Trojan.Remcos
Short bio
Trojan.Remcos is Malwarebytes’ detection name for a Remote Administration Tool (RAT) targeting Windows systems.
Type and source of infection
Trojan.Remcos typically infects a system by embedding a specially-crafted settings file into an Office document, this allows an attacker can trick a user to run malicious code without any further warning or notification. The code is XML code which allows for any binary with parameters to be executed. This code is used to download and execute the REMCOS RAT.
Aftermath
Trojan.Remcos gives the threat actor full control over the infected system and allows them to run keyloggers and surveillance (audio + screenshots) mode. This means:
- Data/information about the system may have been stolen
- User credentials may have been stolen
- Digital coins may have been stolen
- Affected system may be susceptible to further attacks and/or infection due to a backdoor that was opened
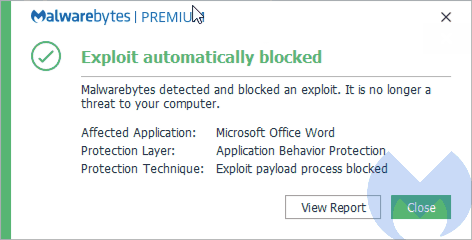
Protection
Malwarebytes protects users from Trojan.Remcos by using Application Behavior Protection.
Home remediation
Malwarebytes can detect and remove Trojan.Remcos without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get startedbutton.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Trojan.Remcos with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

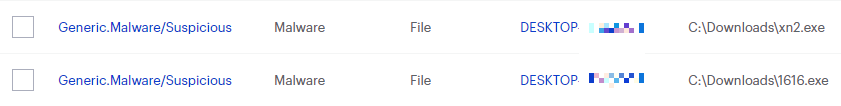
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
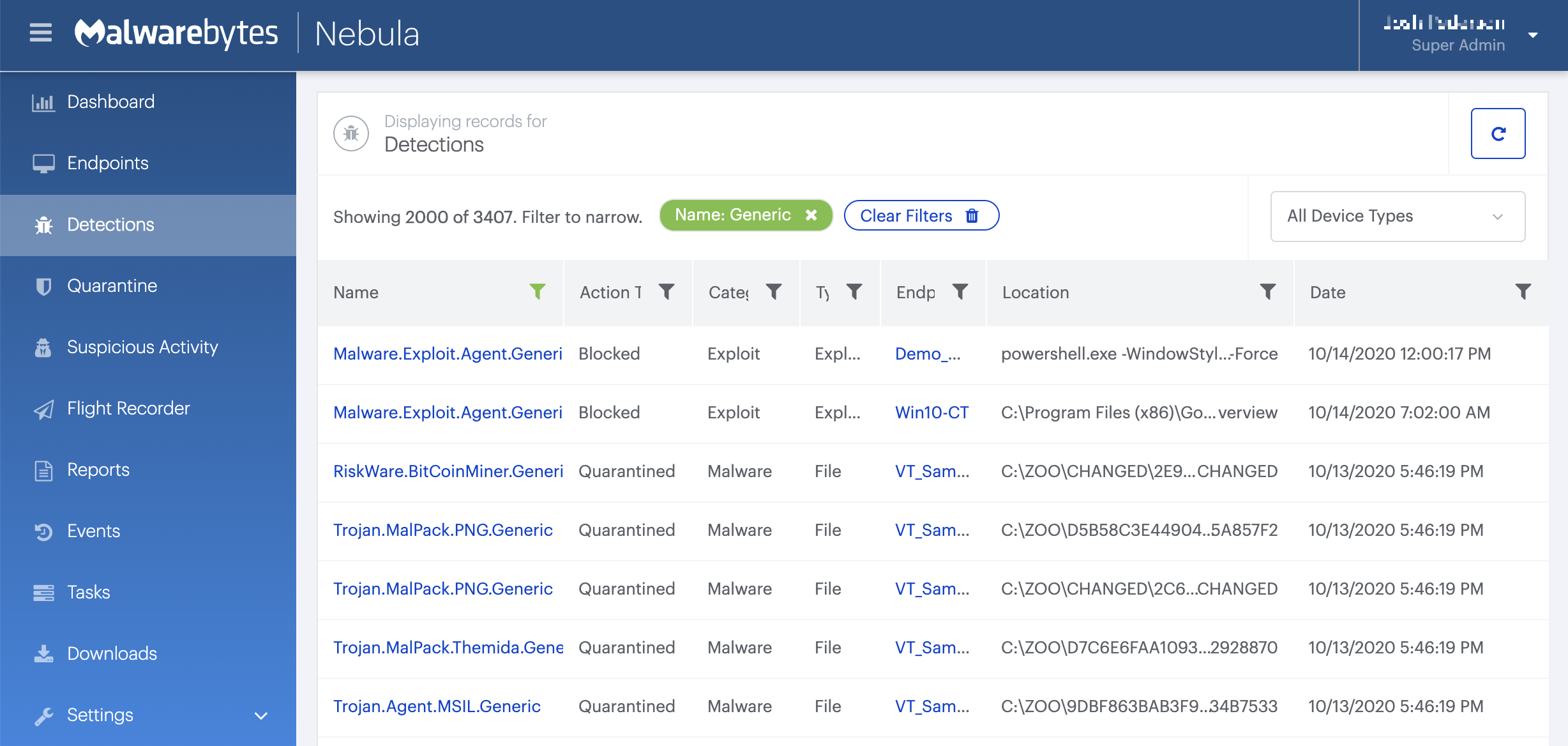
On the Quarantine page you can see which threats were quarantined and restore them if necessary.
Traces/IOCs
Files:
.SettingContent.ms
PcHealths.exe
Hashes:
8710e87642371c828453d59c8cc4edfe8906a5e8fdfbf2191137bf1bf22ecf81
fc0fa7c20adf0eaf0538cec14e37d52398a08d91ec105f33ea53919e7c70bb5a
ff64d7dc2f60fd79304639393cf70fed82e3eb1395d9f331ba123bd4e5f75923





