On Valentine’s Day, Mac users got a special “treat” in the form of new malware. Then, later that same week, there were signs of yet another piece of malware looming. These threats were overshadowed a bit by the discovery last week of the second ransomware app to ever appear on the Mac, but they’re still worthy of consideration.
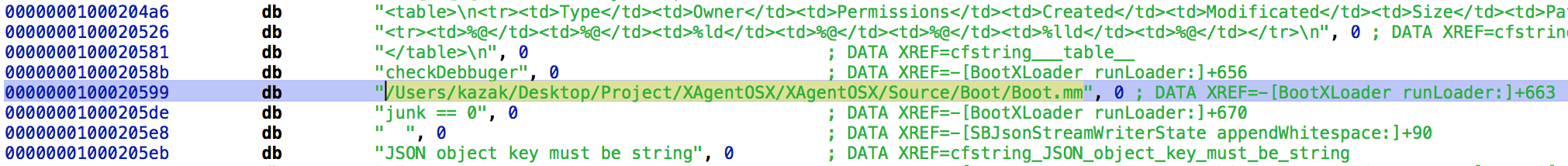
The first malware, named XAgent, was analyzed by Palo Alto Networks. XAgent, it turns out, is related to the Komplex malware discovered by Palo Alto last year, as can be seen by comparing some of the strings to those found in Komplex.
At that time, Palo Alto tied Komplex to the Sofacy Group – also known by the names Fancy Bear and APT28, among others – a Russian hacking organization that has since been linked to such things as the hack of the Democratic National Convention.
XAgent is a backdoor that provides a number of powerful remote access features, including keylogging, screenshots, remote shell access, and file exfiltration. Of particular interest is a command that provides the hacker with information about iOS backups stored on the infected Mac. iPhones (and other iOS devices) are notoriously difficult to hack, but by targeting backups instead, this malware could access potentially sensitive iPhone data.
Interestingly, Patrick Wardle, Director of Research at Synack, had another interesting revelation about this malware. He shows quite convincingly that the Sofacy Group used code copied from the Hacking Team. (Hacking Team is the creator of the Remote Control System backdoor, which it sells to governments and law enforcement, among other organizations.)
Hacking Team was itself the victim of a hack in 2015, and all their source code was made public. Wardle was able to demonstrate key similarities, such as identical bugs, in the decompiled XAgent code and the leaked Hacking Team code. It appears that Sofacy used Hacking Team code in their malware, most likely obtained from the Hacking Team breach.
According to a whitepaper released by Bitdefender, the malware installs itself into the following folder, where it is given one of a set of hard-coded names:
~/Library/Assistants/.local/
At the time of its discovery, the XAgent command & control servers were down, meaning that this variant of the malware is no longer a threat.
On the heels of the XAgent discovery came an intriguing glance at another piece of Mac malware, a sample of which has not yet been found. Three days after Palo Alto released their analysis of XAgent, Apple released an update to XProtect – the built-in anti-malware software in macOS – that added detection of XAgent.
However, that update also included a signature for something Apple called OSX.Proton.A, which ignited a storm of questions in the security community, who had never heard of any such malware for the Mac.
A little digging by Arnaud Abbati, a researcher at Ninja, Inc, turned up a page from the Sixgill website with a terse description of a remote access tool (RAT) called Proton. The page has been taken down, but can still be found in Google’s cache here.
Apparently, the malware is being sold on a Russian cybercrime forum, among other places. Sixgill also provided a link to a YouTube video from December, apparently made to promote the malware by demonstrating its capabilities. Another YouTube video, posted on February 8, showed additional capabilities.
Unfortunately, thus far, no samples of the malware have been found. It does not appear to be in the VirusTotal database, and neither of the sites that appear to be associated with Proton (ptn[dot]is or protonsolutions[dot]net) are responding. Even Sixgill’s analysis seemed to be done entirely from online sources, and had no information to suggest that they had seen a copy of the malware. For now, this is a completely unknown threat with rather frightening apparent capabilities.
Two new malware threats in a week, added to the others previously seen this year (Quimitchin/Fruitfly, MacDownloader, a new class of Microsoft Office macro malware and the Findzip ransomware), brings the Mac malware count for 2017 up to 6, and February isn’t even over yet. If things continue at this rate, 2017 could see a spike in Mac malware that could rival or exceed the previous high point in 2012, when the infamous Flashback, and a number of other pieces of malware taking advantage of Java vulnerabilities, terrorized the Mac community.










