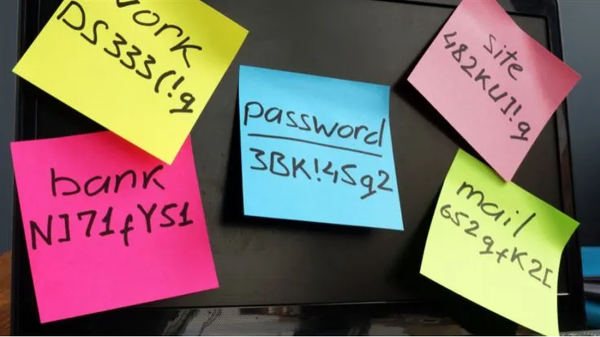
I’m a big advocate of password managers. Granted, there are better alternatives for passwords like passkeys, but if a provider offers nothing but password options, which many do, you can’t do much about that. So, for the time being we seem to be stuck with passwords.
Every reputable password manager claims that they can’t see your passwords, even if they wanted to. But researchers have found that these “zero‑knowledge” cloud password managers are more vulnerable than their marketing suggests.
The researchers also warn that this is not an immediate cause for panic. For a full‑on password leakage to happen, would require rare, high‑end failures such as a malicious or fully compromised server combined with specific design weaknesses and features being enabled.
The underlying “problem” is that most of these password managers are cloud-based. Very handy if you’re working on another device and need access, but it also enlarges the attack surface. Sharing your passwords with another device or another user opens it up to the possibility of unwanted access.
The researchers tested a number of different vendors, including LastPass, Bitwarden, and Dashlane, and devised several attack scenarios that could allow the recovery of passwords.
Weaknesses
Password managers with groups of users
In groups, the sharing of recovery keys, group keys, and admin public keys often means they are fetched from the server without an authenticity guarantee. Meaning that under the right circumstances, an attacker could gain access.
When a group admin has enabled policies such as “auto or manual recovery,” it’s possible to silently change them using a compromised server if there’s no integrity protection on the org “policy blob” (a small configuration file).
Weak encryption on compromised server
Your password manager takes your master password and runs it through PBKDF2 many times (e.g., 600,000 rounds) before storing a hash. But on a compromised server, an attacker could turn down the number of iterations to, say, 2, which makes the master password easy to guess or brute-force.
Account recovery options
On a compromised server an attacker could change the policy blob and change the settings to “auto recovery” and send it to the clients. Switching to auto‑recovery helps the attacker because it lets the system hand over your vault keys without anyone having to click “approve” or even notice it happening.
So, the attacker can turn what should be a rare, user‑visible emergency process into a silent, routine mechanism they can abuse to pull out vault keys at scale or in a stealthy, targeted way.
Backwards compatibility
To avoid locking out users on old clients, providers keep supporting deprecated key hierarchies and non‑AEAD (Authenticated Encryption with Associated Data) modes such as CBC (Cipher Block Chaining) without robust integrity checks. This opens the door to classic downgrade attacks where the server coaxes a client into using weaker schemes and then gradually recovers plaintext.
How to stay safe
We want to emphasize that these attacks would be very targeted and require a high level of compromise. So, cloud password managers are still much safer than password reuse and spreadsheets, but their “zero‑knowledge” claims don’t hold up under nation state‑level type of attacks.
After responsible disclosure, many of the issues have already been patched or mitigated, reducing the number of possible attacks.
Many of the demonstrated attacks require specific enterprise‑style features (account recovery, shared vaults, org membership) or older/legacy clients to be in use. So be extra careful with those.
Enable multi-factor authentication for important accounts, so the attacker will not have enough by just obtaining your password.
Let’s face it, an incognito window can only do so much.
Breaches, dark web trading, credit fraud. Malwarebytes Identity Theft Protection monitors for all of it, alerts you fast, and comes with identity theft insurance.