Ransomware! Ransom Software! Encrypting Ransomware! AHHH!
No doubt the last year exposed you to this term numerous times and I doubt any of it was in reference to a good event.
So, you might wonder why you have been hearing about it so much, truth be told, ransomware has been a pain in the side of computer security folks for nearly four years now. But it feels like this year, so far, specifically has been the “Year of the Ransom” — just like the year before we had “Year of the Breach.”
Well, the reason you are hearing about more of it now is because there is literally MORE of it. In fact, almost 260 percent more than just five months ago! This stuff is everywhere!
Background
So what kicked it off?
Well starting in 1989 and until 2012, there was the version here and there that would lock something, demand payment either through e-mail, snail mail (seriously, look up the AIDS Trojan) and even SMS payment.
Then we saw the huge emergence of a new form of ransomware, you might know it as FBI or Law Enforcement ransomware, it basically locked down your screen, pretending to be from a LE organization, accused you of committing some crime and demanded you pay, usually using prepaid cards, to have your computer unlocked.
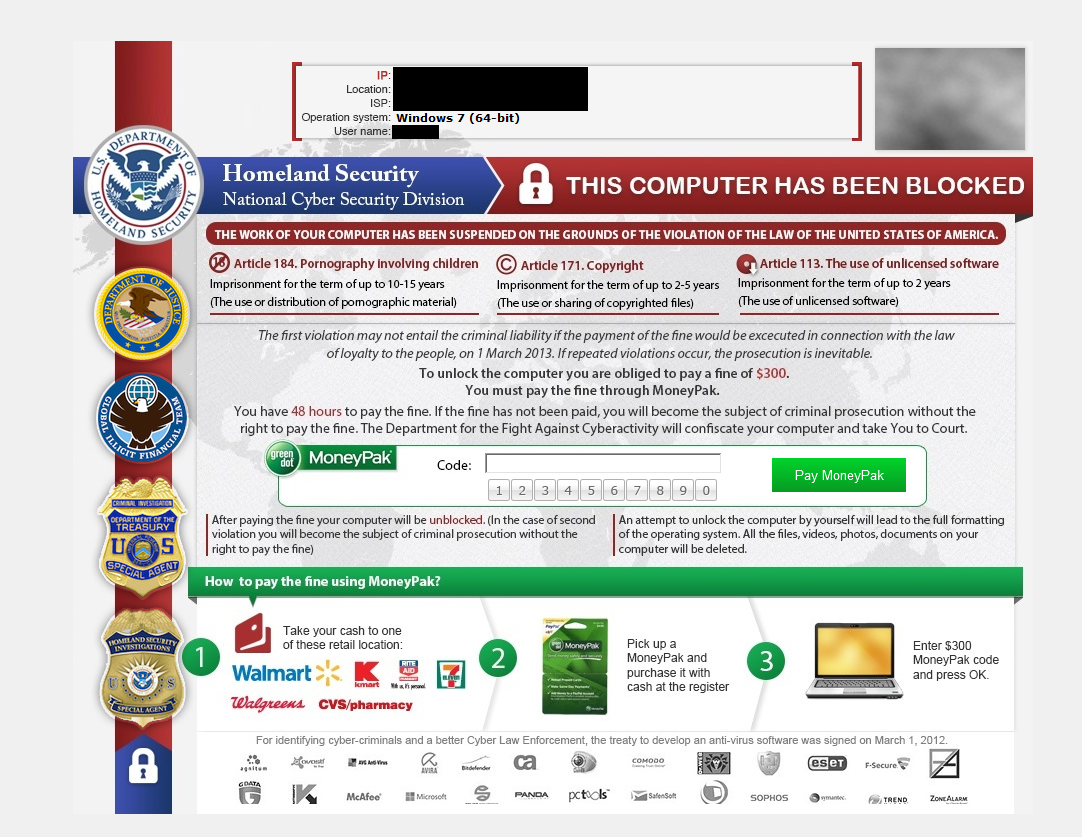
It didn’t take long for people to catch on that this was a scam and lucky for us, it was easy to remove.
So, some folks assumed that was the end of ransomware, but unfortunately it was not, in fact it was just the beginning.
In September 2013, Cryptolocker bounced onto the scene, not bothering to lock anything on the system, instead it just used high levels of uncrackable encryption to make all of your personal files unusable. It demanded payment in the form of pay cards and bitcoin as well.
Statistics
So for the last two-plus years, the security community has been fighting against not only Cryptolocker, but all the Cryptolocker-inspired copy-cats.
In fact, according to a study done by Symantec, from 2005 to 2014, there were only about 16 discovered families of ransomware in the wild, a small number in comparison to the 27 discovered in 2015 alone and the 15 discovered only in Q1 of this year.
The increase in ransomware in the wild is just one of the reasons you are reading about it everywhere (including our own blog) another reason requires us to take a look at some statistics we got from our Honeypot to determine how much of what was being pushed through drive-by exploits was ransomware, below is the chart for the largest grouping of malware dropped by exploit kits in December of 2015.
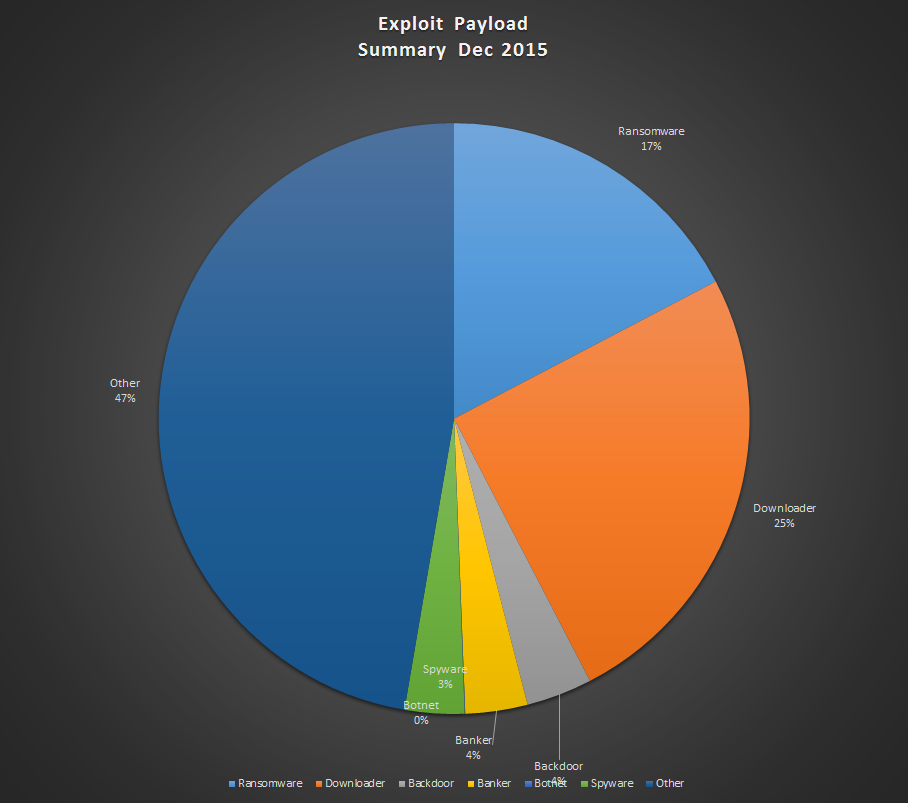
And now take a look at what we are dealing with as recently as May.
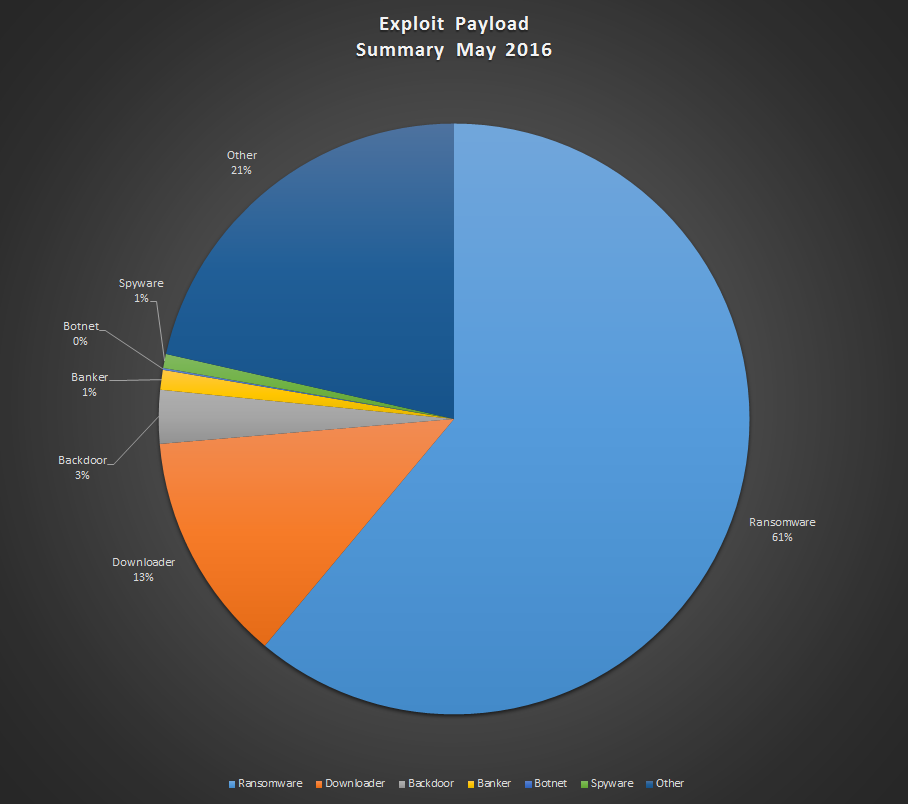
That is a 259 percent increase of ransomware being dropped by exploit kits in nearly half a year!
There are two things not taken into consideration in the above statistics:
- These charts only counts exploit kit activity, they do not mention malicious phishing emails.
- The stats break down ransomware payloads only, while droppers/downloaders are another statistic entirely.
Keep in mind that malicious e-mails are still a viable and frequently used method of infection, we expect stats from that infection vector to be similar to what we see from the exploit side.
In addition, while the ransomware payload statistic is massive, the reality is that plenty of ransomware has been seen infecting systems after being dropped by a downloader malware. In this particular case, I like to refer to downloader malware as “Schrödinger’s” malware because it might be ransomware, it might not be, you would only know what the final payload is if you execute it!
The professionals
To tackle the question of why there is such an increase in ransomware, we can first look at the pre-existing cyber crime groups and actors that have switched over to using ransom tactics over their previous methods. One group that pushed banker trojans like Zeus have started to diversify their income sources by switching to different families of malware, from Zeus to Citadel and then Dridex, all banker trojans but showing a clear sign that they look for the best investment to get the best return.
As recently as December, the same group has been observed pushing ransomware families like TeslaCrypt. Other groups with the same history have switched to ransomware families like Locky over using the same old banker trojans.
The fact is that once encrypting ransomware showed how profitable it could be, the rest of the cyber crime world decided they wanted a piece of that pie as well and abandoned other methods of attack. This is reflected in the previously mentioned statistics as the amount of malware as a whole has not decreased, in fact droppers, banker trojans and other types of malware are less common due to the overwhelming penchant cyber criminals now have for ransomware.
Copy-Cats
There are dozens of active ransomware families in existence, they are being pushed through every mainstream form of infection and it’s flooding the black market. In fact, the increase in families can be partially attributed to the popularity of ransomware and the availability of source code leaked online.
Hidden Tear was an “educational” ransomware, which was posted freely online for people to learn about what was required to write ransomware. Obviously having that code available to anyone was rubbing some folks in the underground the wrong way, as criminals who created a derivative malware using the same code, known as Magic Ransomware, and blackmailed the creator of Hidden Tear to take down the code or the victims of Magic would never get their encryption keys.
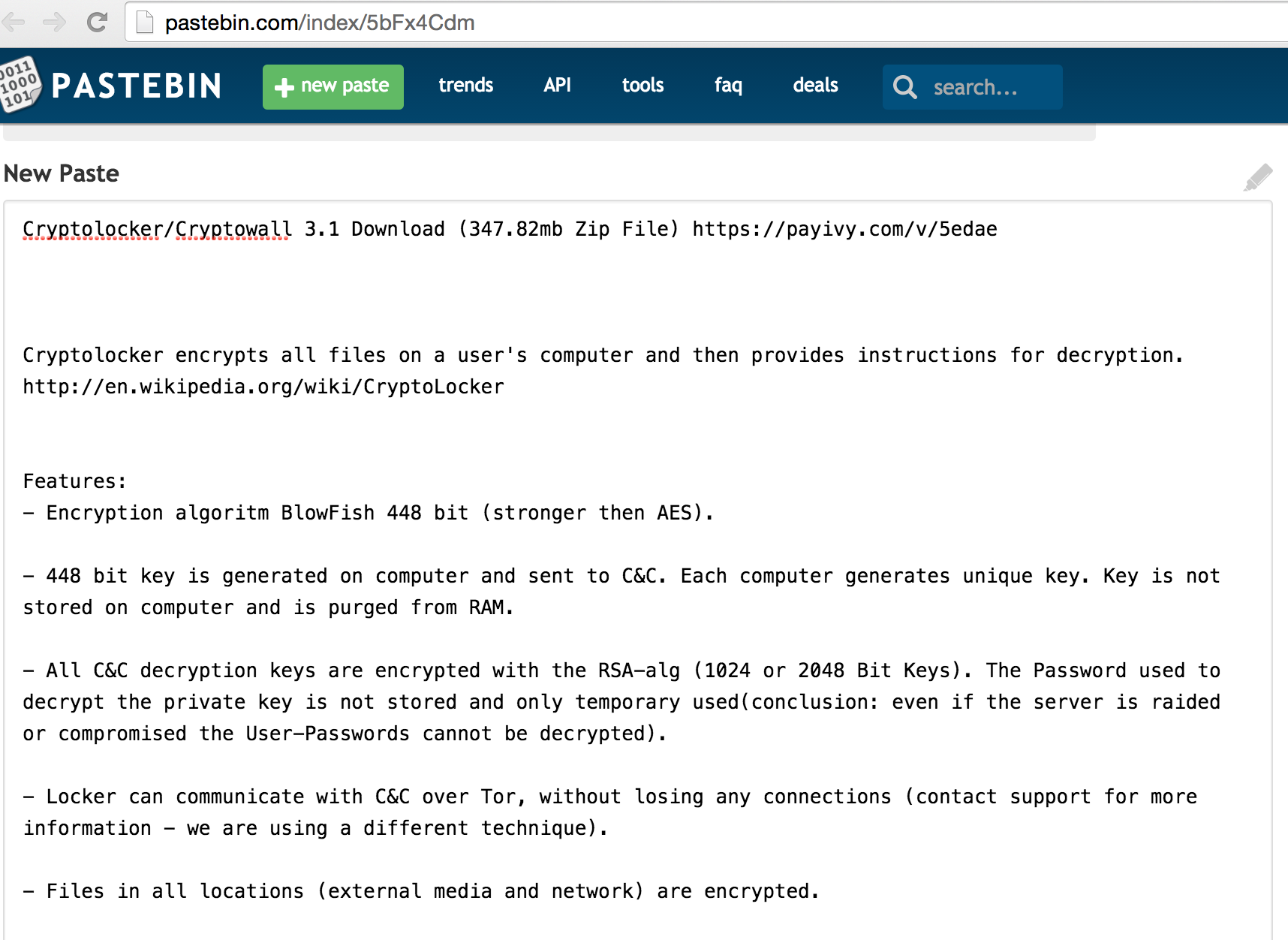
Alternatively, versions of other ransomware, such as Cryptolocker/Cryptowall 3,1 (above) might just end up being hosted for free by someone who purchased or stole it from the creators. This could easily be reverse engineered and modified to fit the needs of whomever has the code either to make it send payments to that person or re-brand it as an entirely different ransomware family.
The process of theft, creation, modification and distribution has left us with an immense amount of ransomware families, but at the end of the day its the old-fashioned method that has made such a huge problem for the security community.
RaaS
Known as Ransomware as a Service (RaaS), cyber criminals can continue doing what they have been doing with botnets, exploit kits, and every other cyber attack method out there, sell it to the next bad guy.
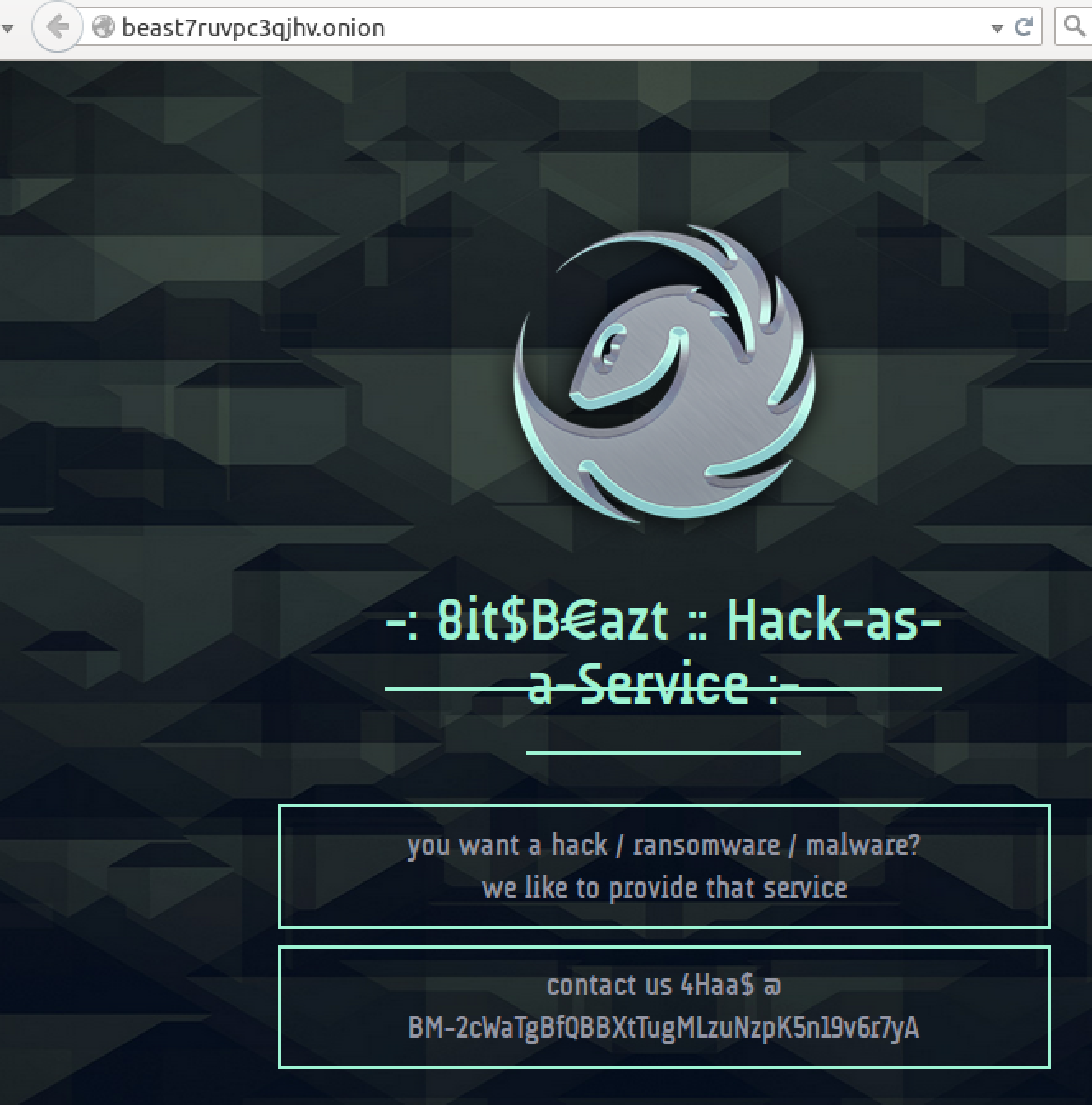
RaaS works by having a ransomware developer post an ad on an underground black market forum (or run a website) that advertises their ransomware product and its capabilities to cyber criminals who want to get into the ransom game, but don’t have the skills to create their own malware. Usually there is some kind of exchange of currency and the cyber criminal who purchased the malware now has a shiny new ransomware to play with, customized for their own personal bitcoin and/or email accounts and a command and control interface they can set up.

The Bandarchor ransomware is a product of the RaaS model, in the above screenshot you see the e-mail address”JohnyCryptor@aol.com” however other variants of this same malware have had lots of different e-mail addresses associated. This means that the malware is being created specifically for a customer, using the above e-mail address and most likely distributed by the purchaser.
RaaS belongs to a huge market that has been thriving for many years concerning cybercrime. Criminals can purchase hosting services, distribution avenues (exploits, phishing), crypting services (to hide the malware from AV detection,) you name it.
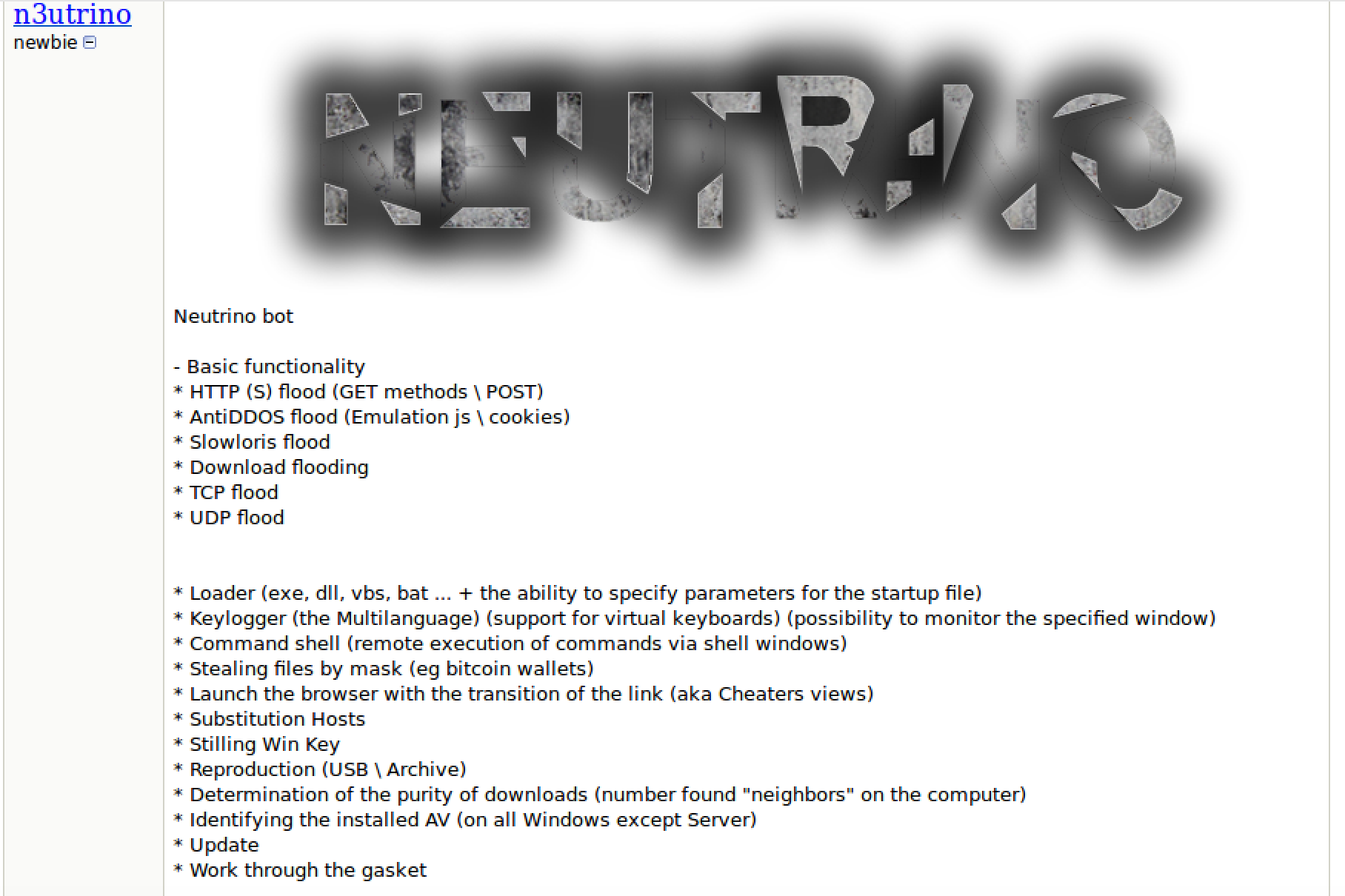
The fallout from this method of business is that you now have more criminals who can utilize ransomware and distribute it in greater numbers than before. The worst part is, little to no technical knowledge is required, meaning that even someone with no background in crime or computers could find themselves at the helm of a ransomware infection campaign.
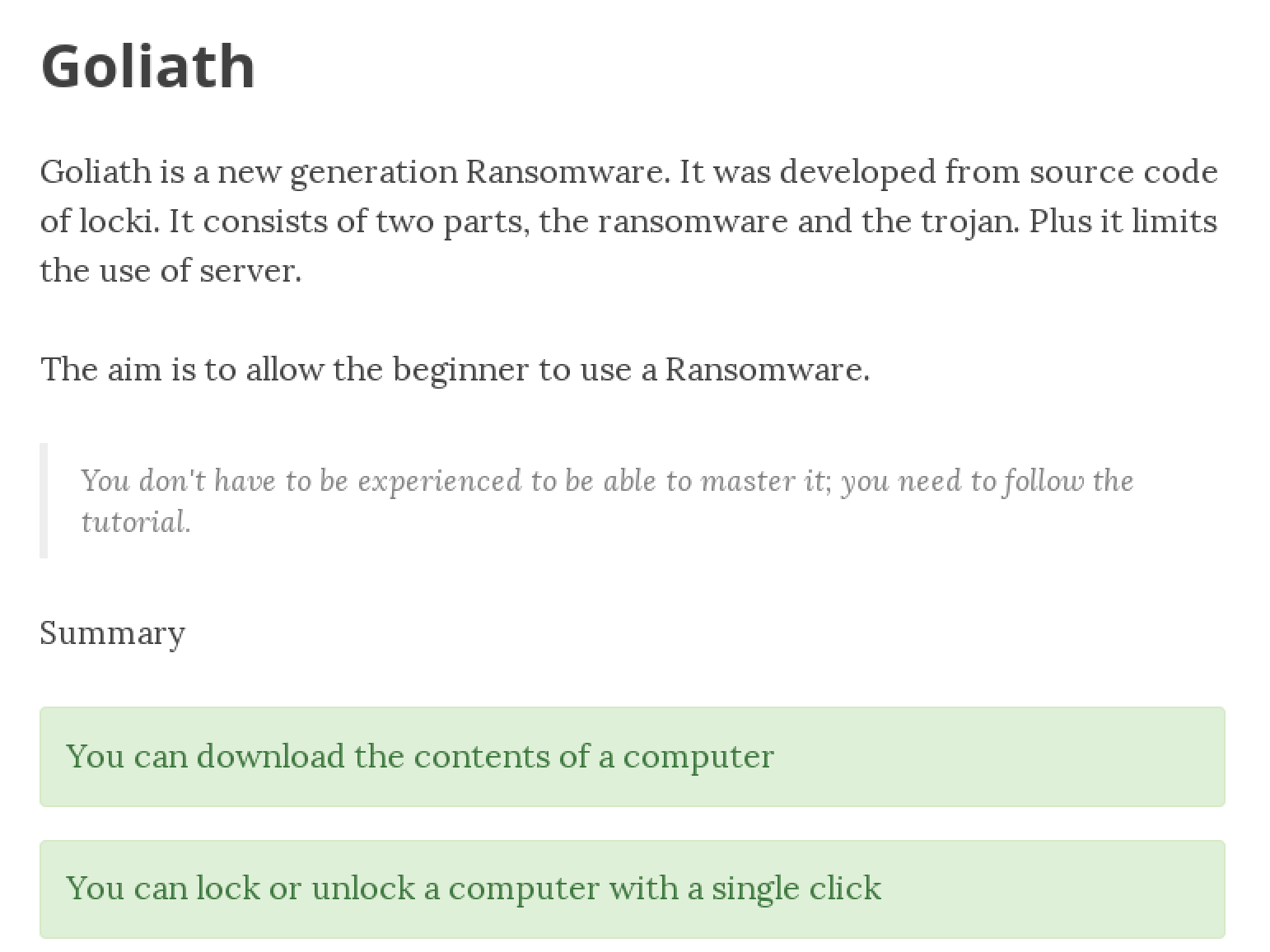
Goliath is a family of ransomware that makes it very easy for the cyber crime beginner to utilize ransom tactics against users. Even more terrifying is that a few families hope to share the wealth with other criminals, victims and anyone who wants a piece!
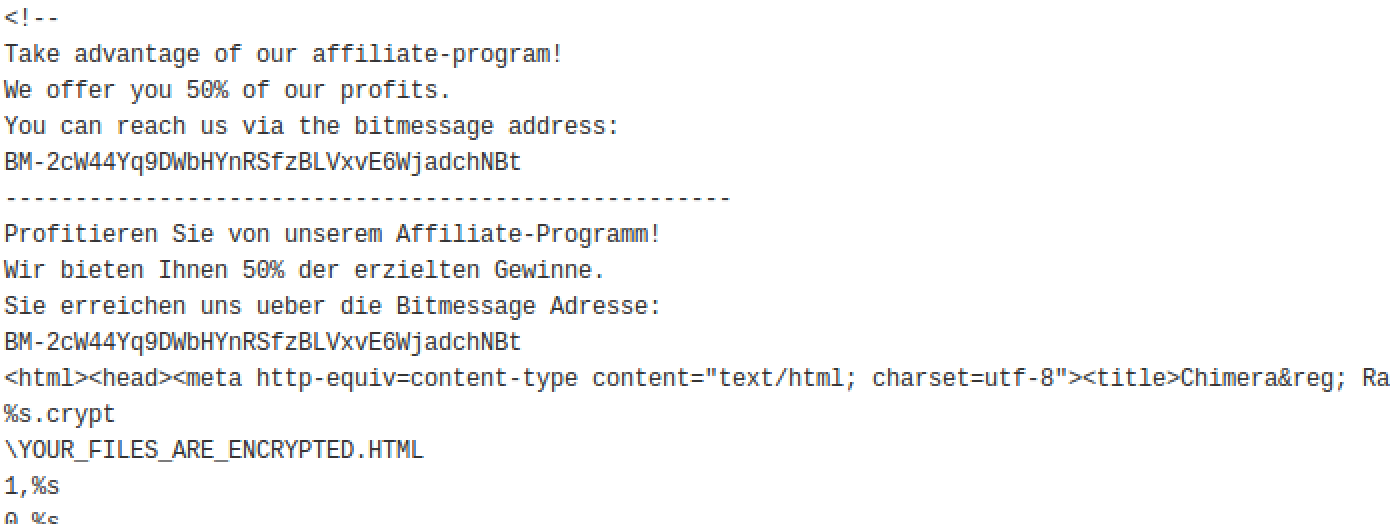
The above shows the HTML for the ransom screen belonging to the German Chimera ransomware, letting folks know that they are happy to work with other would-be criminals in distributing their malware and extorting victims.
Distribution methods
Finally, we can talk about how it gets on your system. Now there are two primary ways you might encounter ransomware:
- Malicious spam
- Exploits
Malicious spam is easy enough to avoid, usually its all about not opening that word document that you didn’t expect to receive, or to always so “no” to allowing macros to run. Exploits are a lot harder to avoid, unfortunately.
While avoiding shady sites is a great way to keep out of the reach of many exploit attacks currently in the wild, when dealing with malvertising, the game changes completely.
Malvertising is an attack wherein an ad server has been compromised somehow by a cyber criminal and has a malicious advertisement circulating through the network of customers the ad server provides for. These ads could be anything from a simple re-direction to full on malicious code embedded within them.
The below shows a malvertising attack launched from a user visiting the website of a local St. Louis news station.

When a user visits any website and the malicious ad happens to show up, they are exposed, it doesn’t really matter which website, as long as it serves ads its potentially going to exploit your system. The code that is executed will target a vulnerability in outdated, and sometimes updated, software that forces your system to download and execute a malicious file.
Many of the payloads being pushed by this form of attack result in ransomware. The previously mentioned statistics explain it all, as they were collected by analyzing the payload drops from malvertising and drive-by exploits.
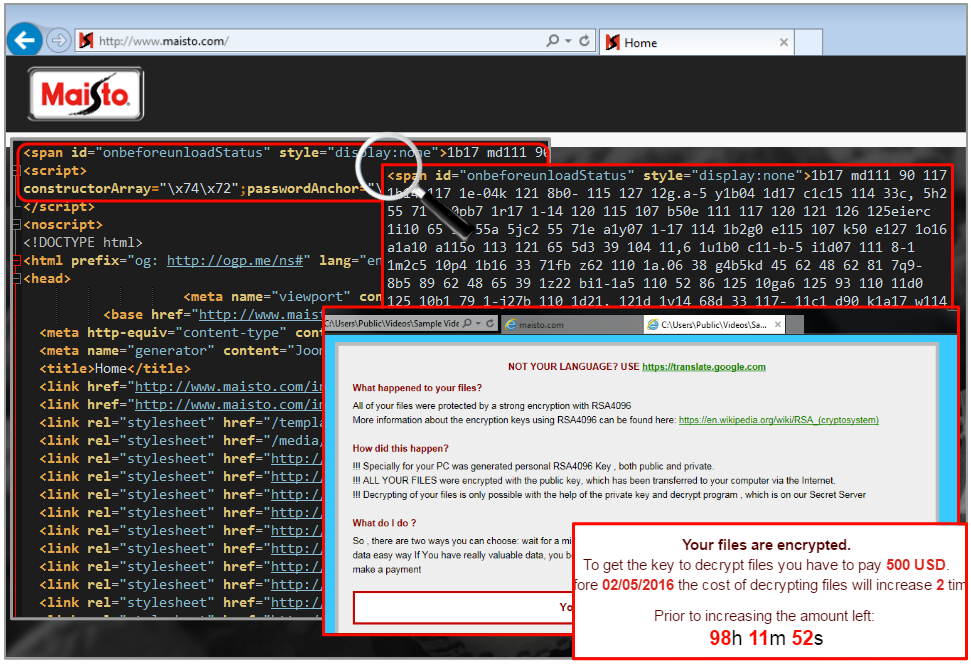
The above shows an incident that happened in April, where the website of a toy company was used in serving up an exploit attack that resulted in an infection of the CryptXXX ransomware.
The best solution to avoid these attack vectors include:
- Updating all outward facing applications (Java, Flash, Internet Explorer, Silverlight)
- Utilizing an Ad blocker (only effective against Malvertising, most of the time, and not compromised websites)
Conclusion
So there you have it, if you thought that the ransomware hype was simply created by the media to sell papers, think again!
Ransomware has become the most frequently used form of malware attack due to its being plentiful in the underground, easy to use and incredibly effective at extorting large amounts of money from victims.
The worst part is, it bypasses all the rules we learned previously on how to fight malware. The sad truth is that there is rarely any recourse after a ransomware infection, its game over and no amount of scanning or cleaning after the fact will return your files. However, here are a few tips on what to do after you have been infected:
Do not pay the Ransom
Identify the ransomware family you are infected with
Due to the fact that many families are copy-cats of more well established ransomware or just poorly coded, there may very well be flaws in the encryption process and security researchers have worked hard to identify those flaws and create decryptors for the victims. It’s not a 100% solution, but its worth a shot.
Do not pay the Ransom
Don’t connect your computer to any other external media device or network drives
Many variants of ransomware will identify personal files that aren’t even on your physical hard drive. You don’t want the ransomware to encrypt any backups you might have or shared files on a file server.
Do not pay the ransom.
Immediately shut off any auto-backup feature you might have for offsite/cloud backups
If you are using an offsite / cloud backup service, fantastic! Great job to you for being proactive! However, if you have those files auto-backup either at a certain time of day or when it detects some changes, if you don’t turn it off you’ll end up with a backup of encrypted files.
DO NOT PAY THE RANSOM!!
There are a lot of controversial opinions on this particular topic, at the end of the day you have to realize that by paying the ransom, you are encouraging not only the criminals that infected you, but also other would-be criminals to take up using ransomware.
The statistics, explosion of families and availability of this malware show that we have already failed to prevent ransomware from becoming popular among criminals. An argument for paying is that a person or organization might not have any other choice, it might be a matter of cost verses risk.
However, despite all of the “free decryption trial” promotions ransomware criminals might offer, there is no guarantee that you are going to get your files back.
In fact, a hospital in Kansas was hit with ransomware and even after they paid the criminals, only part of their files were decrypted while more money was demanded from the victims to do the rest.
The only thing you are doing by paying the ransom is showing the criminals that you are willing to give into their demands and they are going to take advantage of that fact.
Some folks might claim that it’s not the job of the victim to fight ransomware, well I wonder if those same people are the ones who think it’s not their job to prevent the spread of a disease they are infected with.
Fighting malware is the responsibility of everyone, even if its just reading an article, sharing a post or taking a stand against criminals who are unlikely to ever be caught.
Thanks for reading and safe surfing.










