Trojan.Keylogger
Short bio
Trojan.Keylogger is Malwarebytes generic detection name for applications that have the capabilities to harvest keystrokes, screenshots, network activity, and more from affected systems. Trojan.Keylogger may covertly monitor user behaviour and harvest personally identifiable information including names and passwords, keystrokes from emails, chat programs, websites visited, and financial activity.Trojan.Keylogger may be capable of the covert collection of screenshots, video recordings, or the ability to activate any connected camera or microphone. Collected information may be stored locally and later retrieved, or may be transmitted to an online service or location.
Symptoms
Trojan.Keylogger may run as a start-up entry and may be visible as running processes on compromised machines. Alternatively, Trojan.Keylogger may also be configured in a manner which prevents visible processes and start-up entries
Type and source of infection
Trojan.Keylogger may be distributed using various methods. This software may be packaged with free online software, or could be disguised as a harmless program and distributed by email. Alternatively, this software may be installed by an individual with physical or remote access to the computer. Trojan.Keylogger may be installed with or without user consent.
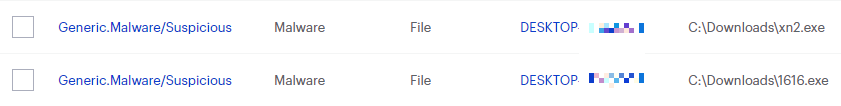
Protection
Malwarebytes blocks Trojan.Keylogger
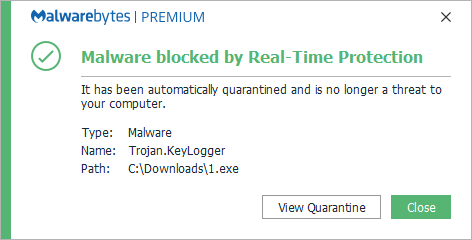
Home remediation
Malwarebytes can detect and remove many Trojan.Keylogger infections without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get startedbutton.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Trojan.Keylogger with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found.
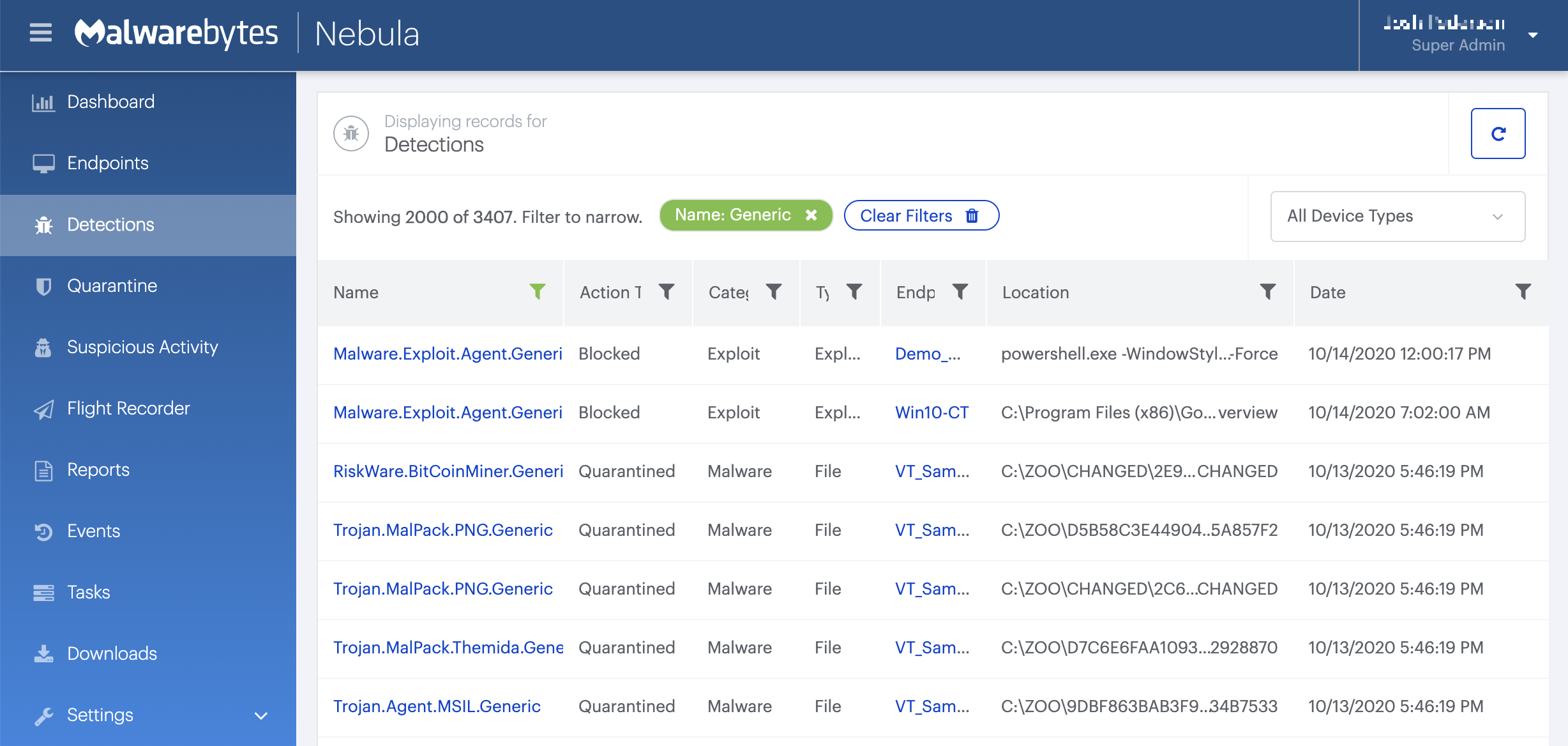
On the Quarantine page you can see which threats were quarantined and restore them if necessary.