UPDATE: February 12, 2021
It has come to our attention that there is another bad actor in this story.
Apparently, the original publisher, LAVABIRD LTD, is not the bad actor. It is instead an account under the name “The space team.” Nevertheless, there is evidence that updates of Barcode Scanner by either publisher results in a malware infection of Android/Trojan.HiddenAds.AdQR.
Here is a breakdown of all the known infected versions of Barcode Scanner with the corresponding upload date on the Google Play store and the corresponding publisher:
- November 27th, 2020: Barcode Scanner v1.67, publisher LAVABIRD LTD
- December 4th, 2020: Barcode Scanner v1.68, publisher LAVABIRD LTD
- December 7th, 2020: Barcode Scanner v1.69, publisher The space team
- December23rd, 2020: Barcode Scanner v1.71, publisher The space team
- December31st, 2020: Barcode Scanner v1.73, publisher The space team
- December31st, 2020: Barcode Scanner v1.75, publisher The space team
- January 5th, 2020: Barcode Scanner v1.75, publisher The space team and last known malware-infected version released
- Some time thereafter Google Play removed Barcode Scanner from its store
To get the full story on this saga, you can also read our full-length blog on our investigation into who owned this app and who is likely responsible for the malicious changes. Read the story here: Who is to blame for the malicious Barcode Scanner that got on Google Play?
Clearing some other things up
We’d like to take some time clearing other things up based on comments left here on the blog. We appreciate all the feedback from our patrons and we’d like to address some of the issues raised.
First, to clarify, there are many, many clean, legitimate barcode/QR scanners on Google Play. We overlooked that the generic nature of the name Barcode Scanner would trigger panic that your barcode scanner could be the one we were referring to. Barcode/QR scanners have long been targets for exploitation due to the fact that just about everyone that uses an Android device installs a Barcode/QR scanner. For this reason, exploitation of barcode/QR scanners has occurred since the beginning of mobile malware. This was just one individual, isolated case of a barcode/QR scanner being exploited. I cannot overstate that most barcode/QR scanners on Google Play are clean and safe to use.
If you are worried that you have this barcode scanner installed, here is the behavior you would experience on your mobile device. Your default browser opening, all by itself, to web redirects. Keep in mind that web redirects could also be browser related, and we suggest clearing your browser history and cache first and foremost. If the issue persists and Malwarebytes for Android does not detect, post up on our forums or submit a support ticket. We can address the issue there.
Next, clarification of Rocket Cleaner – System Optimizer. Within our short video, the web redirect ends with a Google Play webpage of Rocket Cleaner – System Optimizer. We would like to make it clear that Rocket Cleaner – System Optimizer is a clean, safe app found on Google Play.
The malware authors are paid based on clicks from web redirects, not by infecting people with other malware. Not to say that some of these redirects may try to download malware, but there is no evidence of that here. Each web redirect is a small payment. The redirect could have easily opened any number of clean Google Play apps. That does not mean that the app that is the endpoint of the redirect is itself malicious.
Original blog, published February 5, 2021
Late last December we started getting a distress call from our forum patrons. Patrons were experiencing ads that were opening via their default browser out of nowhere. The odd part is none of them had recently installed any apps, and the apps they had installed came from the Google Play store. Then one patron, who goes by username Anon00, discovered that it was coming from a long-time installed app, Barcode Scanner. An app that has 10,000,000+ installs from Google Play! We quickly added the detection, and Google quickly removed the app from its store.
Simple scanner turns evil
Many of the patrons had the app installed on their mobile devices for long periods of time (one user had it installed for several years). Then all of sudden, after an update in December, Barcode Scanner had gone from an innocent scanner to full on malware! Although Google has already pulled this app, we predict from a cached Google Play webpage that the update occurred on December 4th, 2020.
Malicious intent
The majority of free apps on Google Play include some kind of in-app advertizing. They do this by including an ad SDK to the code of the app. Usually at the end of the app’s development. Paid-for versions simply do not have this SDK included.
Ad SDKs can come from various third-party companies and provide a source of revenue for the app developer. It’s a win-win situation for everyone. Users get a free app, while the app developers and the ad SDK developers get paid.
But every once in a while, an ad SDK company can change something on their end and ads can start getting a bit aggressive. Sometimes even landing the apps that use it in the Adware category. When this happens, it is not the app developers’ doing, but the SDK company. I explain this method to say that in the case of Barcode Scanner, this was not the case.
No, in the case of Barcode Scanner, malicious code had been added that was not in previous versions of the app. Furthermore, the added code used heavy obfuscation to avoid detection. To verify this is from the same app developer, we confirmed it had been signed by the same digital certificate as previous clean versions. Because of its malign intent, we jumped past our original detection category of Adware straight to Trojan, with the detection of Android/Trojan.HiddenAds.AdQR.
Bad behavior
The toughest part of malware analysis can be replicating what our users are experiencing. That wasn’t a problem with Barcode Scanner, it went into action within minutes of install. Watch the short video below to see its malicious behavior:
Removed from Play, but not from mobile device
Removing an app from the Google Play store does not necessarily mean it will be removed from affected mobile devices. Unless Google Play Protect removes it after the fact, it remains on the device. This is exactly what users are experiencing with Barcode Scanner. Thus, until they install a malware scanner like Malwarebytes for Android, or manually remove the app, it will continue to display ads.
Lying dormant
It is hard to tell just how long Barcode Scanner had been in the Google Play store as a legitimate app before it became malicious. Based on the high number of installs and user feedback, we suspect it had been there for years. It is frightening that with one update an app can turn malicious while going under the radar of Google Play Protect. It is baffling to me that an app developer with a popular app would turn it into malware. Was this the scheme all along, to have an app lie dormant, waiting to strike after it reaches popularity? I guess we will never know.
Update: February 8, 2021
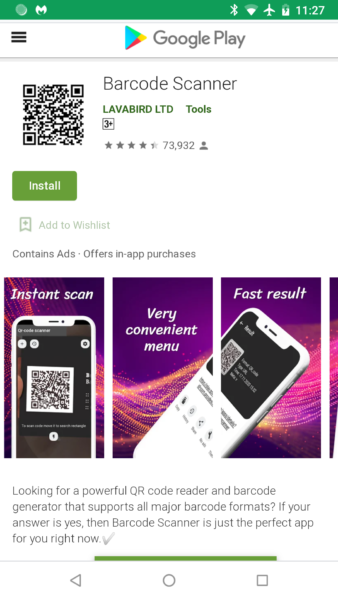
Per user request, we like to provide the Google Play link to the exact Barcode Scanner in question: https://play.google.com/store/apps/details?id=com.qrcodescanner.barcodescanner
We apologize that this was not originally provided. We usually do not provide Google Play links that no longer exist. However, because there are so many other legitimate barcode and QR scanners on Google Play, we understand how this information can help eliminate confusion. In addition, the exact publisher is LavaBird LTD, as shown in the Google Play screenshot. We would also like to further point out that the behavior of the malware is opening the default web browser by itself, without user interaction. This is different from web redirects that occur while actively browsing the web. We hope this clears up any confusion.
App Information
Publisher:LavaBird LTD
App Name:Barcode Scanner
MD5:A922F91BAF324FA07B3C40846EBBFE30
Package Name:com.qrcodescanner.barcodescanner
Google Play URL:https://play.google.com/store/apps/details?id=com.qrcodescanner.barcodescanner