We’ve recently encountered a number of URLs that, at first may appear to host a number of unrelated software, but if we visit and put them side-by-side, the pattern is obvious.
From the cookie-cutter design of the websites to the files they claim to serve, everything is similar, including their detection names.
Sites that usually use the same template are not inherently bad. Small businesses can utilize them as they are generally free, manageable, and easy to configure. One can create a business page and launch it the same day. Unfortunately, the ease and immediacy of such sites are widely exploited by spammers and mainly those with ill intent.
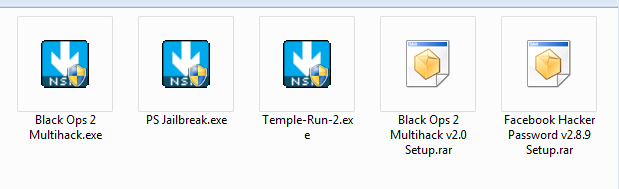
The above sites claim to be sources of the following:
- Call of Duty Black Ops 2 multihack setup tool
- a Facebook password hacking tool
- PlayStation 3 jailbreaking tool
- Temple Run 2 game
Screenshot of downloaded files below:
Once the files are extracted (when in a compressed file) and executed, they all display a GUI, advising users to click the Accept button to proceed with the installation. Promised programs aren’t installed, of course.
Some of these samples we retrieved also install other software, which in this case is a popular music player. Some were also capable of retrieving browser history data. All of them automatically run whenever the system starts up.
Once installation is completed, the user’s default browser opens a new tab to show a “Thank You” page and suggests another file he/she may want to try out. Below are these events in pictures:
Users of Malwarebytes Anti-Malware (MBAM) are protected from the URLs of these sites and the files they serve. We detect all files as PUP.Optional.Outbrowse.
Other related post(s):
- Scams, PUPs Target Would-be WhatsApp Voice Users
- “Cracked” Minecraft? PUP Installer
- Windows 10 Activation Programs: PUPs and Surveys
- PUPs and Java Removal Tools, Oh My
- Encountering the Wild PUP
Jovi Umawing










