Security researcher Kafeine has discovered a Zero-Day in Adobe Flash Player distributed through the Angler Exploit Kit. An Oday is an exploit for a vulnerability that has not been patched yet, meaning that even the most up-to-date systems could get infected.
[Edit: the vulnerability has now been assigned CVE-2015-0311]
Flash has been plagued with critical vulnerabilities in the past few months and surpassed the no longer popular Java as the most exploited plugin.
We immediately got our hands on this new Zero-Day (thanks Kafeine) and were able to replay it as well with the goal of testing our Anti-Exploit product:
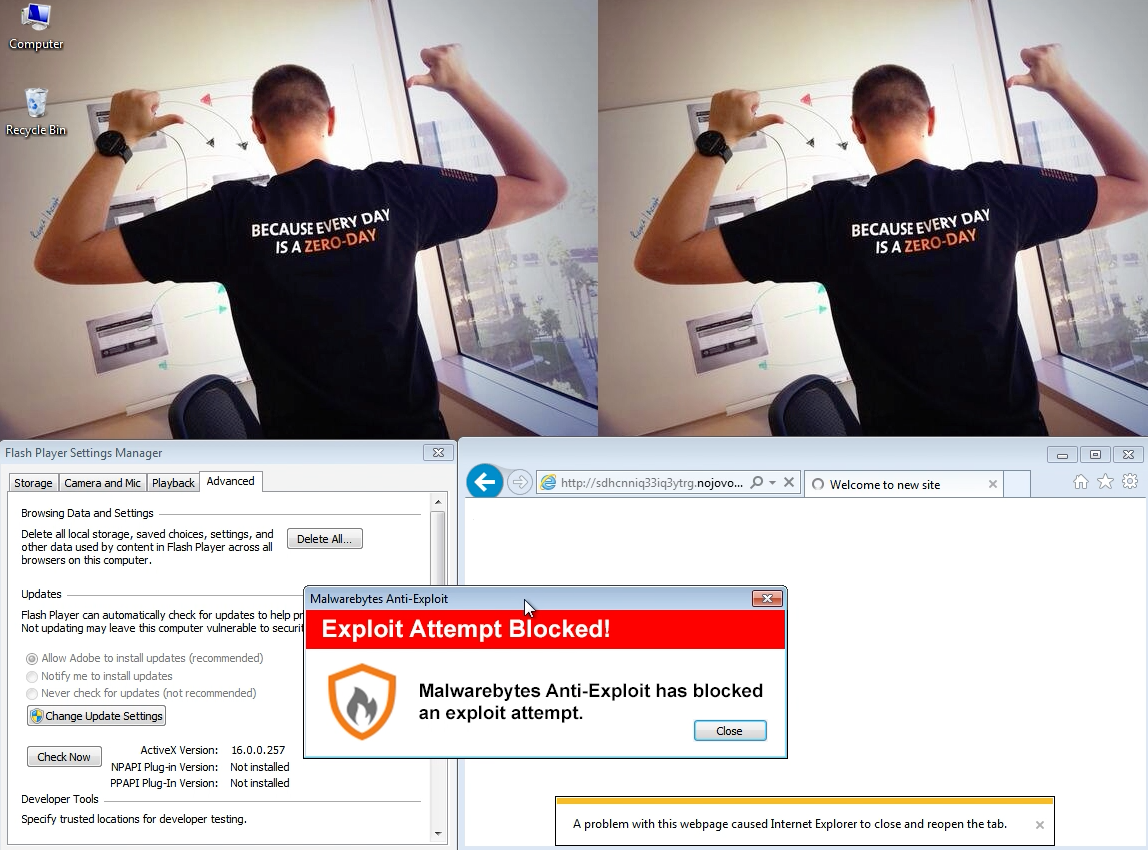
With the latest version of Internet Explorer (IE11) and latest version of Flash (16.0.0.257), the exploit was successfully blocked by Malwarebytes Anti-Exploit.
On unprotected machines, the Angler Exploit Kit will install Bedep, a distribution botnet that can load multiple payloads on the infected host.
As this is a breaking story, we are still analyzing the exploit and will update this post later accordingly.
Update: 01/21/15: Some details about the malware payload.
The payload in this particular instance was ad fraud. Upon infection, explorer.exe (not to be confused with iexplore.exe) is injected and performs the ad fraud calls.
The following Fiddler capture shows how a zombie PC is gaming the ad networks with bogus requests without the victim’s knowledge:
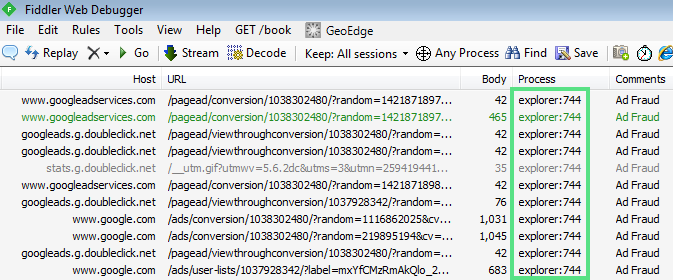
Unfortunately it is very hard to tell apart real users from fake ones and advertisers essentially end up paying for “impressions” or “clicks” where a human being was never involved.
Update(2): 01/21/15: Firefox or Win 8.1 vulnerable with Flash Player vulnerability. See: here and here.
Update(3): 01/21/15: Microsoft releases FixIt for Windows 8 and 8.1 as well as Windows Server 2012.
Update(4): 01/22/15: Adobe releases a patch for CVE-2015-0310 which is a different vulnerability than the one mentioned here.
Update(4): 01/23/15: Malvertising campaign rides on Flash Zero-Day wave
We are tracking an ongoing campaign that is taking advantage of the latest Flash vulnerability. Major websites are unwillingly participating in the distribution of the Bedep Trojan via malicious ads propagated via various advertisers:
- clkrev.com
- ptrk-wn.com
- clkoffers.com
- affyieldmb.com
- zeroredirect1.com
- zb.zeroredirect2.com
- onclickads.net
The campaign can be identified by rotating referers using the .eu TLD which redirect to Angler EK landing pages (.in TLD).
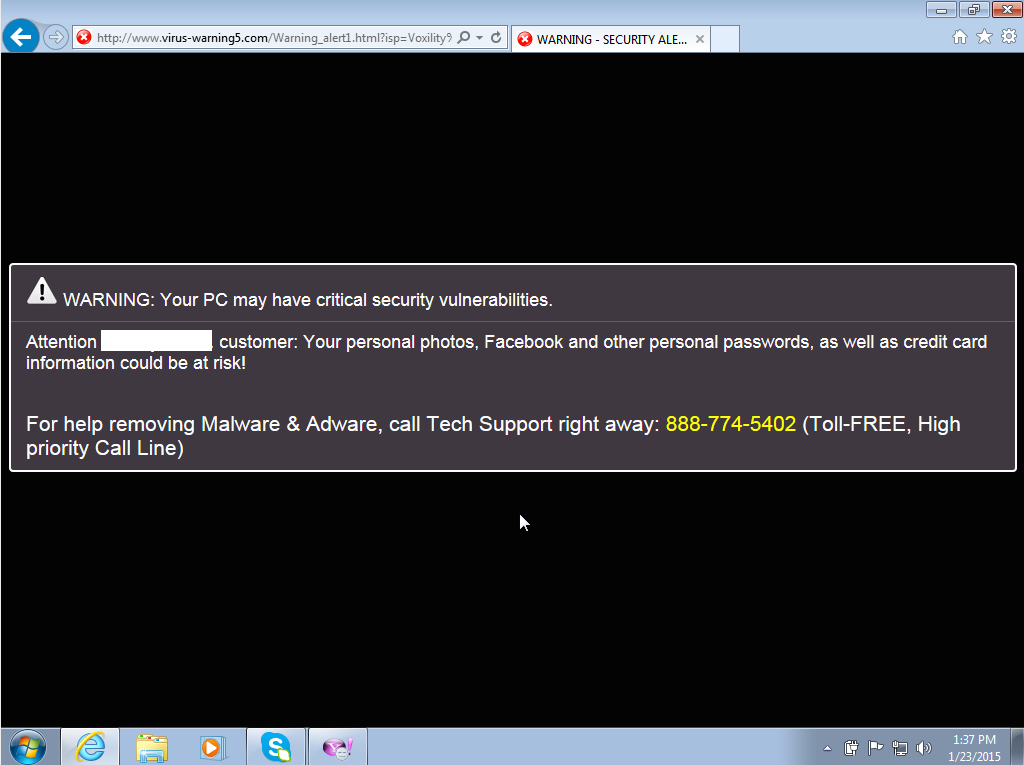
In some instances users get redirected to fake warning pages (tech support scams):
We will keep monitoring this campaign as it evolves.
Update(5): 01/24/15: Adobe releases patch for 0day
Adobe has released an update to the Flash Player to fix CVE-2015-0311. As always make sure you are downloading this update (version 16.0.0.287) ASAP, from the official site.