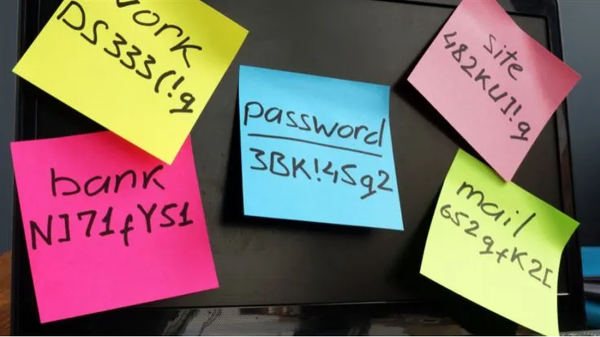
Some time ago, we discussed whether you should allow your browser to remember your passwords.
In that article we mentioned the importance of encryption.
“With a browser password manager, someone with access to your browser could see your passwords in clear text, although Windows can be set to ask for authentication (the same you use at startup of your device).”
The typical behavior of browser password managers is to store passwords encrypted on disk, tied to your user account, and protected by the operating system.
But recently, a security researcher systematically tested every major Chromium-based browser for how they handle credentials in memory. The researcher found that Edge was the only one loading the entire password vault into plaintext process memory at startup, where it remains for the duration of the session.
Chrome and other Chromium browsers were observed to only decrypt a password when needed (autofill or “show password”), not the whole vault, and to use mechanisms like app‑bound encryption for keys. Edge does not use those protections in this context.
So, the researcher decided to write a proof-of-concept (PoC) demonstrating that accessing that vault doesn’t rely on zero-days or complex exploitation. It relies on the relatively simple ability to read process memory, which does require elevated privileges.
But when the researcher reported the issue to Microsoft, the response was underwhelming. The company’s official response was that the behavior is “by design.” The reasoning most likely is that this behavior speeds up sign‑in and autofill, and attackers would already need a compromised machine or elevated access to read RAM, which Microsoft treats as out of scope for this design decision.
Which is basically true. An attacker already needs significant foothold: for example, code execution on the box and the ability to read Edge’s process memory, often requiring elevated privileges. This is not a remote, unauthenticated bug in the browser, but the design makes post‑compromise credential harvesting easier. And it’s a capability many infostealers already have.
It’s just another thing an attacker can do once they’ve compromised your machine. Combined with this academic study from 2024, which found many password managers leak plaintext passwords into memory under some conditions, it leads us to repeat our advice.
Should you allow your browser to remember your passwords?
Your browser password manager gives you ease of use, but that costs you some security. Of course, password managers aren’t foolproof either, so it’s important to decide for yourself where you store your passwords.
If you’re confident the website is safe, and anyone that can access it under your account won’t learn anything new, feel free to store the password in your browser, but disable autofill so you stay in control.
Use MFA where possible. It enormously reduces the risk should someone get hold of your password. And refrain from using the browser password manager to store your credit card details or other sensitive personally identifiable information, such as medical information.
But we’d add that, among the major browsers, Edge appears to be the weakest option if you still choose to use a built‑in password manager.
Stop threats before they can do any harm.
Malwarebytes Browser Guard blocks phishing pages and malicious sites automatically. Free, one click to install. Add it to your browser →