Tech support scammers are reusing an old technique in their existing browser locker (browlock) schemes to force a special kind of file download. Contrary to past attacks, where the purpose was to flood the machine with a large amount of file requests in order to crash the browser, this one is purely a social engineering ploy.
Indeed, the flooding technique that abuses the window.navigator.msSaveOrOpenBlob method, which we reported on this blog before, has already been fixed in Google Chrome. What we see here instead is a blend of a previously-exploited HTML5 method known as history.pushState() and the Anchor download technique.
Here’s how it works: Unsuspecting users are served a fake Microsoft alert page as they are browsing various websites. Typically, the redirection is initiated by a malicious advertising (malvertising) chain.
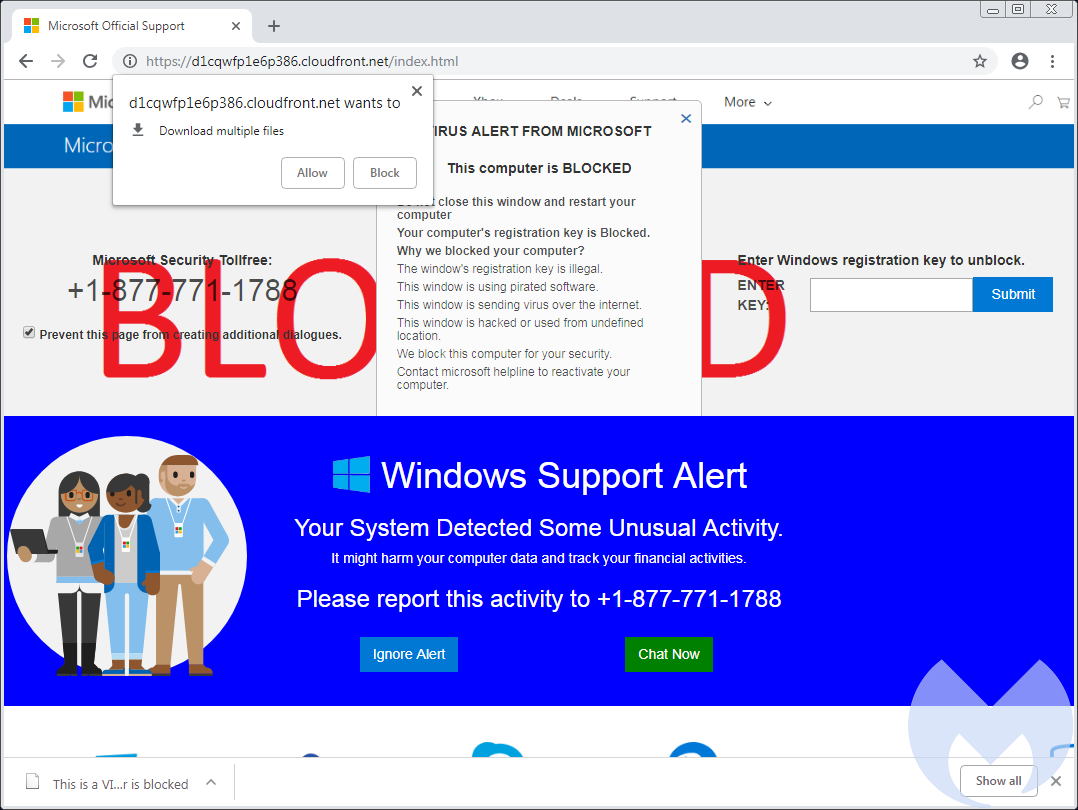
The page attempts to use various tricks to create the lock impression, for example by monitoring mouse and keyboard events and forcing itself into fullscreen mode. Additionally, it starts an automatic file download named “This is a VIRUS.You computer is blocked” (sic) as seen below:
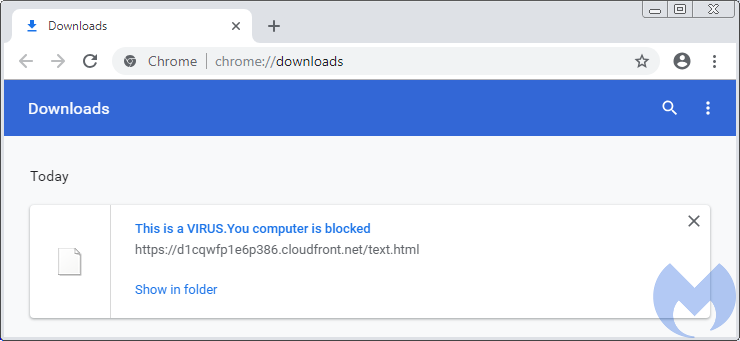
This file is a copy of the browser locker HTML code, so you could say that it is malicious in nature, but it cannot harm the computer like a virus or malware. The scammers are simply using strong words to scare potential victims.
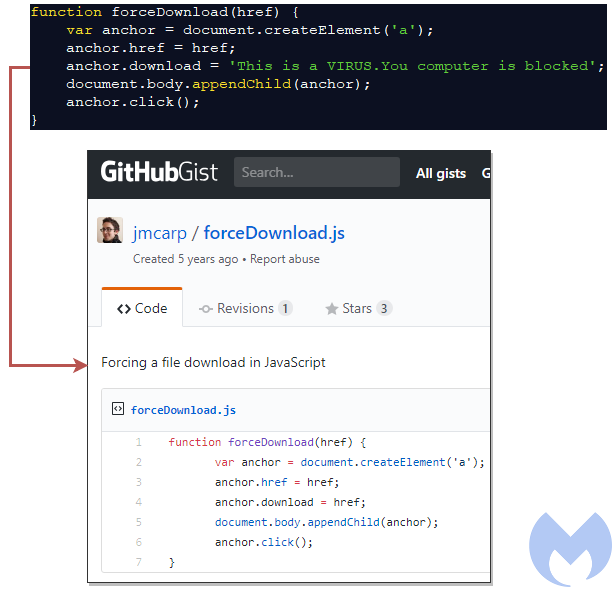
The underlying code responsible for this behavior consists of the use of the jQuery library (jquery-3.3.1.min.js) and a few blocks of JavaScript, starting with the Anchor element. This was likely grabbed and modified from this 5-year-old Github Gist:
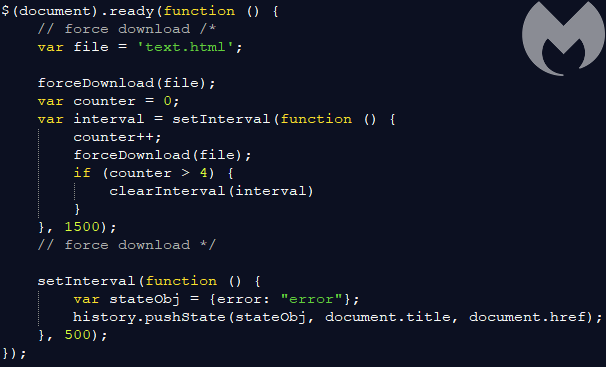
The second part consists of creating a loop and interjecting the history.pushState method:
Different browsers will handle the automatic file download in their own way. For example, Firefox will prompt users multiple times for the bogus file download:
Once again, we see that tech support scammers continue to abuse browsers using basic techniques. Their effectiveness is in large part due to the fact that these are legitimate features or web standards that are being used in malicious ways.
For this reason, browser vendors can have a hard time mitigating these types of attacks without also breaking legitimate use cases. The browser hang with infinite downloads bug we blogged about at the beginning of the year is still unresolved in Mozilla Firefox.
Malwarebytes Browser Extension (Beta) mitigates these browser lockers both for Chrome and Firefox.










