SweepWizard, an obscure app apparently created by ODIN Intelligence and used by more than 60 law enforcement departments, has a flaw: According to an ethical hacker, a misconfiguration in the app’s API (application programming interface) caused it to unintentionally leak to the open internet a trove of very sensitive data on police sweeping operations, including details about the officers involved in them and the suspects, several of whom were juveniles at the time of sweep. One doesn’t need a legitimate account or access to view these data but a single, specific URL.
Wired was the first to reveal SweepWizard’s serious flaw. In the wrong hands, the report said, the data could tip off potential suspects as to when and where they would be raided—something law enforcement doesn’t want to happen.
The data included geographic coordinates of suspects’ homes; time of raids; suspects’ Social Security numbers; demographic information of individuals (height, weight, eye color, and whether they’re unhoused or not); and names, phone numbers, and email addresses of police officers who were part of the operations. We’re talking about 5,770 suspects, hundreds of officers, and around 200 operations.
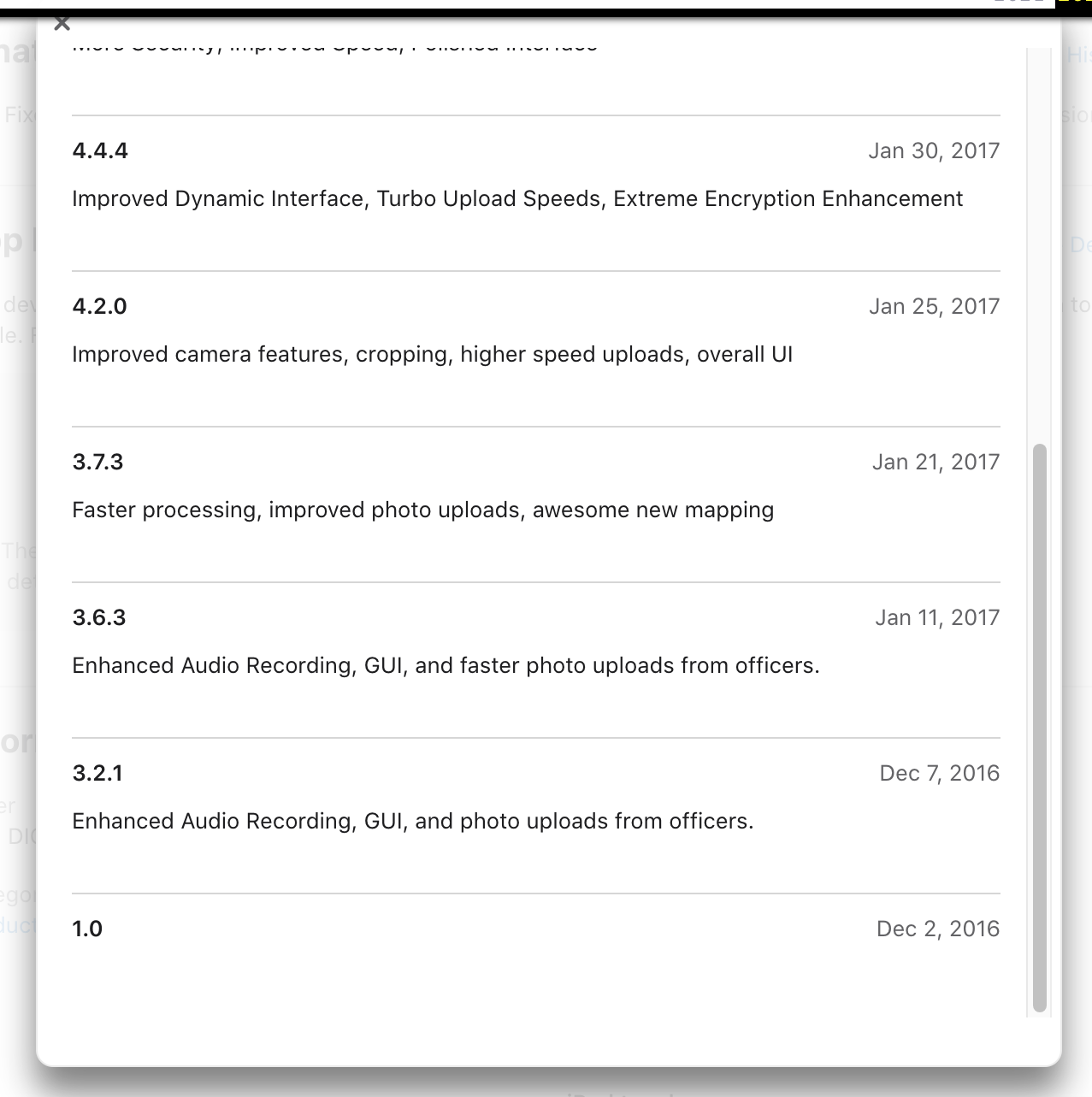
Although version 1 of SweepWizard has been available for download from the Apple App Store since 2016, according to archived information, Wired could access sweep data as far back as 2011. The report mentioned (and we have confirmed this) that SweepWizard’s standalone website was around that same year.
Malwarebytes Labs also found archived information showing the app’s media features, such as audio recording and image uploading and cropping. However, it’s not clear if any media data was being publicly exposed.
Since Wired’s report, some departments using SweepWizard have already suspended its use until a thorough investigation is complete.
In a statement, Captain Kelly Muniz of the Media Relations Division of the Los Angeles Police Department (LAPD) said:
“[T]he department is working with federal law enforcement to determine the source of the unauthorized release of information, which is currently unclear. At this point in the investigation, it has not been determined if the third-party application or another means is the source of the unauthorized release.”
Erik McCauley, CEO and founder of ODIN Intelligence, told Wired
“ODIN Intelligence Inc. takes security very seriously. We have and are thoroughly investigating these claims. Thus far, we have been unable to reproduce the alleged security compromise to any ODIN system. In the event that any evidence of a compromise of ODIN or SweepWizard security has occurred, we will take appropriate action.”
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.










