Author’s Note: We at Malwarebytes continue to do our part in educating our product users and constant blog readers about day-to-day online threats and how they can avoid falling prey to them. “PUP Friday”, our latest attempt at getting users acquainted with files they may need to watch out for in the Wild Web, offers an in-depth look at some interesting and quite notable potentially unwanted programs (PUPs). Expect to see this type of content pushed out twice a month at the end of a work week.
If you look at our policy for detecting software as a Potentially Unwanted Program (PUP) you will notice that there is an entry that says “Browser add-ons that install across multiple browsers”. And I’m going to assume that among our readers it’s common knowledge that vendors want security researchers to gain as little as possible information about their installs. If that can be combined with avoiding to get classified as a PUP by behaving “nice” they will do just that when they detect they might be installing on a security researchers machine.
Yontoo aka BrowseFox aka Sambreel
The PUP I want to display as an example for this is from the Yontoo family. These are sometimes detected as Sambreel or Browsefox, but in fact they all come from the same source. The normal procedure for their install is in a bundler. In fact the Yontoo installer is downloaded and executed by the bundle-installer, but they will use a trick that I will discuss later on.
VM-aware
The installer runs a few tests to figure out whether it’s being installed on a Virtual Machine (VM). For example it checks the drive model and the BIOS manufacturer. These are hard to change identifiers which give away a VM. It also checks for the presence of Fiddler and certain types of VPN services. It considers the presence of any such sign as a trigger to behave itself.
Behaving nice
What does behaving nice mean here? We will have a look at the installer for Splendor Search and use it as an example. The installer will prompt you if you agree to a change in Default Search engine. If you agree the default search engine in Internet Explorer will change to Yahoo Search!
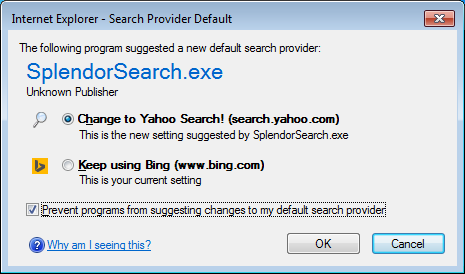
Screenshot 1
Regardless of your choice, your Start-page for Internet Explorer will be changed to Yahoo Search! Next the Yontoo installer will show a prompt that has links to the EULA and Privacy Policy and give the user the option to read them first.
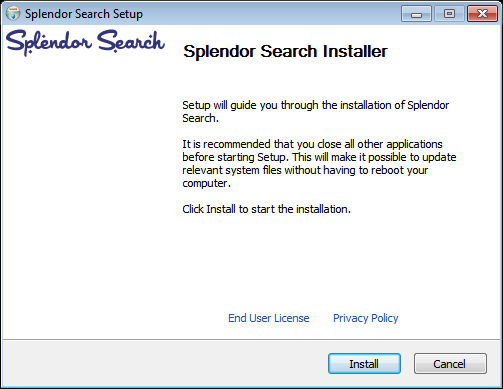
Screenshot 2
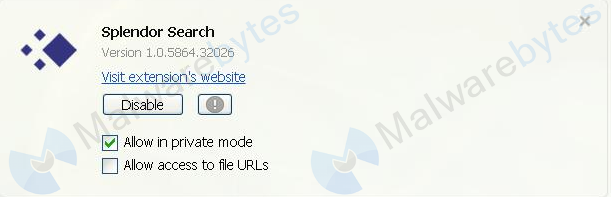
Should the user choose to proceed with the install then it will install one browser extension. When available that is always in Firefox.
Screenshot 3
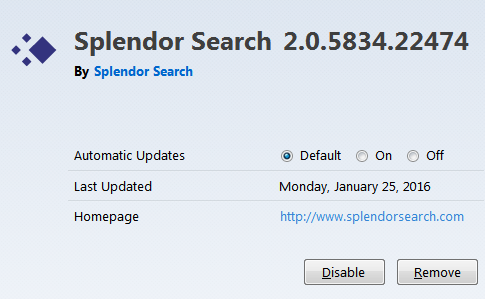
Other than that the installer will drop a copy of the main executable in the Startup folder and it will create a search icon on the users’ desktop. And an uninstall entry in your list of Programs and Features will be created. This uninstall works reasonably well for the “limited install” we have discussed here.
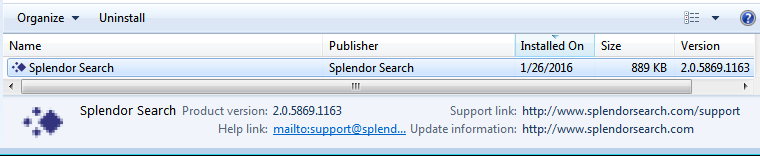
Screenshot 4
Trick
So how does the installer know when to deliver a full install? The bundle installer passes along some argument(s) when they trigger the Yontoo installer. These can be as simple as “/s” or “-brakes” or consist of several switches like for example “/sh 1 /is secret code”. Needless to say these arguments will be hard to guess, so it will take some degree of reverse engineering to find out what they are. Only after receiving the command with arguments and after checking if it is not on a researchers’ machine will the full install deploy.
The difference with nice
The difference in this case is not that big, but it demonstrates my point. First of all the install screen as shown in Screenshot 2 above will be skipped. And no other pointers to the EULA or Privacy Policy are offered. And the full install also looks for the presence of the browsers Chrome and Opera. If these are present on the system it will provide these browsers with browser extensions as well.
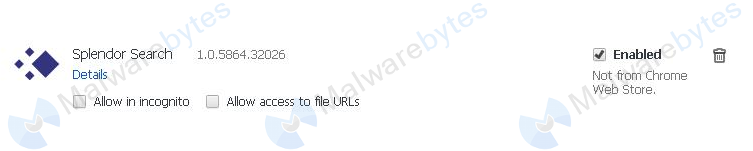
Oh, hang on. Let’s see. That qualifies as “Browser add-ons that install across multiple browsers” doesn’t it? Busted.
What the browser add-ons do
By now you may be wondering what these browser extensions do. In short: they alter the search results by adding sponsored links at the top of the listed results. Even if you use another search engine than Yahoo Search! as demonstrated below.

Altered Google search results in Opera caused by the browser extension
Detection, protection and removal
Splendor Search is detected as PUP.Optional.Yontoo and users of Malwarebytes Anti-Malware Premium are protected against this threat if they use the setting to treat PUP detections as malware. The removal guide can be found on our forums.

Summary
We have looked at the methods that the installers for Yontoo browser hijackers use to keep as much information about their program as possible away from security researchers. And maybe avoid being classified as potentially unwanted. They consist of using command switches in bundled installers and routines to check if their installer is triggered on a security researchers’ machine.
Links
Pieter Arntz