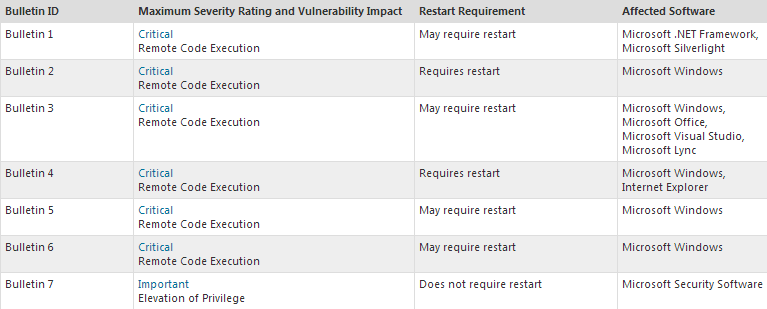
Tomorrow on Patch Tuesday, Microsoft will be issuing security updates that address multiple vulnerabilities across several of its products. This information was provided by an advance notification of the normal security bulletin released monthly by Microsoft.
Six of the seven updates issued on July 9th are deemed “critical,” the highest rating on the company’s severity scale (seen here). Make sure to install the update as soon as it becomes available to remain secure. If you’ve enabled automatic updates from the Control Panel in Windows, you will receive the update as soon as it becomes available.
Vulnerable software includes Windows, Microsoft Office, .NET framework, and more. There is also one additional update for Windows Defender that allows for privilege elevation.
Tavis Ormandy—a security engineer at Google—is credited for the discovery of one vulnerability affecting the Windows kernel, dubbed as a “really cute trick” on his twitter page.
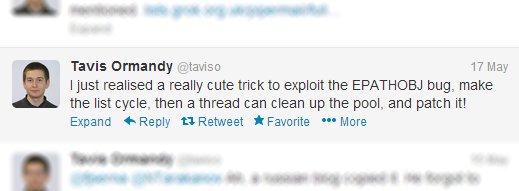
Ormandy later disclosed details of the exploit, but not to Microsoft. Instead, Ormandy posted information on the vulnerability to seclists.org, an Internet security site for researchers. Ormandy believes that publishing this information in public domains will better protect the user, but is that really true?
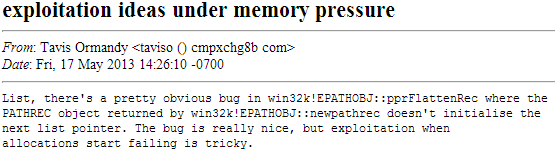
There’s no doubt that cyber-criminals would be eager to get their hands on this exploit code, especially since exploits affecting Windows are not as common as say another flaw in Java or Adobe Reader. In turn, the exploit code could easily be packaged and used in various exploit kits, potentially allowing for execution of arbitrary code, like malware.
Also, let’s not forget the rivalry between Microsoft and Google, which may provide more insight on Ormandy’s decision.
In fact, Microsoft has waged an aggressive marketing campaign against popular Google products and services, like Gmail, the Play Store, and Google Chrome. The company’s recent “Scroogled” ads points fingers at Google for collecting information for the purpose of selling advertisements and possible misuse.
The ads of course have received a lot of mixed reviews from viewers, and it certainly does make Microsoft look a bit desperate when you factor their other ads targeting Google Chrome and lauding Internet Explorer.
However, regardless of that battle, you’ll need to install the update from Microsoft tomorrow when it’s released to stay safe. It will surely be interesting to see if the EPATHOBJ exploit will be used in future exploit packs.
_______________________________________________________________________________
Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and in-depth analysis on current malware threats. He has over 5 years of experience working with US defense intelligence agencies where he analyzed malware and developed defense strategies through reverse engineering techniques. His articles on the Unpacked blog feature the latest news in malware as well as full-length technical analysis. Follow him on Twitter @joshcannell