1. Set up two-factor authentication
Do this for as many of your online accounts as you can, especially the major ones like your email and social media accounts. Two-factor authentication (2FA) adds an extra step of protection and makes it much harder for attackers to login as you. We recommend using authenticator apps or physical security keys, but sometimes SMS is the easiest option and that’s fine. In most services you won’t have to enter the 2FA code every time, only when using a new device.
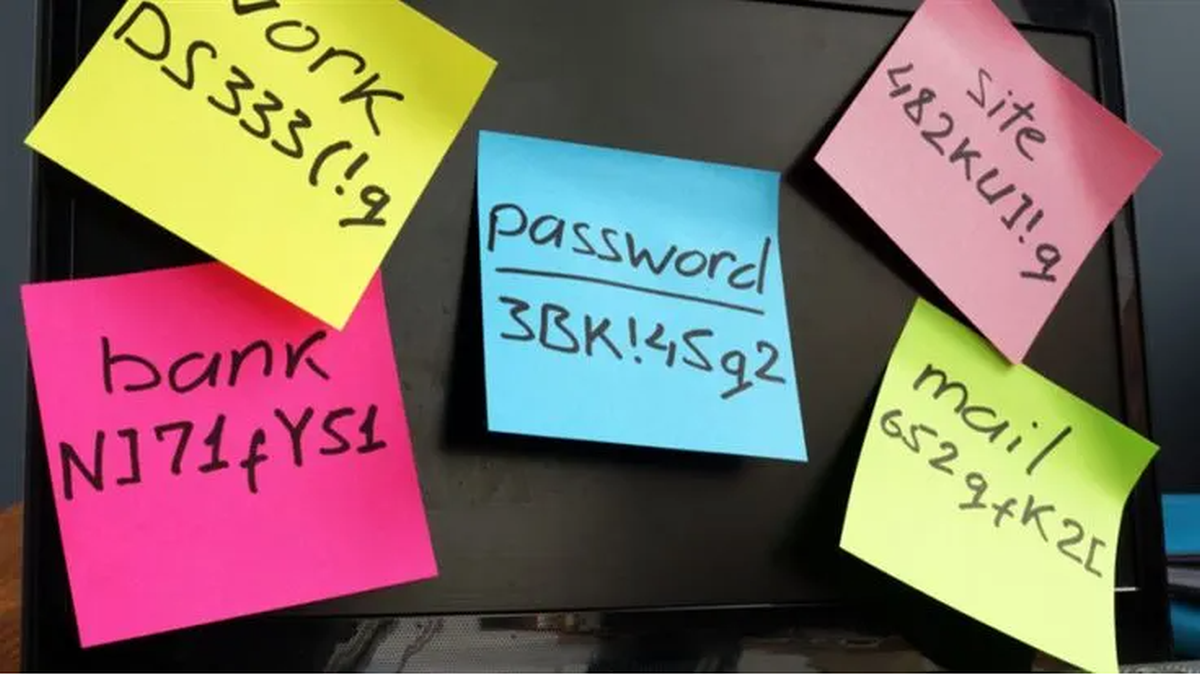
2. Use a different password for every account
If your password is breached on one site, cybercriminals can use that login information to access your other online accounts that use the same passwords. If you use a different password for each account they can’t do this. Make sure your passwords are long (15 characters or more is good) and use a mix of upper and lower case characters, numbers and symbols too.
To make it easy, you can chose a phrase or a line from a song you like (for instance: DancingInTheMoonlight1999!). You can also use a password manager built-in on your browser, or a stand-alone password manager (see below). If you’ve received a notification from Google, Malwarebytes or any other service telling you your password has been exposed make sure to not use it or any variation of it again for any of your accounts.
3. Use a password manager
Making different and complicated passwords for each and every online account you have is one thing, but remembering them all is a lot more difficult. That’s why we use a password manager, and why you should too. It will generate passwords for you and then remember them all. Choose a vendor you trust for it, or simply use Apple or Google.
4. Keep software and hardware up to date
Make sure your computer, phone, browser, apps and other programs are always on the latest version. If someone finds a security bug, the company that makes that software or hardware will release a new version with a patch for the bug. If you’re not on the latest version, you will be vulnerable. We know it can sometime be a hassle to update the version – but it’s not only about the latest features, in many cases it’s about keeping you safe!
5. Double check everything
Got an email or SMS saying your delivery has been delayed that asks you to click on a link? Double check that you are expecting a delivery from where it says it’s coming from. Got a message from a friend on Facebook that seems off? Double check via text or phone that it is really them. Is your CEO suddenly asking you to buy $5000 of gift cards on the company credit card? Double check that it really is the CEO (it probably isn’t). There’s a ton of scams out there and they are getting more and more sophisticated with time, you just have to stay vigilant and aware of it.
6. Be careful who you share your real data with
Does that restaurant you’re making a reservation with really need to know your actual date of birth? Does that shopping site really need to know your mother’s maiden name as a password reset question? Consider carefully where you share your data and keep in the back of your mind that the service you are using could be breached. If it is breached, what of your information would be taken? If you can use false information, we really encourage you to do that. Pro-tip: create an “avatar online identity” for yourself with a separate email, date of birth and information you remember and use this information for vendors that don’t require your real identity.
7. Cover your camera
When your camera isn’t in use, make sure you cover it with a physical cover. You can get webcam covers that slide open and shut to make it easy for you to use your camera when you like, and they look a lot nicer than a sticking plaster! Hackers have been known to take over webcams and take snapshots – so sometimes a physical cover is our last line of defense!
8. Use an identity monitoring solution
Identity theft is a real challenge today, including stealing your credit and even opening new lines of credit in your name. Identity monitoring alerts you if your personal information is found being traded illegally online, and helps you recover after. Malwarebytes Identity Theft Protection can help with this.
9. Check what data of yours has already been exposed
It’s very likely that your personal information has already been involved in a breach, but you might be wondering how much information can be gained about you from all the pieces of data about you that’s online—aka your digital footprint. We created a tool that will show you just that. You enter your most commonly-used email address, we’ll run a scan and then we’ll send you the results. Try the free scan now.
10. Use security software
Finally, make sure you have protected your devices with security software. It doesn’t take long and it’s such a basic step we must all do. Malwarebytes Premium detects or blocks over 95 million pieces of malware a day so we definitely have you covered. We protect Windows, Mac, Chrome, Android, and iOS.
Let’s face it, an incognito window can only do so much.
Breaches, dark web trading, credit fraud. Malwarebytes Identity Theft Protection monitors for all of it, alerts you fast, and comes with identity theft insurance.