Some time ago I showcased the Wi-Fi pineapple, a small portable Wi-Fi access point modified with a custom firmware to be used as malicious “Man-In-The-Middle” attacks — all of this of course as part of a sanctioned security evaluations.
As it turns out, there are other projects that are very similar in implementation, if not in philosophy, such as the Piratebox.

Piratebox V1, photo courtesy of David Darts.
David Darts, the chair of the NYU Art Department, started this project when he was looking for a simple way to share files between him and his students. After investigating a possible commercial product to address their need and discovering there simply wasn’t one available at the time he decided to build one, using off the shelf components.
“PirateBox is a self-contained mobile communication and file sharing device,” according to Darts’ how-to webpage. “Inspired by pirate radio and the free culture movement, PirateBox utilizes Free, Libre and Open Source software (FLOSS) to create mobile wireless file sharing networks where users can anonymously chat and share images, video, audio, documents, and other digital content.”
Darts then put the plans to build a Piratebox online and copyleft-ed them. (This is a general method for marking a creative work as freely available to be modified, and requiring all modified and extended versions of the program to be free as well.)
This was to ensure as many people as possible could play with the idea and hopefully expand upon it. It did not take long before enterprising hackers started porting the code to other devices.
David’s original Piratebox was an amalgamation of off-the-shelf devices, and the moniker originated from the lunchbox that he used to hold all the components.
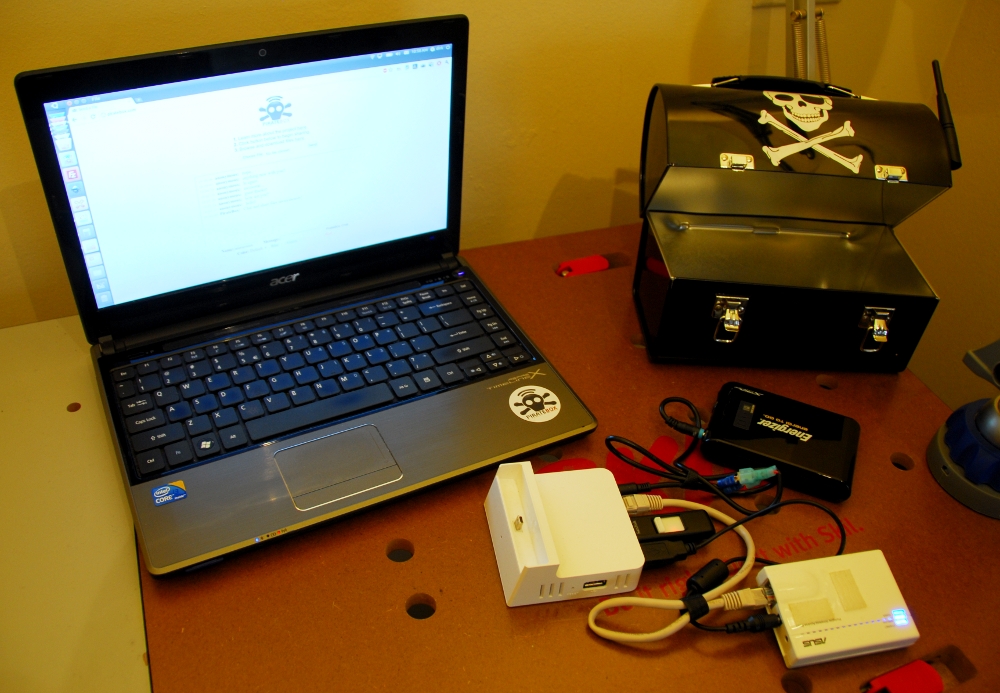
Piratebox V1, photo courtesy of David Darts.
The second version used a DD-WRT Buffalo router, merging some of the components. This meant a much more streamlined package with the router, a battery for supplying power, and a USB stick for disk space. All this contained in a smaller lunchbox in keeping with the pirate theme.
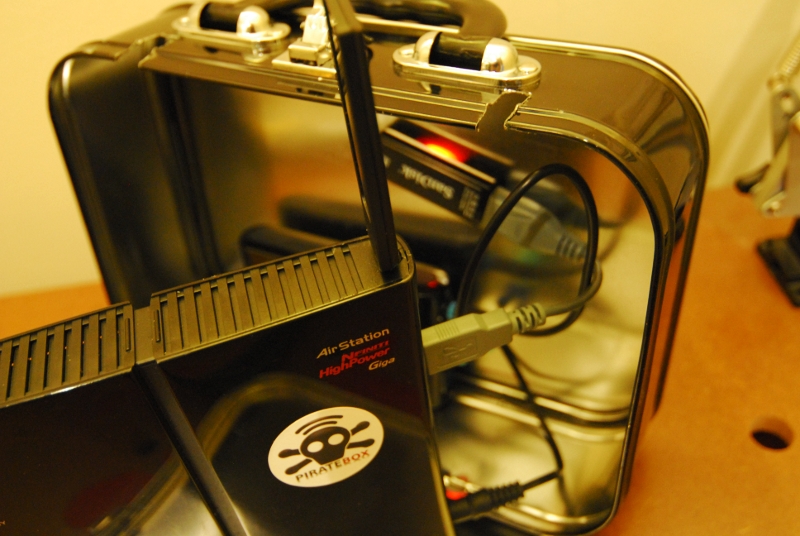
Piratebox V2, photo courtesy of David Arts.
The evolution of the Piratebox has not stopped there as further development focused on increasing portability, ease of installation, and additional functionality.
David Darts now has a page describing how to build a Piratebox using a very inexpensive TP-LINK MR3020.

Small router / access point / Wi-Fi access point. I added the crossbones to retain the pirate theme.
This device is originally designed to allow redistributing internet access wirelessly achieved either from an ICS connection on a laptop, or even directly from a cell phone.
As portability is the main selling point of this device, they made it small. It’s supported by OPENWRT and modifying it to become a Piratebox was relatively painless. It did not require any fancy jailbreaking. I simply uploaded the new firmware via the default web interface. I also added a small USB key for storage.
There is a helpful forum where you can get further assistance in your efforts, located at: http://forum.daviddarts.com/
(This is very useful if you brick both of your Pirateboxes like I did.)
Once you have completed the conversion from the standard firmware to the custom one, you can connect to it by selecting the “PirateBox – Share Freely” unsecured wireless network. All traffic will be redirected to the locally hosted web page where you can upload and download files.
To test the functionality I uploaded several files, and used the built-in anonymous chat feature, called shoutbox.
After some further tinkering, I was also able to deploy a Pirate box on a TPLINK 3040. This removes the need to carry around a separate battery, for the ultimate in anonymous portable file sharing!

Darts said this project was in part inspired by USB dead drops, pirate radio, and the free culture movement. The community around it is vibrant. It has been ported to Android, can be run entirely on a laptop and the list of devices you can get it to run on is constantly growing.
Sadly, despite several long visits at my local coffee shops, I have yet to have a single file shared.
Perhaps people are starting to heed our repeated warnings about randomly connecting to unsecured Wi-Fi access points?










