Cybersecurity researchers discovered a new ransomware last month called RegretLocker that, despite a no-frills package, can do serious damage to virtual hard disks on Windows machines.
Through a clever trick, RegretLocker can bypass the often-long encryption times required when encrypting a machine’s virtual hard disks, and it can close any files currently opened by a user to then encrypt those files, too.
Chloé Messdaghi, vice president of strategy at Point3 Security, described RegretLocker as having “broken through the speed-of-execution barrier for encryption [of] virtual files.”
She continued: “[RegretLocker] actually seizes the virtual disk and is much faster in execution than previous ransomware attacking virtual files.”
Despite the ransomware’s state-of-the-art machinery, its appearance remains quite plain.
RegretLocker does not offer its victims a lengthy ransomware note—a common practice for many ransomware types today—and it asks victims to contact threat actors through an email address. That email address is hosted on CTemplar, which, according to Silicon Angle, is an anonymous email hosting service based in Iceland.
The short note that victims receive, titled “HOW TO RESTORE FILES.TXT” contains the following text:
“Hello, friend.
All your files were encrypted.
If you want to restore them, please email us : petro@ctemplar.com”
As of Tuesday, our threat intelligence team only knew of one in-the-wild reported sample, with no known or reported victims. However, this ransomware should still be watched because of its ability to quickly encrypt virtual hard disks, a potential breakthrough in ransomware capabilities.
Often, ransomware avoids any attempts to encrypt virtual disks found on machines because those virtual disks can be enormous in size, and the time to encrypt those files would simply delay the ransomware’s purpose—to get into a machine and lock it up.
RegretLocker treats virtual disks differently, though. It utilizes the OpenVirtualDisk, AttachVirtualDisk, and GetVirtualDiskPhysicalPath functions to mount virtual disks as physical disks on Windows machines. Once the virtual disk has been mounted, RegretLocker encrypts the disk’s files individually, which speeds up the overall process.
RegretLocker’s virtual hard disk mounting capabilities potentially came from research that was recently published on GitHub by the security researcher smelly__vx. The researchers at MalwareHunterTeam also analyzed a sample of RegretLocket and found that it can run offline as well as online.
Further, RegretLocker can tamper with the Windows Restart Manager API to terminate active programs or Windows services that keep files open. According to IT Pro Portal, the same API is utilized by other ransomware types, including Sodinokibi, Ryuk, Conti, Medusa Locker, ThunderX, SamSam, and LockerGoga. Files encrypted with RegretLocker use the .mouse extension.
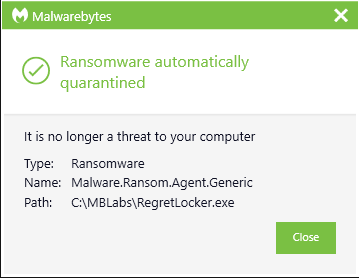
Malwarebytes users should know that we protect them from this new threat, as shown below.