More often than not, online criminals take advantage of what’s currently popular, may that be news surrounding a certain celebrity, sites visited by a large number of netizens, or even well-known video game titles.
It is no wonder that Dragon Quest, an international best-selling RPG series developed by Square Enix, is used in the latest phishing campaign we’ve seen targeting gamers.
This campaign, which particularly banks on the reputation of Dragon Quest X (2012), is highly targeting video game players in Japan for account credentials. Below is what the phishing page looks like:

One may notice that the above looks the same as the Square Enix Account Management System, sans the CAPTCHA and Information sections.
Like the real thing, it also asks for the user name, password, and a one-time password (OTP), a token Square Enix put in place to further strengthen the security of user accounts. If this resemblance does not fool users, perhaps the URL on the address bar would. Let’s look at it closely.
hiroba[DOT]dqx[DOT]jp[DOT]se[DOT]uqdyr[DOT]com
Not only has phishers used typosquatting here, they also trust that users will be convinced that they are entering details on a legitimate page. hiroba[DOT]dqx[DOT]jp[DOT]se is a mistype of hiroba.dqx.jp/sc/, the real Square Enix page for Dragon Quest X.
The “se” in the fake URL is supposed to be “sc”, and instead of a “.”, it should be preceded with and followed by “/”. The domain for the phishing URL is uqdyr[DOT]com, while the domain for the legitimate URL is dqx.jp. These elements can easily be missed by users, even those with trained eyes.
Moving on: Once users feed their Square Enix credentials to the page and click Log In (the red button), the page makes a POST request to /account/app/svc/check.asp?step=1 then points users to the page below, asking them to specify their date of birth (DOB):
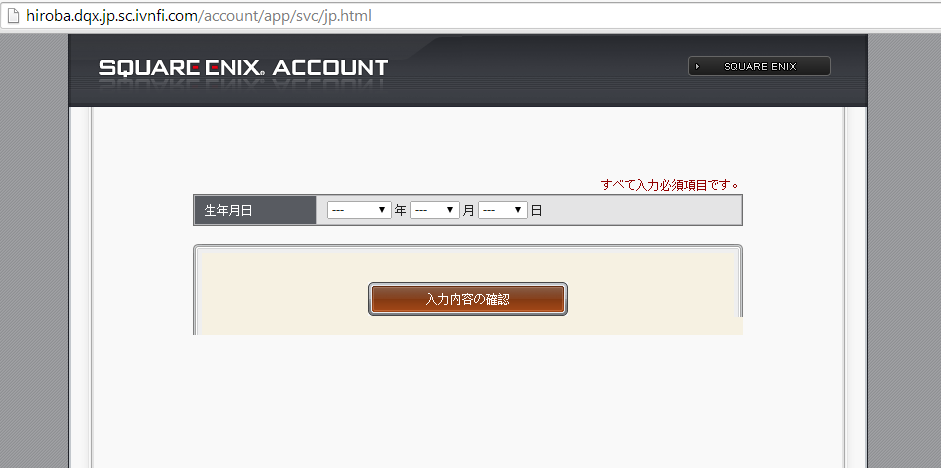
Once DOB is provided, this page makes a POST request to /account/app/svc/check.asp?step=2, and then redirects users to the legitimate Square Enix Support Center page where it discusses accounts.
ivnfi[DOT]com is found to be another domain housing the same phishing campaign. Doing a quick WHOIS for this and uqdyr[DOT]com has revealed that both have been registered and owned by one person based in China.
This isn’t the first tim users of Square Enix have been targeted by phishers; however, it happens quite sparingly that reports of which hardly makes it in the news.
We implore clients of Square Enix who play games across different platforms to visit and read this page on phishing to know more about the telltale signs of fraud. Japanese clients are advised to visit this page.
Jovi Umawing










