What are file extensions?
A file extension (or simply “extension”) is the suffix at the end of a filename that indicates what type of file it is.
This suffix is separated by a point from the name of the file, for example word.doc). But, by design, points are also allowed as part of the filename. You may have seen filenames like program-1.12.3-ver4.exe which are clear for all to determine what it is. The extension is exe so the file is executable.
But malware writers are using this behavior to trick users. And users that have “Hide file extensions for known filetypes” checked, could easily fall for this. Unfortunately, this option is checked by default.
How are they being tricked?
Consider the file Gangster.exe which could be anything, but let’s assume it’s malware. The person trying to get you to run that file does not stand much of a chance if he mails it to you named like that, does he?
But let’s make a few changes which will not affect the behavior of the file in any way.
First we rename the file to YourTickets. exe The filename is irrelevant for what the file actually does, so it does not change anything. Hey, but then we can go one step further and rename the file to YourTickets.pdf.exe
Remember what we explained before? “YourTickets.pdf” is now the filename without extension, but the extension is still exe so it is still an executable and it still does have the same effect. Only problem is, and that is the objective of the entire trick, that to some people it will now look like this:
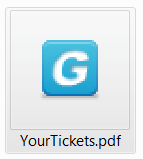
But it doesn’t look like a pdf, you say. Well, a programmer can define any icon to be used for his application, so why not use an icon that everyone knows and trusts.
Et voila!

Is this actively being used?
You bet. This is how malware like for example Cryptolocker is mailed to millions of potential victims. Usually pretending to be from a worldwide courier service, but it could also be a travelling agency. Is it surprising that many fall for it?
What can I do?
Surprising or not, there are a few things you can do, to avoid becoming one of the victims.
First of all, your spam-filter should catch all executable files and delete them or at least warn you about them. Secondly, never open attachments that you did not expect. Thirdly, change your settings so you can see the true extensions of files.
And last but not least, use resident protection, be it Malwarebytes Anti-Malware, an antivirus or both. Even if you trigger the file by accident, resident protection will stop the file from running, if it has the file signature in its database.
How do I change my settings so I can see the true extension?
Easy. In Windows open any explorer window and locate the “Folder and search options”
- Windows 8 : “Options” > “Change folder and search options”
- Windows 7: “Organize” > “Folder and search options”
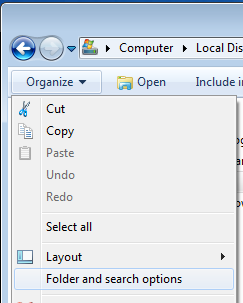
- Vista and XP: “Tools” > “Folder options”
Under all of the above you will find a “View” tab. Under the options listed there, remove the checkmark before “Hide extensions for known file types”

From then on you should be able to see the true extensions.
Summary
Malware is using a method with double extensions to trick users into thinking files are safe to be opened. Don’t fall for it. Read how to see those files for what they really are.
And as always “Save yourself the hassle, get protection.”