Short bio
Advertising (ad) fraud, also called click fraud or click spam, is a practice by bad actors, specifically dubious advertising networks, wherein they deliberately use automated programs—from simple to sophisticated bots and botnets—to interact with advertisements online. They do this by simulating legitimate users into clicking ads, visiting pages, and (in some instances) creating fake form submissions.
While it is common knowledge that fraud earnings of this sort are inflated via automated means, some claim that a significant portion of ad click traffic is generated by actual people (low-wage workers). Furthermore, some form of fraud involves ads that are never seen in the wild by Internet users and ads that publishers intentionally misrepresent. Regardless of how click fraud is played, the objective of people and organizations behind them varies. The most obvious one is to generate high profit, the less obvious one is to incriminate or damage the profit of competitors.
History
The pay-per-click (PPC) scheme was born shortly after organic SEO (or the natural means of having websites and content found via keywords) was recognized as a marketing channel. Ad fraud in the PPC scheme was first identified in 2001 by Jessie Stricchiola, a search engine marketing pioneer and founder of an SEO company in San Francisco, California.
Common infection method
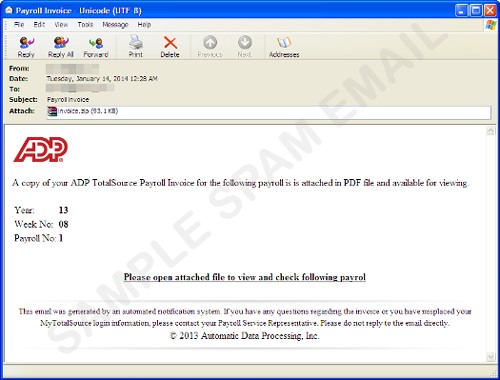
In the case of ad fraud via bots, such pieces of malware may arrive on a system via initial system infection of a worm or Trojan. The malware may also arrive via drive-by download once it finds that target systems are exploitable due to software or browser plugins that are not up to date. Lastly, attaching ad fraud malware to spam has been a potent method of infection as well.
Associated families
- 7cy
- Fiesta
- Kovter
- MIUREF
- Poweliks
- Rerdom
Remediation
Most ad fraud malware is detected by security programs. It’s best to have them updated. Some companies also offer exclusive, stand-alone tools for detecting, removing, and remediating such bots.
It also pays to update all software installed on user systems to avoid such malicious programs exploiting holes that would have been avoided if only they were patched.
Aftermath
More often than not, systems that are infected with clickbots lead to further infection by other malware. This happens when the clickbots request ads from random sources, which may or may not be serving malware. Known infections include ransomware, such as CryptoWall, rootkits, and several Trojan spyware variants. Furthermore, users’ privacy can be compromised as some clickbots are capable of monitoring or tracking browsing behavior.
Avoidance
Keeping installed software on user systems, including the OS, is already a great help in avoiding getting infected by clickbots. It’s also important to keep in mind and continue to practice basic secure computing tips when dealing with suspicious emails, questionable links on social sites, and the like.
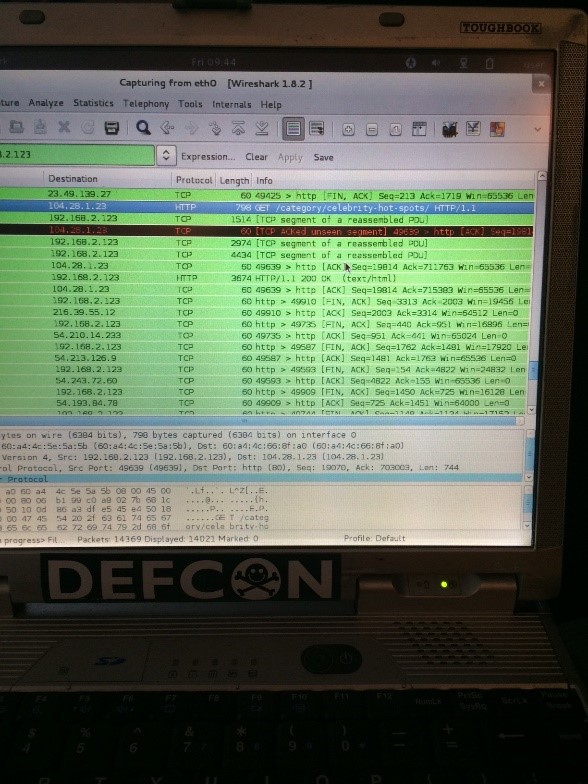
Screenshots