Trojan.MetaSploit
Short bio
Trojan.MetaSploit is Malwarebytes’ generic detection name for Trojans that are based on the Metasploit framework.
Type and source of infection
The Metasploit framework is intended as an information security tool to test the vulnerability of computer systems. It is a Ruby based open-source framework that allows penetration testing via command line alterations or GUI. Threat actors sometimes use the framework for malicious activities and build Trojans based on the Metasploit framework.
Protection
Malwarebytes protects users from Trojan.MetaSploit by using real-time protection.
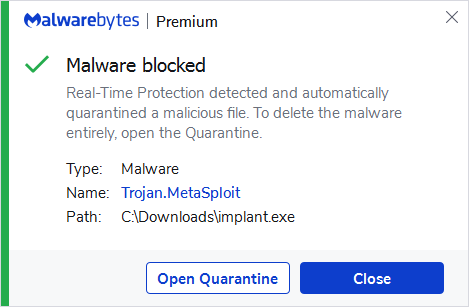
Malwarebytes blocks Trojan.MetaSploit
Home remediation
Malwarebytes can detect and remove Trojan.MetaSploit without further user interaction.
- Please download Malwarebytes to your desktop.
- Double-click MBSetup.exe and follow the prompts to install the program.
- When your Malwarebytes for Windows installation completes, the program opens to the Welcome to Malwarebytes screen.
- Click on the Get startedbutton.
- Click Scan to start a Threat Scan.
- Click Quarantine to remove the found threats.
- Reboot the system if prompted to complete the removal process.
Business remediation
How to remove Trojan.MetaSploit with the Malwarebytes Nebula console
You can use the Malwarebytes Anti-Malware Nebula console to scan endpoints.

Nebula endpoint tasks menu
Choose the Scan + Quarantine option. Afterwards you can check the Detections page to see which threats were found. On the Quarantine page you can see which threats were quarantined and restore them if necessary.





