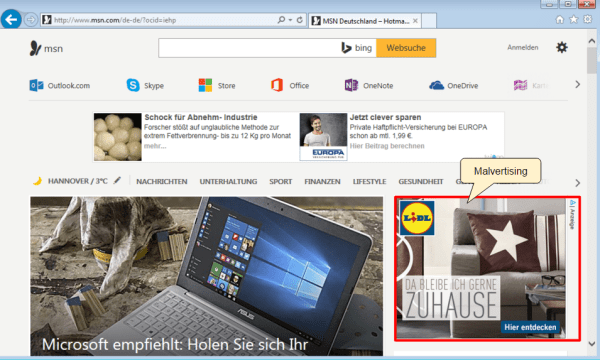
Malvertisers are once again abusing ad technology platform AdSpirit and exposing visitors of the MSN homepage to malware. These attacks appeared to have been primarily focused on Germans users via an ad for Lidl, one of the Germany’s leading supermarkets.
This is not the first time we have caught malvertising on MSN or via AdSpirit. Each time, we spot telltale signs of suspicious activity with advertiser domains freshly created a few days prior the attack or hiding behind the CloudFlare service.
Perhaps the only surprise here was to find different exploit kits than the usual Angler EK to carry out the execution to the malware payload. In two separate incidents, we observed the RIG and Neutrino exploit kits.

Incident #1 Flow:
- Ad call: lidl.adspirit.de/adframe.php?&ref=http%3A%2F%2Fwww.msn.com%2Fde-de%2F%3Focid%3Diehp&pid=236&ord=822757499
- Rogue advertiser: getkampagnen.com/banner.track?st=1&cb=523523&ebdr_sid={redacted}
- Rogue advertiser: norgren.top/adclick.adx?wid=48&pid=2&c={redacted}
- RIG EK: reg.elizabeththefirst.com/?xXmNd7GZKh7JD4M=l3SKfPrfJxzFGMSU{redacted}
Domain Name: getkampagnen.com Creation Date: 2016-01-12 Registrant Email: contact@privacyprotect.org
Domain Name: norgren.top Creation Date: 2016-01-06 Registrant Name: Jhon Smith [sic]Incident #2 Flow
:
- Ad call: ams1.ib.adnxs.com/if?{redacted}&referrer=http%3A%2F%2Fwww.msn.com%2Fde-de%2F%3Fpc%3DSK2M%26ocid%3DSK2MDHP%26osmkt%3Dde-de
- Ad platform: ib.adnxs.com/imptr?id=15543&t=1
- Advertiser: lidl.adspirit.de/adscript.php?pid=259&ord=1453041649&prdclick_0=ams1.ib.adnxs.com/click?{redacted}
- Advertiser: lidl.adspirit.de/adscript.php?&ref=http%3A%2F%2Fams1.ib.adnxs.com{redacted}
- Rogue advertiser: my-tracker.space/usermatch?wd=48&fid{redacted}
- Rogue advertiser: gamergrad.top/track/k.track?wd={redacted}
- Neutrino EK: yhkbtf.libromatt.top/hello/minister-alas-pencil-11158461
Domain Name: my-tracker.space Creation Date: 2016-01-17 Registrant Email: contact@privacyprotect.org
Domain Name: gamergrad.top Creation Date: 2016-01-12 Registrant Email: Jhon Smith [sic]
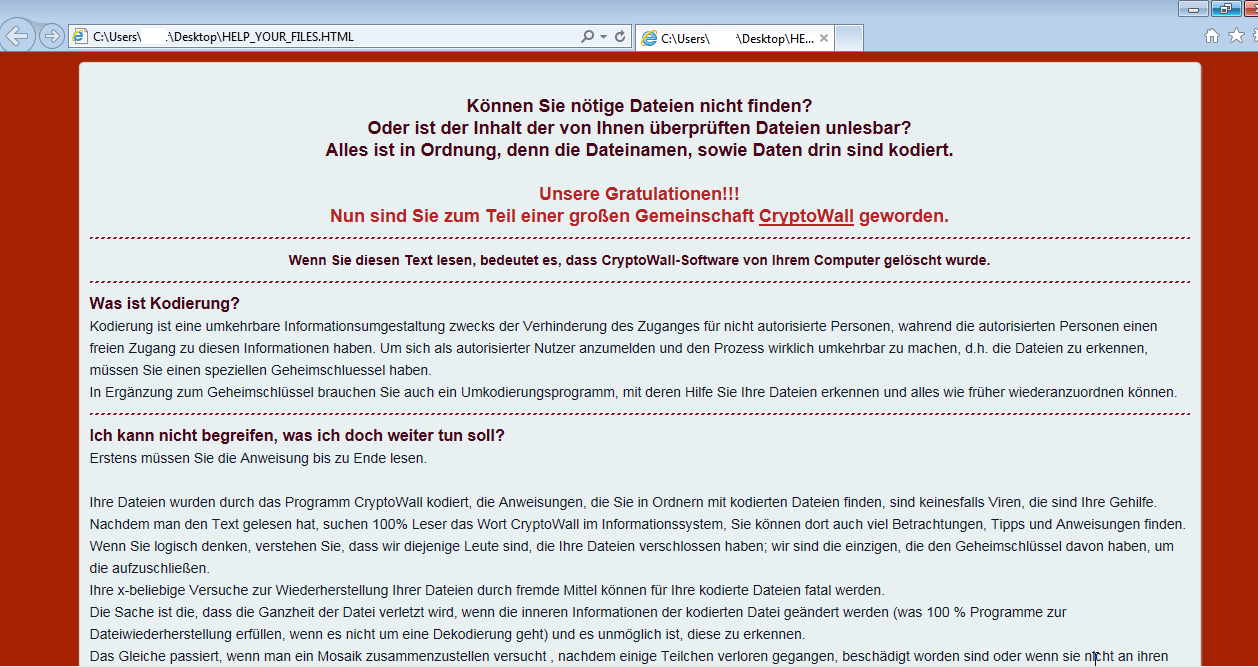
While we did not collect the payload in these specific attacks, other similar captures of RIG during the same time frame show that CryptoWall ransomware was downloaded onto vulnerable machines.
We immediately notified AdSpirit about those incidents which were confirmed and addressed promptly. AppNexus also deactivated the offending ad objects and will be doing a further review about these attacks.
To prevent these malvertising infections please ensure that your computer is up to date and that you are running the right security tools to mitigate those attacks. We recommend a combination of Anti-Exploit and Anti-Malware to keep the bad guys at bay.