Michael Grime, a British games programmer, has escaped jail after using stolen credentials to access several women’s personal email accounts and social media accounts in order to steal their private and intimate photos.
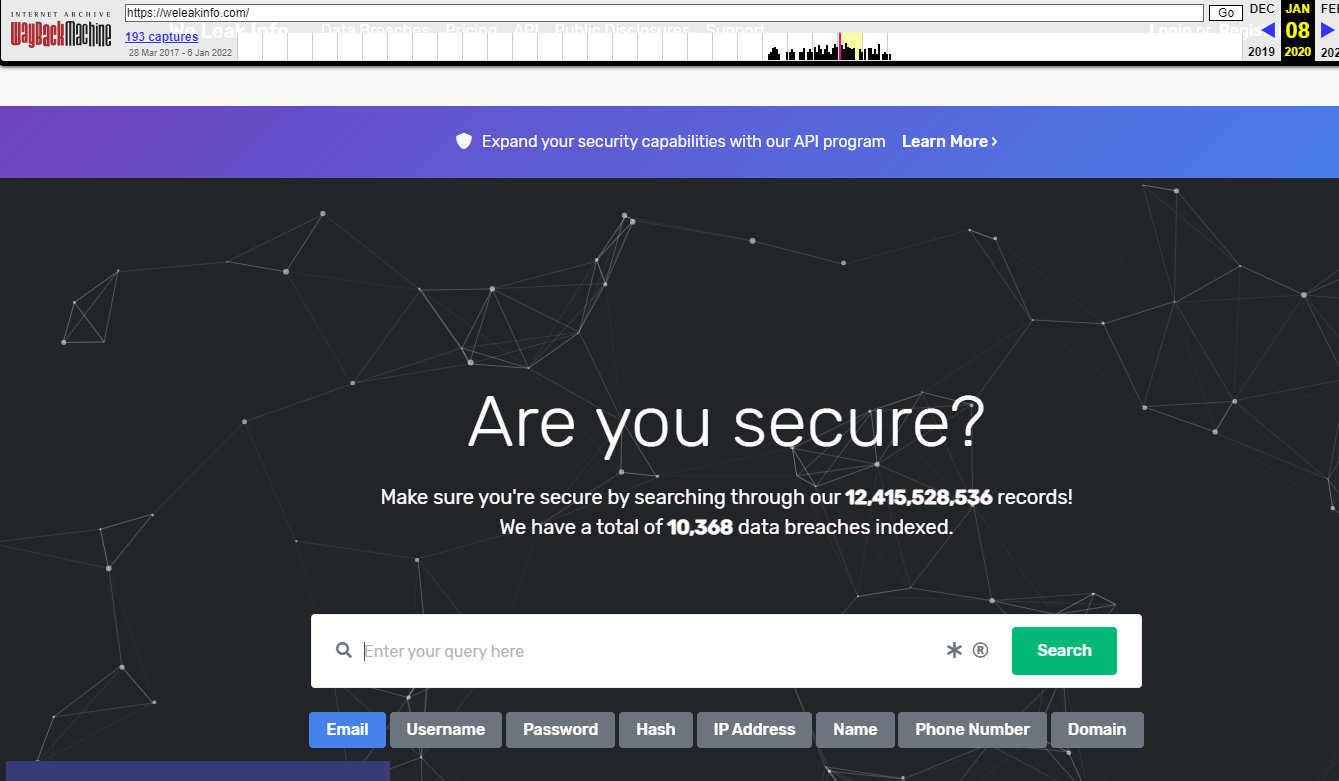
Grime was caught by the National Crime Agency (NCA) as part of an operation involving several agencies and the FBI. The agencies were able to link his email address to an account in WeLeakInfo[dot]com, a website that sells leaked credentials. Grime is said to have been paying $2 USD a day to access this site before it was taken down by law enforcement in early 2020.
WeLeakInfo[dot]com is marketed as a site that offers access to 12 billion user records collected from more than 10,000 data breaches. These records contain user names, email addresses, IP addresses, passwords, and phone numbers.

In November 2020, law enforcement officers raided Grime’s home and seized a PC tower, three external hard drives, and his mobile phone. Thousands of photos and videos of women either topless or nude were found on his devices, many of which were images that had never been shared publicly.
The NCA primarily identified 11 women in the UK, most of whom went to school with Grime or had known him since childhood. It isn’t specified how many women Grime victimized outside of the UK. Some of his victims are popular figures on YouTube and Only Fans.
During a Preston Crown Court hearing, Grime admitted to having access to “around 50 accounts”. In one incident, Grime, who was described as “geeky, loner, and odd”, hacked the account of one of the women’s boyfriend’s to access private photos shared between the couple.
Lisa Worsley, prosecuting, told the court that his victims “felt betrayed and sad. One woman’s first response was to delete all her social media which she found upsetting.”
“Another said her Snapchat has been unstable and would log her out three or four times a day.” That’s a red flag there.
On the defending side, the lawyer whom outlets only name as “Mr. Forbes” told the court that Grime is “socially awkward” and may be on the autistic spectrum, although Grime has never had an official diagnosis. Forbes also said that his client became obsessed with hacking and “liked the detective work”.
“Many cybercriminals rely on the fact that lots of people use the same password on multiple sites and data breaches create the opportunity for fraudsters to exploit this,” said Detective Inspector Chris McClellan from the North West Regional Organizaed Crime Unit, who carried out the warrant at Grime’s home address in November.
“He knew it was wrong,” Forbes is quoted saying, “He stopped on occassions but [sic] and deleted material and would start again. This was something over which he felt he had little to no control over.” Forbes said Grime’s arrest was a “relief” for the young programmer as Grime didn’t have to rely on his weak will to stop himself from hacking accounts and downloading photos.
Although he wasn’t imprisoned, Michael Grime was given a community order, which orders him to do unpaid community work for 80 hours over two years. He was also ordered to undergo rehabilitation for 30 days and pay £500 as compensation for each of his 11 victims.
DI McClellan advised internet users to check if their credentials and personal data have been part of a data breach by using legitimate websites like haveibeenpwned.com. If users find one or more of their accounts have been compromised due to breaches, they should make new strong passwords for each account.
“Do not reuse passwords and where possible apply Two Factor Authentication (2FA). This will help you prove you are who you say you are when you are logging into your account. Do not share the 2FA code with anyone.”
Sage words.










