Security journalist Brian Krebs revealed details yesterday surrounding the malware sample used in the Target cyber-attacks, which originally took place November 27 – December 15, 2013.
On Sunday, Target CEO and President Gregg Steinhafel conducted an interview with CNBC over the recent Target security breach. During that interview, he mentioned that a malware infection was involved, but no specific samples were identified.

According to Krebs, a report of the malware used during the breach was uploaded to ThreatExpert, an automated analysis system run by Symantec.
The report has since been removed, but Krebs managed to save a copy of the cached report (found here on his website). Afterward, a “source close to the investigation” tied that report to a malware family Symantec identifies as Infostealer.Reedum.
Reedum is a POS ram scraper malware, a type that scans memory within processes and “scrapes” out anything useful. For POS malware, this is usually Track 2 credit card information that can be used to create a forged copy using special equipment.
I managed to acquire a copy of the Reedum malware, with the first sample uploaded to Virustotal in July of 2012.
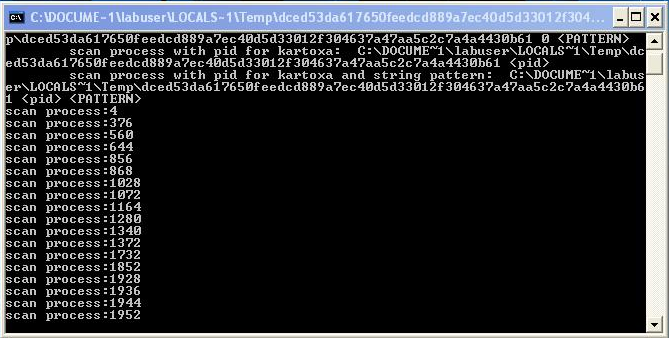
When executed, it’s pretty straightforward about what it’s doing; below is a dialog box showing the process scan:
Back in March of 2012, French security Researcher Xylitol analyzed an older version of Reedum from an infected POS system. The sample doesn’t appear to be as robust, but still contains the same functionality. You can see it on his blog here.
Target hasn’t spoken out about how the breach happened, but it’s believed that a web server was compromised and then a control server was established.
Krebs is currently investigating the author of the malware, called “BlackPOS” in underground criminal forums. For more information, see his full blog here.
_________________________________________________________________
Joshua Cannell is a Malware Intelligence Analyst at Malwarebytes where he performs research and in-depth analysis on current malware threats. Follow him on Twitter @joshcannell










