This blog post explains what FEATURE_BROWSER_EMULATION is and why browser hijackers seem to love it. It also points out that this does not mean it’s automatically a problem if you have one or more of them.
What is FEATURE_BROWSER_EMULATION?
FEATURE_BROWSER_EMULATION is a registry key that allows you to set a different default document mode for the web-browser control of any given application.
The activation of this setting is done by adding a registry value—a name-data pair—to any of these keys:
HKEY_LOCAL_MACHINESOFTWAREMicrosoftInternet Explorer MainFeatureControlFEATURE_BROWSER_EMULATION HKEY_CURRENT_USERSOFTWAREMicrosoftInternet Explorer MainFeatureControlFEATURE_BROWSER_EMULATION HKEY_LOCAL_MACHINESOFTWAREWow6432NodeMicrosoftInternet Explorer MAINFeatureControlFEATURE_BROWSER_EMULATION
The value-name, in this case, corresponds to the application that has the WebBrowser Control. The value-data tells it what Internet Explorer version standard to follow when displaying Web pages, following the !DOCTYPE directive.
For example, the added registry value below—
HKEY_CURRENT_USERSOFTWAREMicrosoftInternet Explorer MainFeatureControlFEATURE_BROWSER_EMULATION "HomeBrew.exe" = dword:0x00002AF8
—makes sure that the WebBrowser Control of HomeBrew.exe displays Web pages containing standards-based !DOCTYPE directives the same way that Internet Explorer 11 would. You can find the description belonging to this specific value-data at this MSDN page.
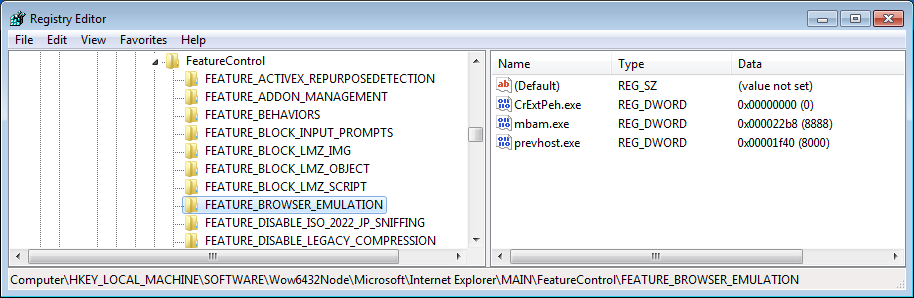
As you may be able to tell from the screenshot above, there are many types of applications using this feature:
- prevhost.exe is Windows’ preview handler
- mbam.exe is our own Malwarebytes Anti-Malware
- CrExtPeh.exe is used by many Mindspark/Ask toolbars
Roughly explained, it gives the application some control over how you see certain Web-based content in the programs’ windows of said application. This is usually done for compatibility reasons. As with many other registry keys and values, there is no need to specify the full path, only the name of the executable. So, as soon as that executable is removed from your system, the value is obsolete as it will not be used anymore.
Malwarebytes Anti-Malware does scan this key for known unwanted entries and removes them if they are there.
Summary
FEATURE_BROWSER_EMULATION is a setting that controls which Internet Explorer version certain browser controls should mimic. Although popular with browser hijackers and other adware, it is not a risk by itself.
Resources:
Pieter Arntz











