It’s not unusual to hear about malware created to affect automated teller machines (ATMs). Malware can be plantedat the ATM’s PC or its network, or attackers could launch a Man-in-the-Middle (MiTM)attack.
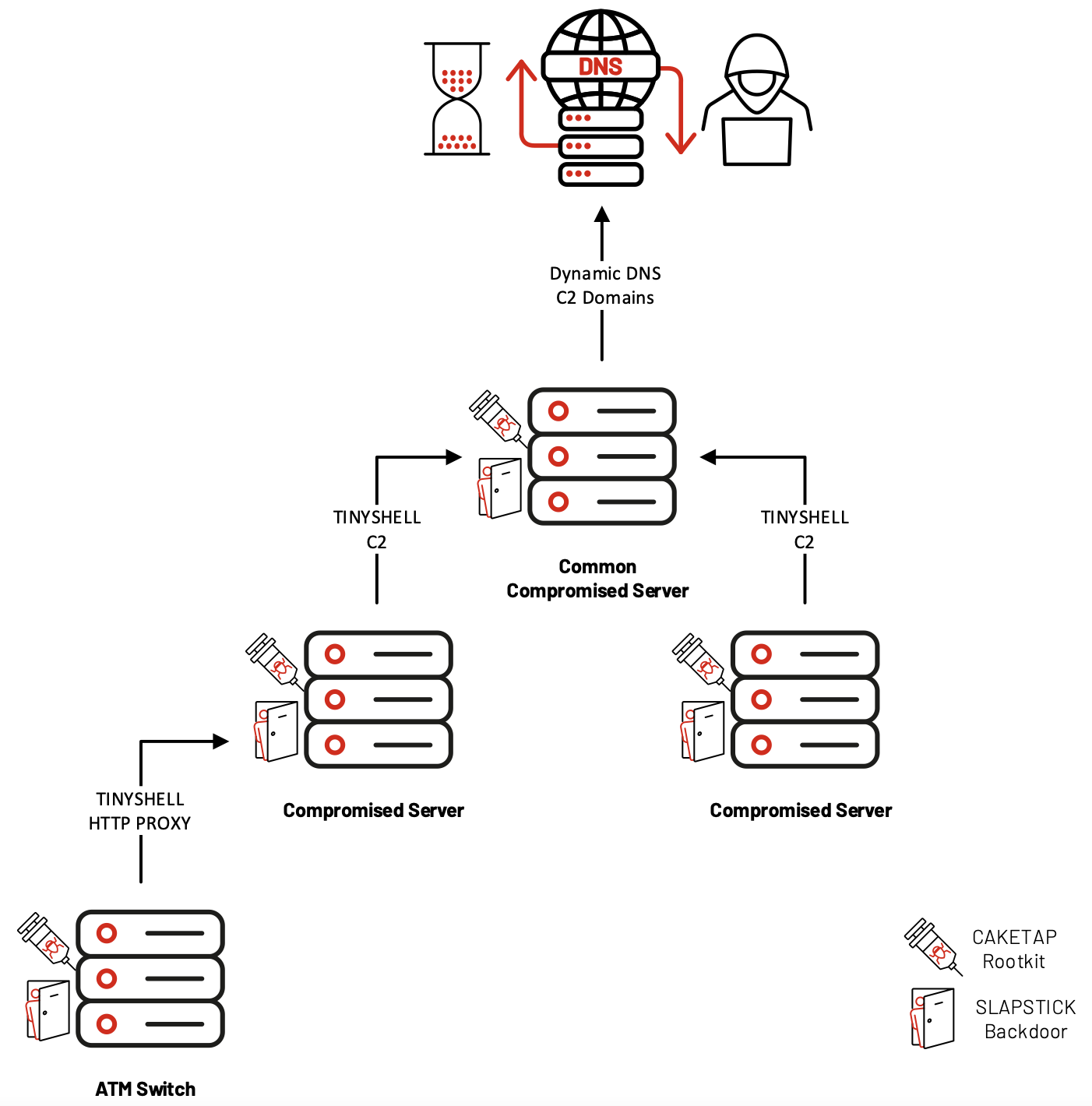
Recently, a new rootkit, which the Mandiant Advanced Practices team have named CAKETAP, was found targeting Oracle Solaris systems running on ATM switch servers. This rootkit is a Unix kernel module that performs several malicious tasks to aid attackers—Mandiant tracks it as UNC2891 (aka LightBasin)—in conducting fraudulent ATM transactions.
CAKETAP has an impressive list of stealth capabilities to hide its presence and activities. It hides network connections, processes, and files. It removes itself from a list of loaded modules on execution and updates data in the
This rootkit can conduct fraudulent bank transactions by intercepting specific messages—card and PIN verification messages—sent to the ATM system’s Payment Hardware Security Module (HSM). Banks use this tamper- and intrusion-proof hardware component to generate, manage, and validate cryptographic keys for PINs, magnetic stripes, and EMV chips. When threat actors use a fraudulent card on an affected ATM, CAKETAP alters card verification messages to disable card verification. This, in turn, creates a valid response from the HSM.
On the other hand, when a regular ATM user uses a valid card on an affected ATM, CAKETAP stores the verification message from a valid transaction, which essentially says that the card is not fraudulent, and forwards it to the HSM, allowing for routine transactions to continue uninterrupted. CAKETAP sends this stored verification message to the HSM to trick it into allowing a fraudulent transaction by sending the stored message.
“Based on Mandiant’s investigation findings, we believe that CAKETAP was leveraged by UNC2891 as part of a larger operation to successfully use fraudulent bank cards to perform unauthorized cash withdrawals from ATM terminals at several banks,” Mandiant security researchers said in the report.
UNC2891 (aka LightBasin) are financially motivated and uses an arsenal of tools in their ATM attack campaigns: two of which are backdoors called TINYSHELL and SLAPSTICK; two decryptors called STEELCORGI and STEELHOUND; a network reconnaissance toolkit named SUN4ME; two keyloggers called WINGHOOK and WINGCRACK; and utilities named BINBASH, WIPERIGHT, and MIGLOCLEANER.
Mandiant has noted that, although LightBasin and another threat actor UNC1945have overlapping operational tactics, they cannot readily conclude that they are the same. “For example, it is possible that significant portions of UNC2891 and UNC1945 activity are carried out by an entity that is a common resource to multiple threat actors, which could explain the perceived difference in intrusion objectives—a common malware developer or an intrusion partner, for example,” the report concludes.










