-date versions of Malwarebytes Anti-Malware include Chameleon already built-into the application, the problem of being unable to install Malwarebytes Anti-Malware still exists for users who have not been using our product. To counter this threat, the stand-alone Chameleon download will install Malwarebytes Anti-Malware and scan the system to free it from the grips of malware. Here is a quick tutorial on how to use Chameleon on its own:
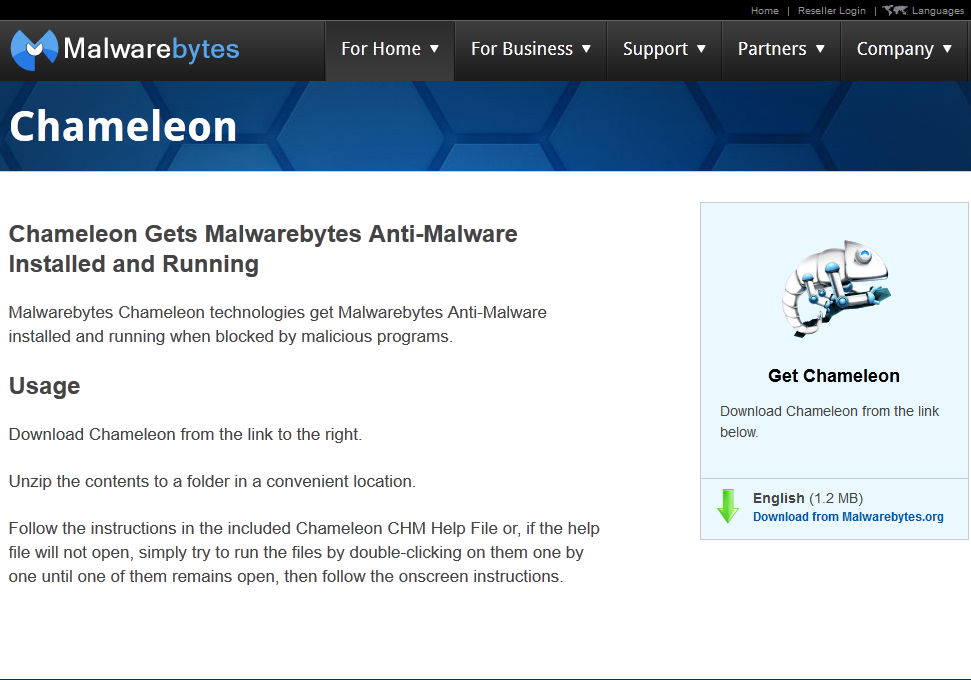
1. First, go to Malwarebytes.org and select the “Other Tools” option from the “For Home” Menu.
2. Next, select the option for Chameleon and download the ZIP.
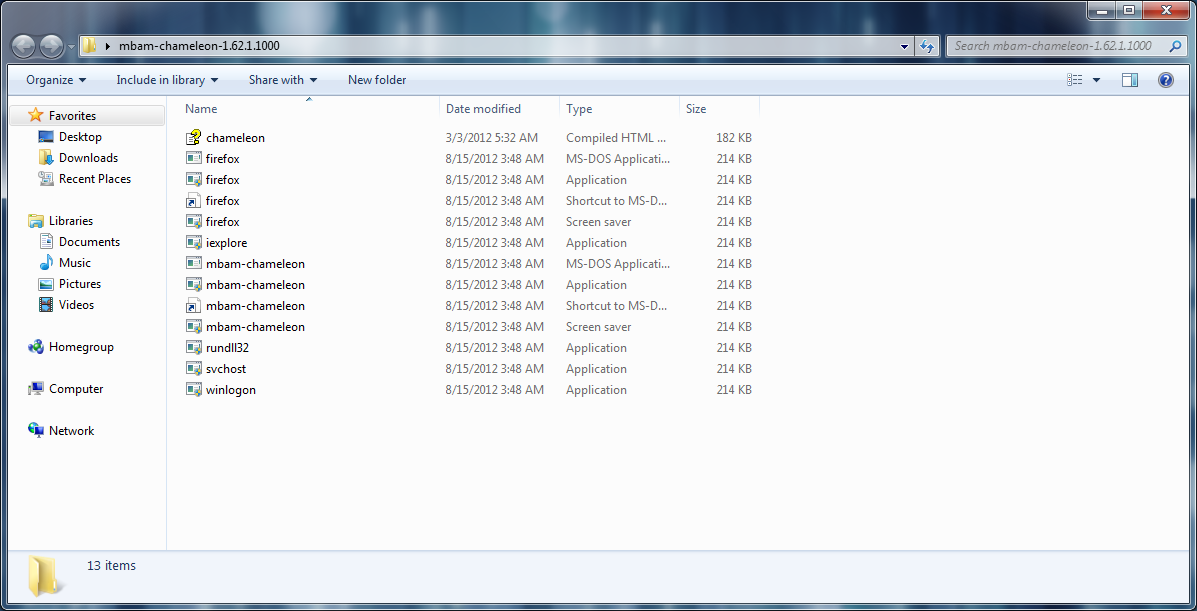
3. Unzip the contents somewhere like your Desktop, when done you should see something like this:
4. Click on the “Chameleon.chm” file to open up the Help interface and get you started.
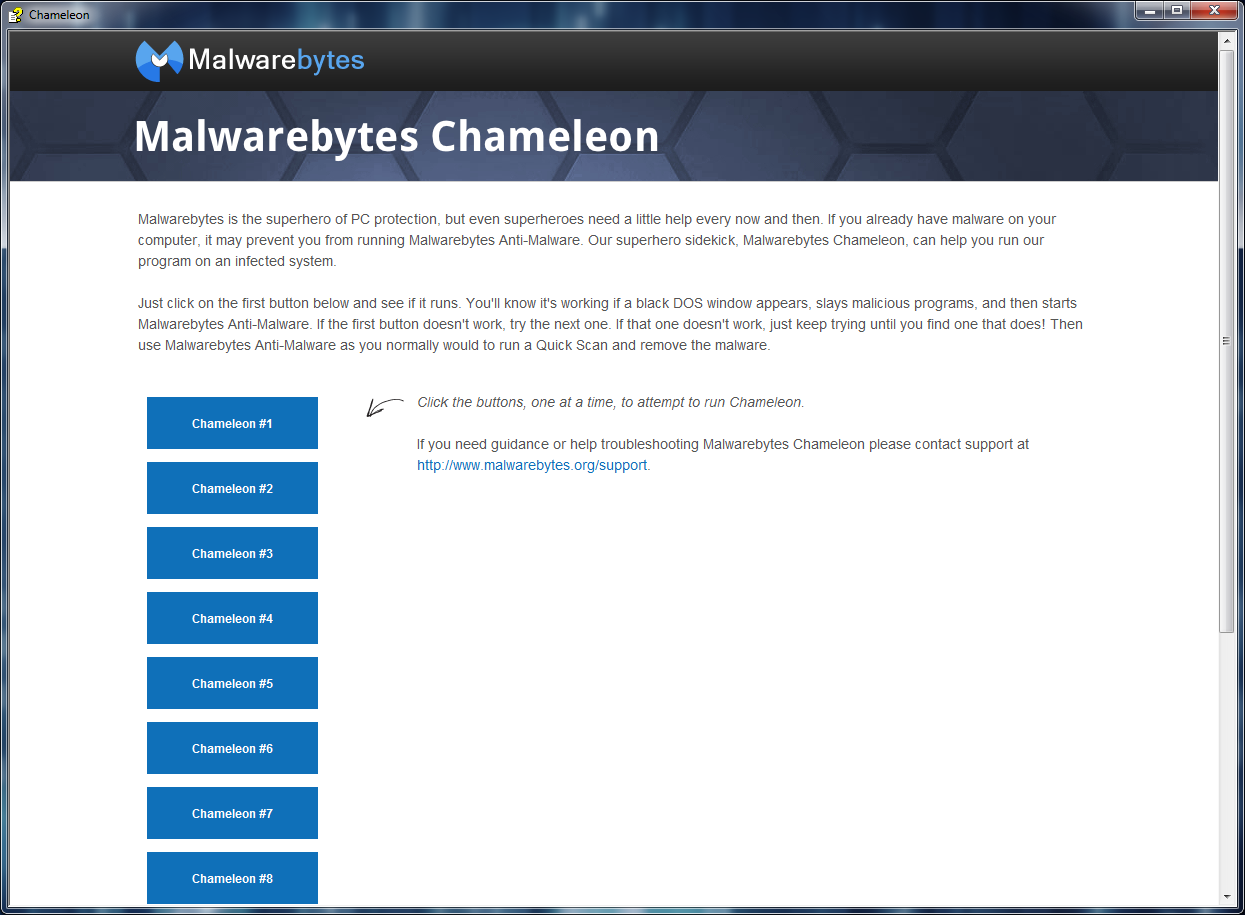
5. Once opened, read the help file text and then click down the line of Chameleon install attempts. The purpose of this is to try starting Chameleon from different angles to avoid a single executable being blocked.
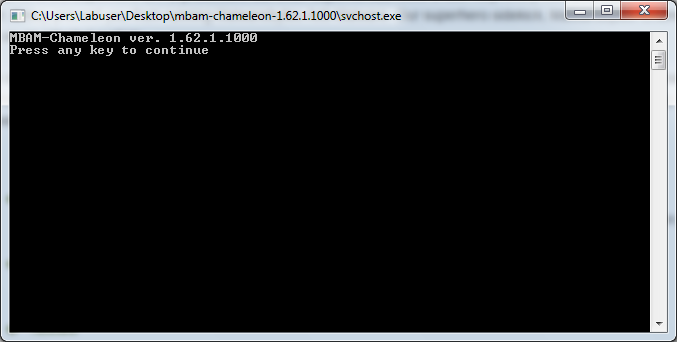
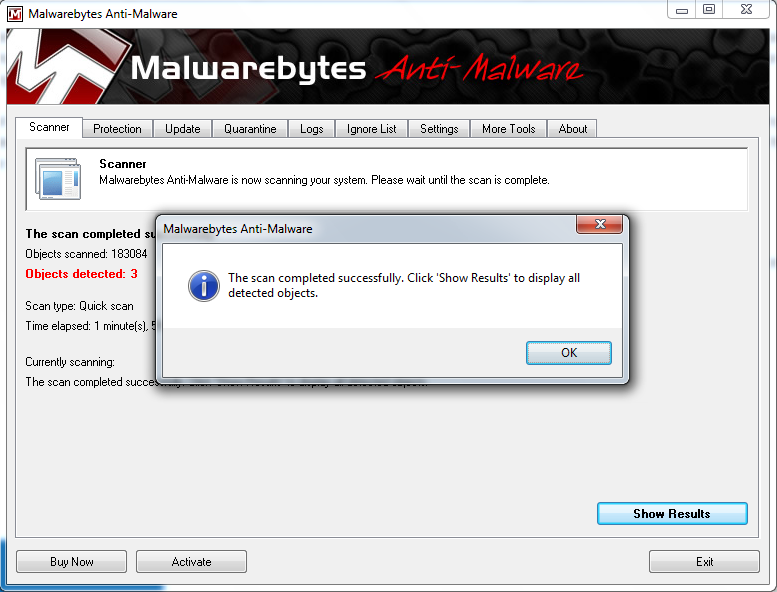
6. You should see something like this when Chameleon has successfully started up:
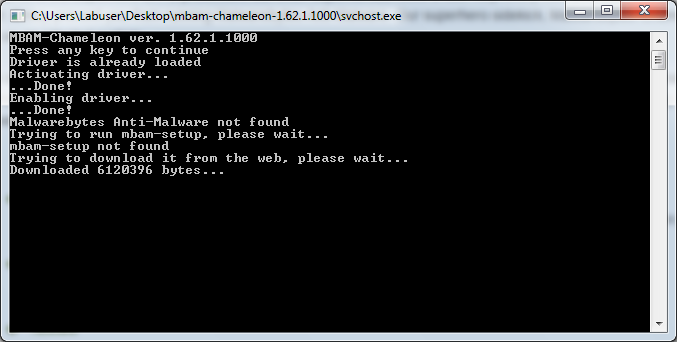
7. Once you ‘Press any key’ then Chameleon will start doing what it does. Firstly, it will try to download Malwarebytes Anti-Malware for you.
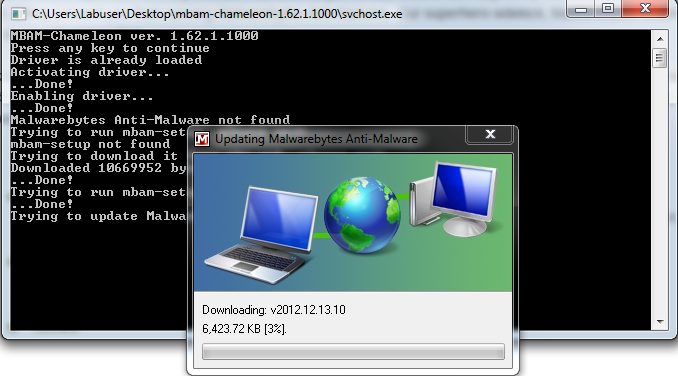
8. Once downloaded, it will try to update the Malwarebytes Anti-Malware definitions.
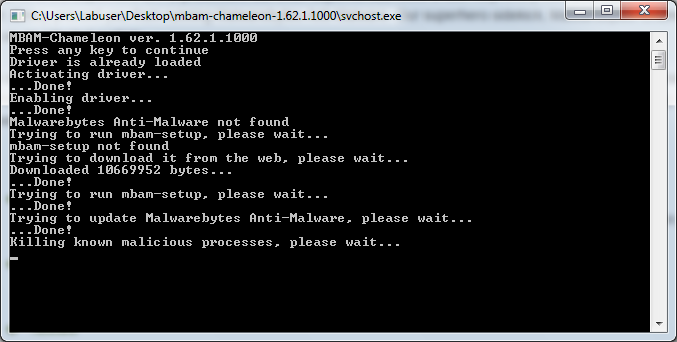
9. Next, it will kill any malicious processes that prevent Malwarebytes Anti-Malware from running.
10. Finally, it will start up the Malwarebytes Anti-Malware interface and run a scan to remove the malware.
Using Chameleon on the go
If you find yourself with lots of friends or family who get infected with malware all the time and constantly ask you or someone you know to help them out, here is a great way to quickly get them back on their feet using Chameleon.
- Download the Chameleon ZIP
- Unzip the files
- Download the Malwarebytes Anti-Malware setup executable from Malwarebytes.org
- Copy the Malwarebytes Anti-Malware setup file into the Chameleon Folder
- (OPTIONAL) Do the same for Malwarebytes Anti-Rootkit.
- Save the folder to a USB stick
Now you can use that USB stick to copy the Chameleon files to the infected system and run Malwarebytes Anti-Malware, even if the user cannot access the internet.
Conclusion
Over the last year, we have developed, tested and improved on multiple products including Chameleon, Malwarebytes Anti-Rootkit and even the original Malwarebytes Anti-Malware. In doing so, we have drawn inspiration from not only the malware we fight but also our community of users and cyber threat fighters who assist us every day in making the internet a safer place. Looking to the future, we have amazing new applications on the horizon and new functionality for the tools you already know and love that will make your computing experience even safer than it was before. The year 2013 should be a great one in the fight against malware so stay tuned and safe surfing!