Short bio
A bot, also known as a zombie, automatically performs a task or set of tasks usually under the command and control of a remote administrator, or what is known as a bot master.
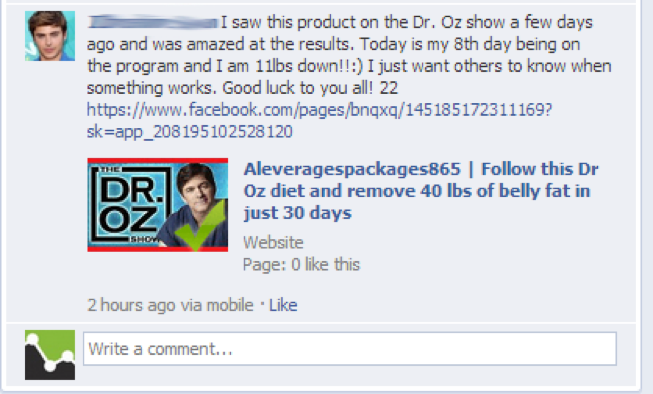
Social media bots have been used by spammers/scammers on social media sites as a method of pushing their spam/scam to numerous accounts. They do so by increasing the number of followers on their bot accounts, increasing likes/views, and also as a method to mass distribute malicious content.
History
When we think about bots, usually botnets and Denial of Service attacks come to mind. But bots are also being used by scammers, political regimes, marketers, and even celebrities via social media sites like Twitter, which averages over 200 million users.
More recently, the Hammertoss malware is known to leverage many common malware tactics to obfuscate the malware’s activity, which include obtaining commands from social media networks like Twitter, also automatically visiting different Twitter handles on a schedule. Furthermore, Hammertoss has hundreds of Twitter accounts it communicates with, which can be an indicator of bot activity on these accounts.
There’s also the infamous Twitter bot, which is used to create automated posts and automatically follow users on Twitter. Twitterbots have been used for spam, for luring of clicks on promotional links, and for automatically retweeting in response key word/phrase tweets.
Twitter bots have been suspected of being used to promote presidential campaigns in Mexico and Russia. In both instances, Twitter accounts were used to send out mass tweets in support of specific political candidates.
Common infection method
Unpatched systems, software vulnerabilities, zero-day vulnerabilities, weak or lack of passwords, malicious websites, social engineering techniques, and weak security practices are avenues of infection. Social media bots can be purchased or created by scammers. Scammers then conduct user reconnaissance to select a specific target criteria for their campaign, such as software developers, activists, employees of an organization they are targeting, and ensure targets are active and human through further reconnaissance. Threat actors then use bots for mass distribution of their attack, using different strategies and tactics, such as sending/tweeting malicious shortened URLs > sent to a malicious site > download of malicious content.
Associated families
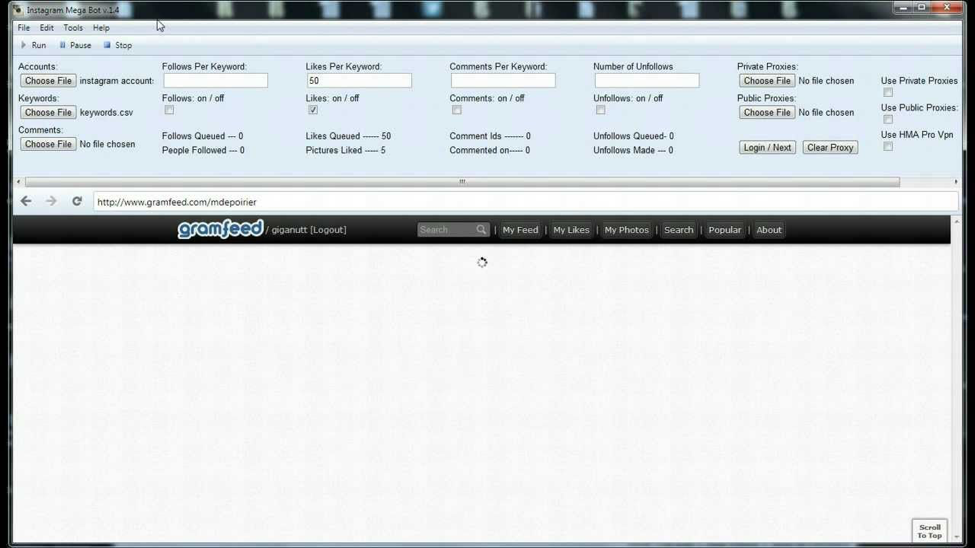
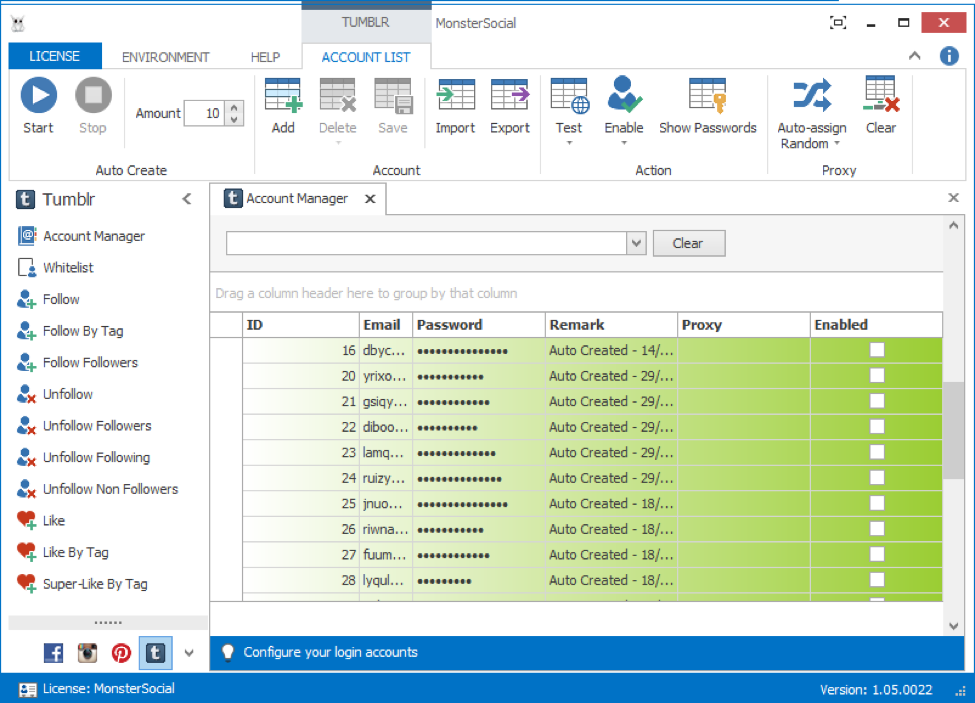
There are a number of programs that can be considered Social Media Bots. Some well-known programs include Instagram Mega Bot, MonsterSocial, and Senuke.
Remediation
Due to the fact that Social Media Bots are not an infection, and pose little danger in-and-of themselves, there are no remediation tactics available. Users are simply advised to not click links if not 100% sure of the origin of the content or the final destination of the URL.
Aftermath
Users may face various risks if the attempted deception of the Social Media Bot content is successful. The risks range from none to great depending on the complexity and the intent of the person behind the campaign.
Avoidance
Avoid clicking links or generating false beliefs from content located on public spaces. Verify the authenticity of the person responsible for generating the content, and confirm the accuracy of information posted before providing information or engaging in practices which may endanger financial resources. Never click links from unknown persons and never install software at the recommendation of unknown persons.
Examples
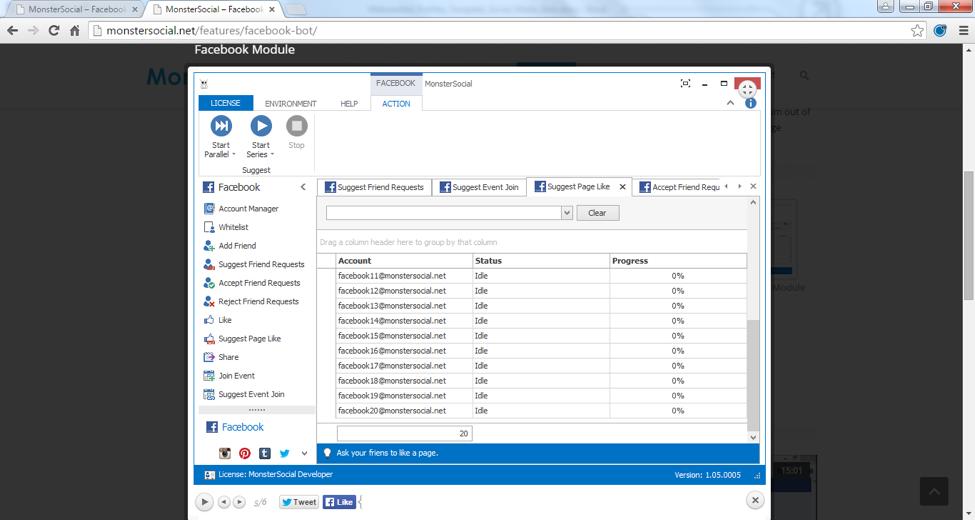
“MonsterSocial allows you to automate multiple profiles on multiple social networks doing multiple features using multiple proxies!”
MonsterSocial sells Facebook, Instagram, Tumblr, Pinterest, and Twitter bots. MonsterSocial boasts to scammers that they can use their product for “guiding traffic from social networks to wherever you want. Hint: PPV, PPC and PPD services!”
Testimonials
“I’m making 300 USD a day by spreading my PPD links with the Facebook module!”
MonsterSocial Facebook Bot features:
- Ask all the friends of all your accounts to like a specific page by sending a personal notification
- Ask all the friends of all your accounts to join a specific event by sending a personal notification
- Ask all the friends of your accounts to add a specific friend to their friends list by sending a personal notification
- Like a status, picture or page with all your accounts
- Comment on a status, picture or page with all your accounts
- Share a specific status on the timelines of all your accounts
- Add a specific profile to the friends lists of all your accounts
- Join a specific event with all your accounts
- Accept all pending friend requests with all your accounts
- Reject all pending friend requests with all your accounts
- Exclude specific profiles from suggestions using a whitelist
- Import accounts in the account manager
- Test accounts in the account manager
- Assign proxies to your accounts in the account manager
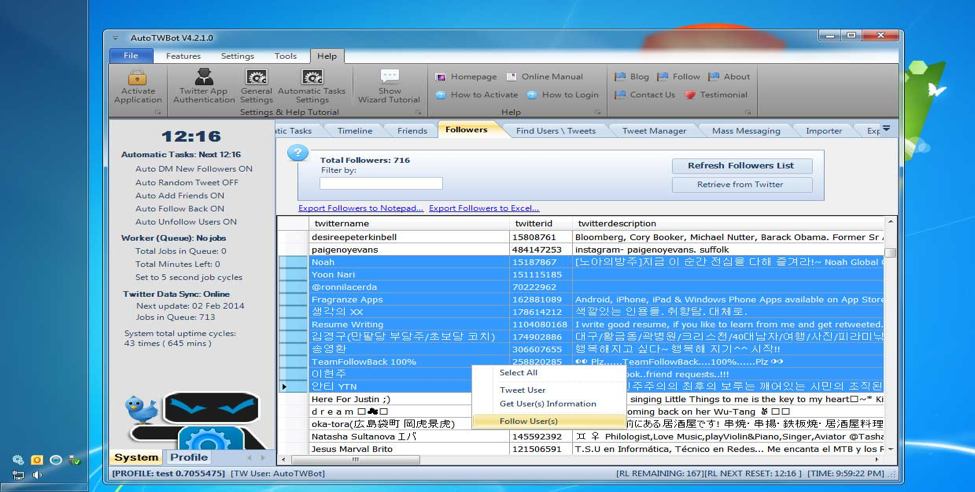
AutoTWBot includes a mix of automated and mass Twitter features, such as:
- Automatic Follow Back New Followers
- Automatic Unfollow Users Not Following You
- Automatic Add Targeted Users
- Automatic Direct Message New Followers
- Automatic Random Tweeting
- Automatic add targeted users: This automatic feature allows AutoTWBot to search for tweets provided by the user’s keywords and automatically follow a certain number of people. Great for following targeted Twitter users to get involved with their conversations and build new connections. Also the majority of users you follow on Twitter today will follow you back in good intent.
Screenshots