“It happens to the best of us.”
And, indeed, no adage is better suited to a phishing campaign that recently made headlines.
Fraudsters used the brand, KnowBe4—a trusted cybersecurity company that offers security awareness training for organizations—to gain recipients’ trust, their Microsoft Outlook credentials, and other personally identifiable information (PII). This is according to findings from our friends at Cofense Intelligence, who did a comprehensive analysis of the campaign, and of course, KnowBe4, who first reported about it.
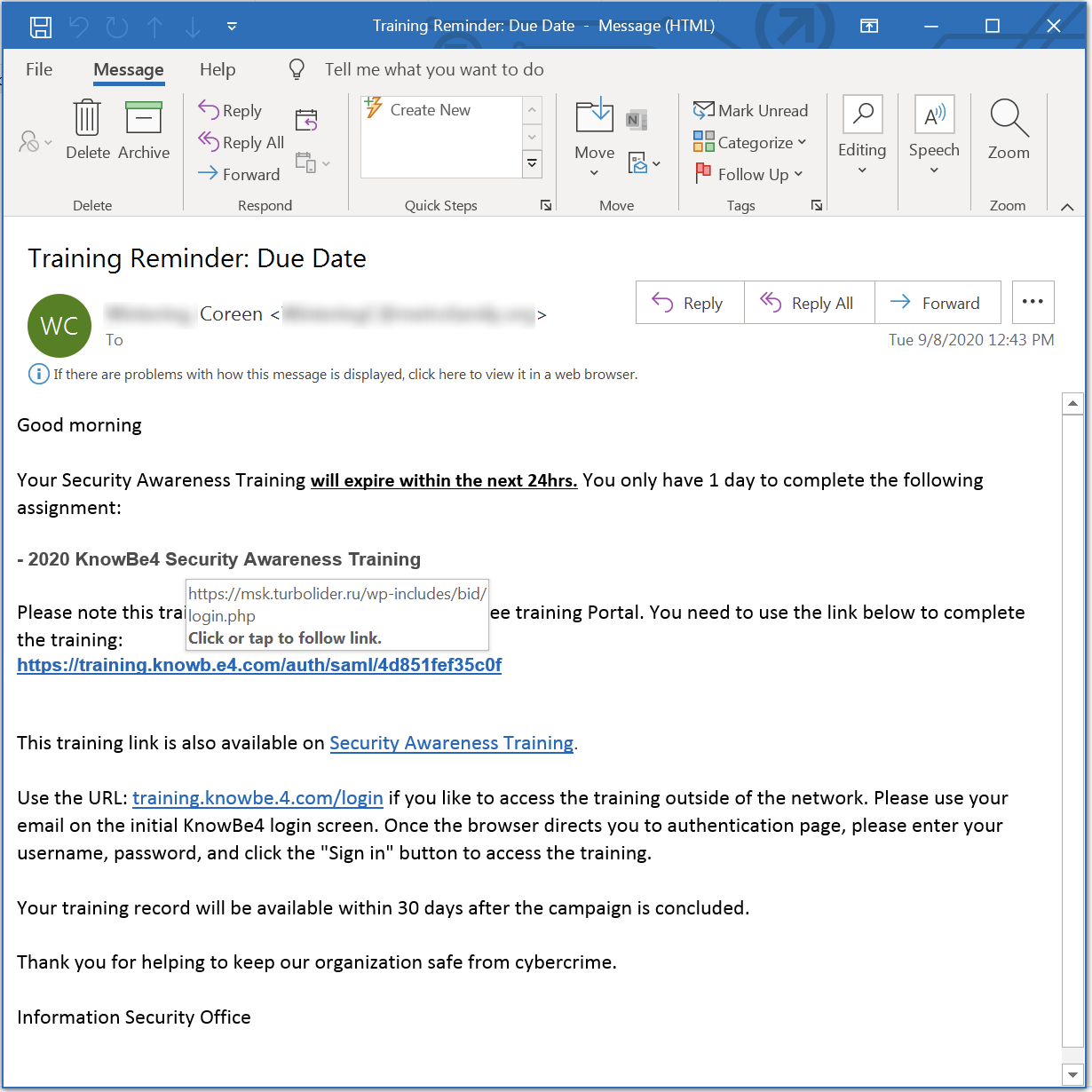
Email details are as follows:
Subject: Training Reminder: Due Date
Message body:
Good morning
Your Security Awareness Training will expire within the next 24hrs. You only have 1 day to complete the following assignment:
– 2020 KnowBe4 Security Awareness Training
Please note this training is not available on the employee training Portal. You need to use the link below to complete the training:
hxxps://training[.]knowb[.]e4[.]com/auth/saml/4d851fef35c0f
This training link is also available on Security Awareness Training.
Use the URL: training[.]knowbe[.]4[.]com/login if you like to access the training outside of the network. Please use your email on the initial KnowBe4 login screen. Once the browser directs you to authentication page, please enter your username, password, and click the “Sign in” button to access the training.
Your training record will be available within 30 days after the campaign is concluded.
Thank you for helping to keep our organization safe from cybercrime.
Information Security Officer
“Poor English” is usually a hallmark of a scam email, according to majority of cybersecurity experts, and phishing emails are notoriously known for it. The above training-themed email may have fooled several recipients who are quite forgiving to some English errors—after all, typos do happen.
However, we should remember to also look at the URLs closely, both on the email and where it really leads to when you hover a mouse pointer over each one of them. Granted this is a straightforward, unsophisticated scam, which makes discerning it easier. It also gives us the notion that whoever the campaign is trying to bag, they’re only after those who aren’t careful enough to look closely or critical enough to perceive that something is amiss.
To the seemingly untrained eye, the URLs on the email may seem genuine, but they’re not. If you’re familiar with a URL’s structure, you’ll realize quickly that they’re not even close to being genuine. Take, for example, training[.]knowb[.]e4[.]com. The main domain here is e4[.]com. As for training[.]knowbe[.]4[.]com, the main domain is 4[.]com. Basic familiarity to URLs can save you from falling for scams like this.
Once users click any of the links, they are directed to a destination that doesn’t bear the KnowBe4 brand but to what appears to be a Microsoft Outlook sign in page, asking for credentials.
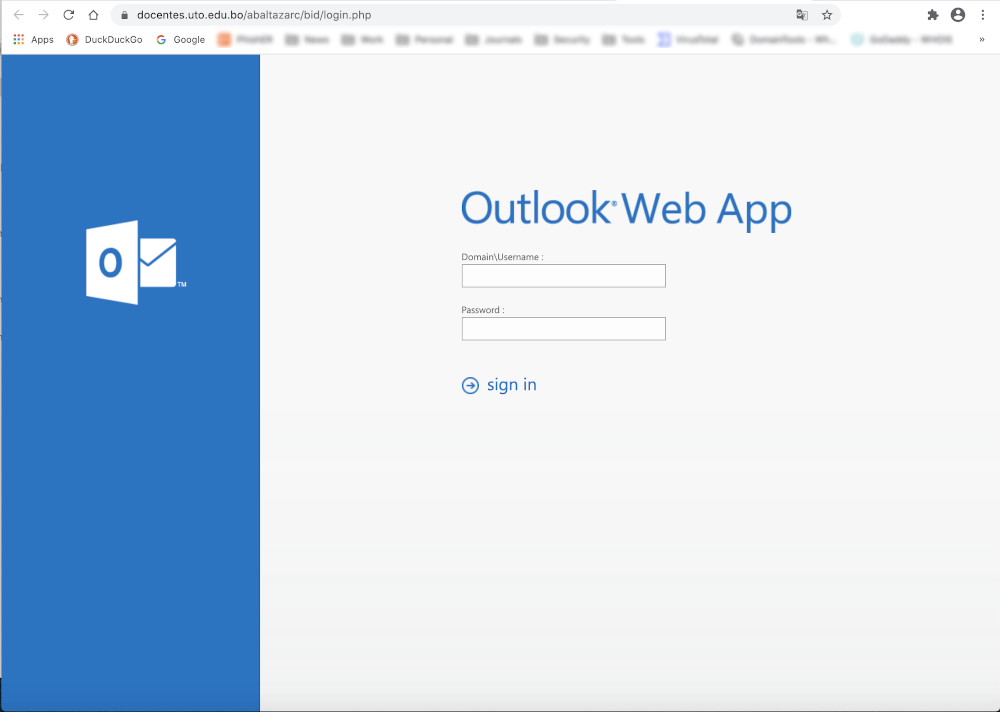
Again, take note of the URL in the address bar.
According to Cofense, similar phishing pages like this are hosted on at least 30 sites since April of this year. They also found traces of other current or previous phishing campaigns that were themed around sexual harassment training, another learning course many organizations require their employees to take.
Going back: Once the Outlook username and password combination were provided and the user clicks “sign in”, they are directed to another Outlook page, this time asking for details that are more personal, such as date of birth and physical address.
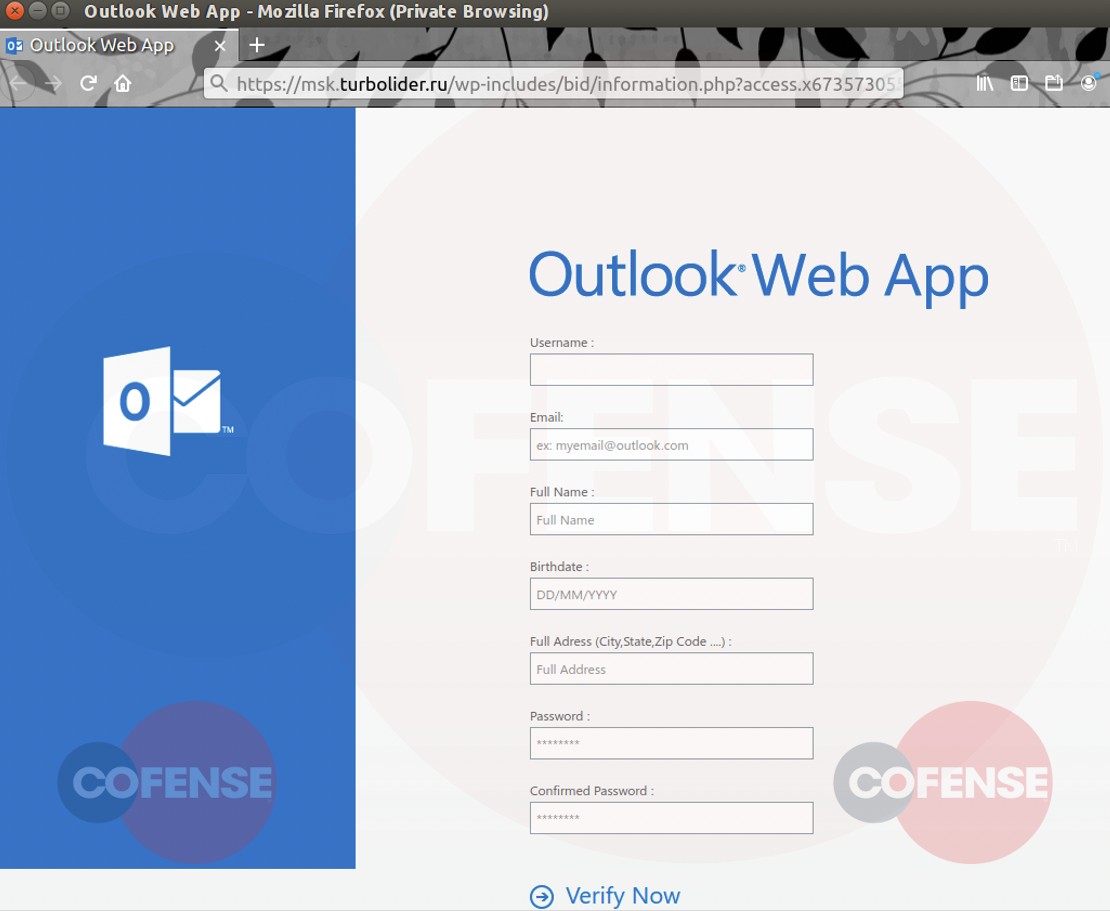
As the phishing kit had already been taken down at the time of writing, testing couldn’t show what happens next after clicking “Verify Now”. But based on the sexual harassment training phishing campaign, which used the same kit, redirecting to a legitimate sexual harassment training page, it’s logical to conclude that users would also be directed to a security awareness training website, which may or may not necessarily be KnowBe4.
This isn’t the first time the KnowBe4 brand—or other cybersecurity brands for that matter—have been abused to defraud people. The company was first used in phishing campaigns in September 2018 and in January 2019.
In February of this year, a NortonLifeLock phishing scam, wherein threat actors forced a remote access Trojan (RAT) installation onto victim systems by making a malformed Word document appear to be password-protected by NortonLifeLock, was found in the wild.
In April 2019, sophisticated Office 365 credential stealers didn’t only craft fake Microsoft alert types around certain Microsoft products, they also mimicked the return path of Barracuda Networks, a well-known email security provider, and include it in the phishing email’s Received header, making the email appear that it passed through Barracuda servers. This would make it seem like it could be trusted, and thus, safe to open, when—upon closer inspection—it’s not.
Every organization has a brand to protect. And the first step to do this is to realize early on that their brand could be misused or abused by those who want to make illicit gains. That said, no brand is truly safe. Heck, even Malwarebytes has doppelgängers.
Businesses must be actively looking for those banking on their names online. Customers, on the other hand, must know and accept that online criminals can get to them through the services they use by pretending to be these companies. It’s no longer enough to readily trust emails based on the logos they purport to bear. It’s time to start carefully reading emails you care about and scrutinizing them, from the supposed sender to the email links and/or attachments.
Never attempt to click anything on dubious emails or visit the destinations by copying and pasting them on a browser unless you’re in a virtual machine. And if you don’t have time to do the investigative work yourself, ask. Give your service provider a call or report a potential phishing attempt. This way, you’re not only helping yourself but also alerting your provider and helping those who would have fallen for a scam if not for your efforts.
Stay safe!










