Tech support scams follow a simple business model that has not changed much over the years. After all, why change a recipe that continues to yield large profits.
We see countless such campaigns and block them indiscriminately to protect our customers from being defrauded by a fraudulent tech support agent over the phone. Every now and again, our attention is caught by one that is larger in volume due to upstream traffic.
Their modus operandi is as classic as it comes: To target users to adult sites and redirect them to fake warning pages via malicious ads. The threat actors behind this malvertising business appear to have been quite successful at following the same pattern over and over.
In this blog, we break down what we call the IP2Scam tech support scheme, by going back in time to track previously used infrastructure. We highlight that these fraudsters have been active for quite some time and how we found a way to track them more closely and identify their next move.
Why bother with domain name registration?
This tech support scam campaign has been seen by many people (victims and scambaiters alike) and can be recognized by its URL scheme because it always consists of an IP address, instead of a registered domain name.
http://155.138.141[.]187/systemerror-win-chx/?phone=.&
Everything is a commodity when it comes to malicious infrastructure and scammers know quite well that their domain names will be blacklisted pretty quickly. In this case, they simply buy a new virtual server and rotate ad infinitum.
There is nothing particular about this fake notification also known as a ‘browlock’, for browser locker. It is customized based on the browser’s user agent to display a slightly different template for Windows, Mac and the choice of Chrome or Firefox.
Browlocks IP space
We took about 10 months’ worth of telemetry and sorted all the servers’ IP addresses associated with this scam. This gave us a better idea of where the scammers like to host their infrastructure. We have shared our data with both Digital Ocean and The Constant Company (Choopa) and thank them for their help in this effort.
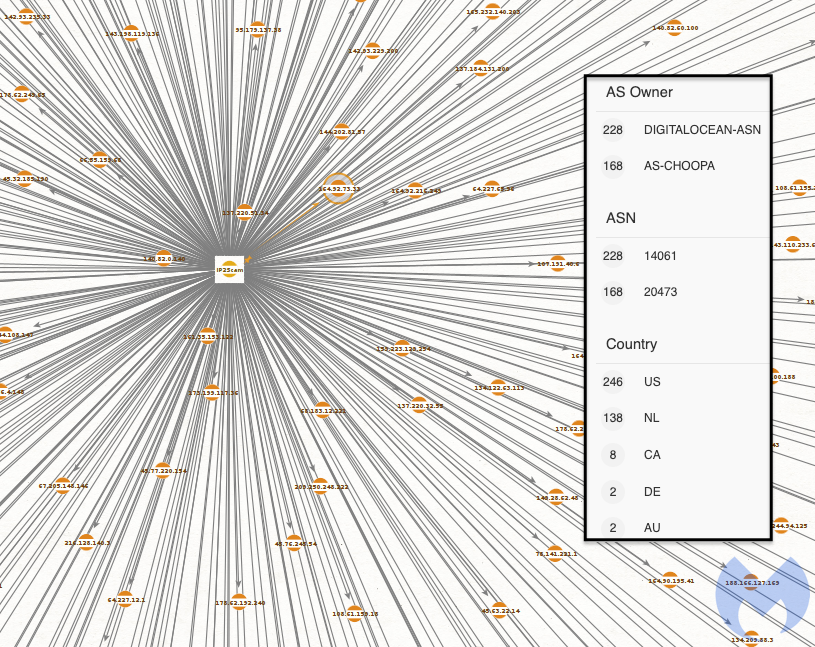
New servers come up as needed and are pushed dynamically via ongoing malvertising campaigns.
Malvertising flow
As with many other malvertising campaigns, the scammers prey on visitors to adult websites and perform a very simple cloaking technique to hijack traffic and redirect it to their browser locker.
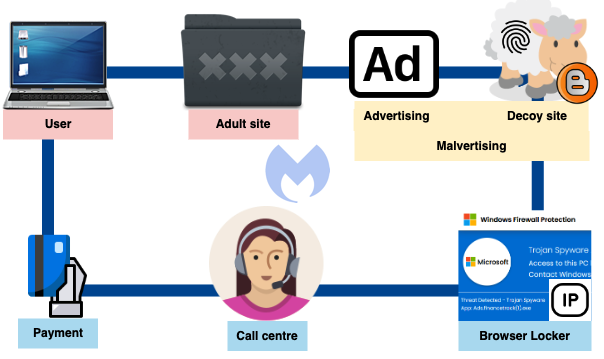
The cloaking part consists of a decoy website named after a known brand whose purpose is to filter traffic and redirect if the user matches a certain set of criteria. For example we see bongaecams[.]xyz impersonating BongaCash and being used to redirect to the browlock
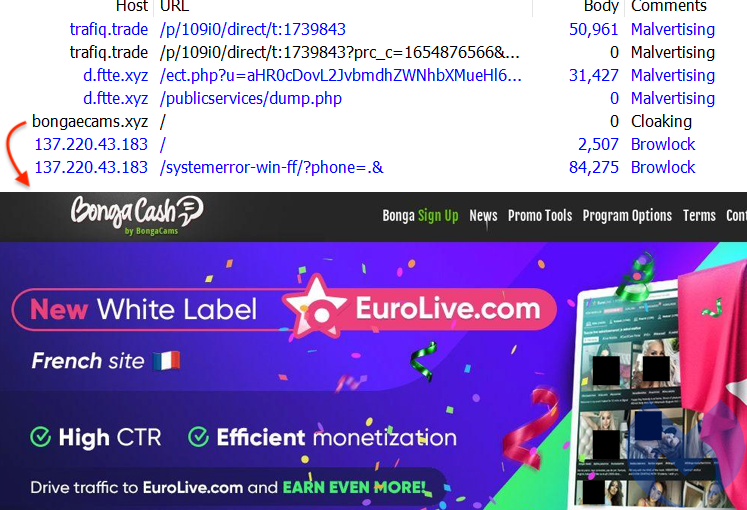
Other impersonated brands include Tom’s Guide and the New York Post. When a potential mark is identified, they are redirected to the browlock, otherwise they simply see some other content.

Those cloaking sites tend to remain active for longer periods of time probably because they aren’t malicious in and of themselves. One way to track this campaign is to follow these domains and simply attempt to get the redirect to the browlock IP du jour. We also identified another mechanism (that we won’t share publicly as to not give it away) that can programmatically retrieve new browlock server IP addresses as they come.
Reporting and take down
Tech support scammers are well aware that a number of people are after them and yet they often feel safely out of reach.
While not as good as actual arrests by local police, we hope to make it as difficult as possible for them to bring up new servers and defraud victims by disrupting their lead generation flows.
We would like to thank DigitalOcean and the Constant Company for their help.
Indicators of Compromise
Cloaking domains
newsjump[.]xyz
newsmaven[.]xyz
newsdeals[.]xyz
xposednews[.]xyz
taclenews[.]xyz
crypcoinsnews[.]xyz
chapternews[.]xyz
kathnews[.]xyz
tomsguides[.]xyz
npost[.]xyz
maanews[.]xyz
tomguide[.]xyz
exposednews[.]xyz
hrmaclenews[.]xyz
bongaecams[.]xyz
clarkdeals[.]xyz
bongmecams[.]xyz
bongocams[.]xyz
eronews[.]xyz
Browlock IPs by ASN and timestamp