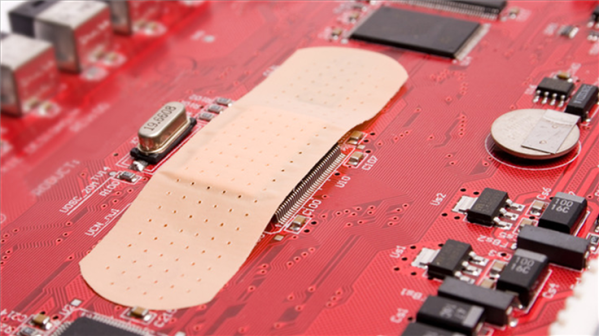
In July’s update for the Android operating system (OS), Google has patched 43 vulnerabilities, three of which are actively exploited zero-day vulnerabilities.
The security bulletin notes that there are indications that these three vulnerabilities may be under limited, targeted exploitation.
If your Android phone is at patch level 2023-07-05 or later then the issues discussed below have been fixed. The updates have been made available for Android 10, 11, 12, 12L and 13. Android partners are notified of all issues at least a month before publication, however, this doesn’t always mean that the patches are available for devices from all vendors.
You can find your device’s Android version number, security update level, and Google Play system level in your Settings app. You’ll get notifications when updates are available for you, but you can also check for updates.
For most phones it works like this: Under About phone or About device you can tap on Software updates to check if there are new updates available for your device, although there may be slight differences based on the brand, type, and Android version of your device.
The Common Vulnerabilities and Exposures (CVE) database lists publicly disclosed computer security flaws. The CVEs listed as actively exploited are:
CVE-2023-26083: a memory leak vulnerability in Mali GPU Kernel Driver in Midgard GPU Kernel Driver all versions from r6p0 – r32p0, Bifrost GPU Kernel Driver all versions from r0p0 – r42p0, Valhall GPU Kernel Driver all versions from r19p0 – r42p0, and Avalon GPU Kernel Driver all versions from r41p0 – r42p0 allows a non-privileged user to make valid GPU processing operations that expose sensitive kernel metadata.
ARM was warned about this vulnerability on March 31, 2023 and stated:
“There is evidence that this vulnerability may be under limited, targeted exploitation.”
CVE-2021-29256: The Arm Mali GPU kernel driver allows an unprivileged user to achieve access to freed memory, leading to information disclosure or root privilege escalation. This affects Bifrost r16p0 through r29p0 before r30p0, Valhall r19p0 through r29p0 before r30p0, and Midgard r28p0 through r30p0.
Both of the above vulnerabilities are present in the ARM Mali GPU, which is the graphics processor of many Android phones. A patch for both vulnerabilities had been issued by ARM, but Google has decided to include them in this month’s Android update.
CVE-2023-2136: An integer overflow in Skia in Google Chrome prior to 112.0.5615.137 allowed a remote attacker who had compromised the renderer process to potentially perform a sandbox escape via a crafted HTML page.
This vulnerability is affecting the Skia 2D graphics library used in Android systems. Skia is an open source 2D graphics library for drawing Text, Geometries, and Images.
It is likely that attackers would use the vulnerability in Skia as a first stage and then use one of the Mali vulnerabilities to complete a device takeover.
Another vulnerability that caught our eye was CVE-2023-21250: a critical vulnerability in the System component that could lead to remote code execution with no additional execution privileges needed and no user interaction is needed for exploitation. Further details were not revealed to give users a chance to install the patch first.
We don’t just report on vulnerabilities—we identify them, and prioritize action.
Cybersecurity risks should never spread beyond a headline. Keep vulnerabilities in tow by using Malwarebytes Vulnerability and Patch Management.