Malicious advertising attacks (malvertising) have been plaguing mainstream sites and their visitors a lot these past few years.
While some are easy to spot and get rid of, others tend to be much more sophisticated and hard to shine light on.
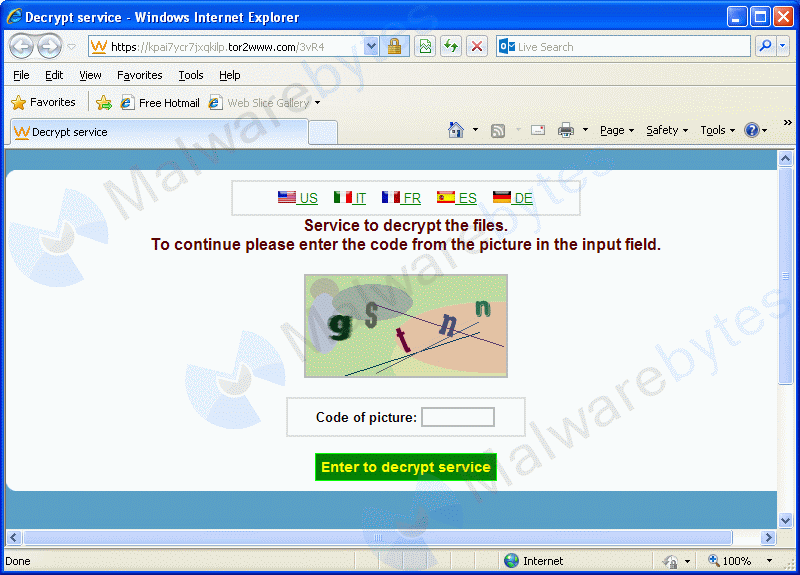
On Saturday 11th, we discovered a malicious advert that was displayed on huffingtonpost.com as well as other popular sites, such a Zillow.com. This advert was used to deliver the Cryptowall ransomware via a Flash exploit.
The ad was loaded by a third-party advertiser (servedbyadbutler.com) initially called by delivery.first-impression, where it won the real-time bidding auction for $2.31 CPM (cost per thousand impressions).
http://delivery.first-impression.com/delivery?action=serve&ssp_id={sanitized}&ssp_wsid={sanitized}&dssp_id={sanitized}&domain_id={sanitized}&ad_id={sanitized}&margin=0.55&cid={sanitized}&bn=inferno&ip_addr={sanitized}&ua={sanitized}&top_level_id={sanitized}&second_level_id={sanitized}6&page=huffingtonpost.com&retargeted=null&vender_data_used=0&height=250&width=300&idfa=null&android_id=null&android_ad_id=null&bid_price=2.699&count_notify=1&win_price=2.31
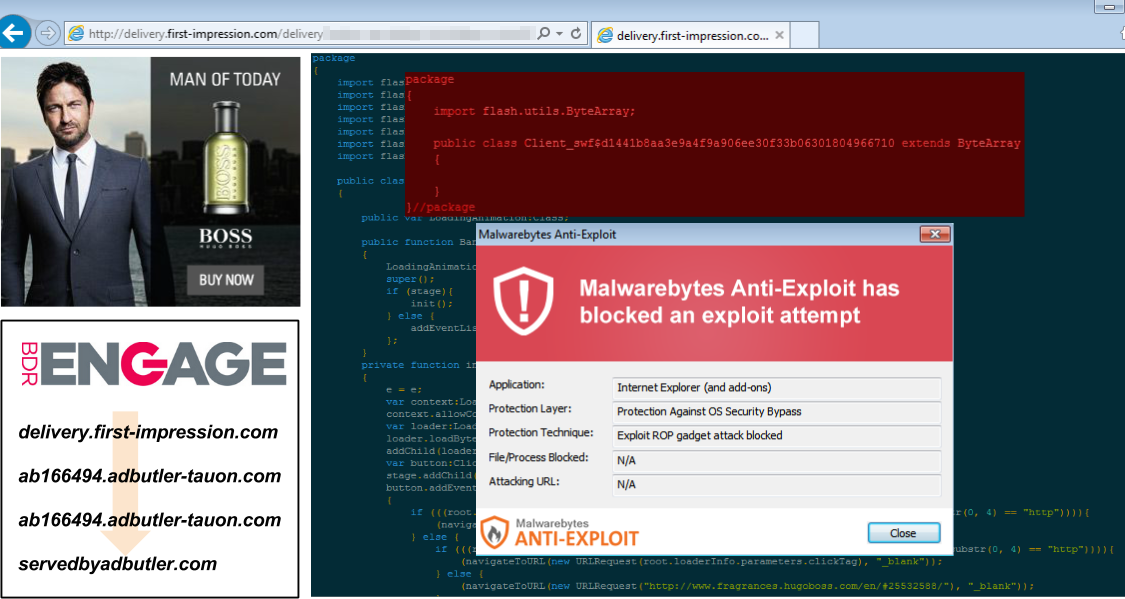
The majority of malicious Flash adverts we are used to seeing redirect to external pages, often leading to an exploit kit.
This one is different in that the advert itself (which could be for any brand) is also used as the exploit. This is the work of the Flash EK, which likes the ‘two birds, one stone’ approach.
Gaining the trust of an ad agency and packaging the exploit in the advert itself is a bit bold and risky. But it succeeded nonetheless and the bad guys behind it were able to push the Cryptowall ransomware onto visitors that were running outdated Flash Player versions.
Malwarebytes Anti-Exploit users were already protected against this campaign, while Malwarebytes Anti-Malware detected the Cryptowall sample. Removal instructions can be found in our forums here.
Engage:BDR has confirmed to us that the offending advertiser account has been deactivated and that this campaign is no longer active.










