In the beginning of the year, we asked our readers for their input about our PUP Friday initiative. For those of you that took the time to fill out the survey or post their comments, thank you for your feedback and continuous support!
The numbers
We had hundreds of readers that filled out our survey. Which is pretty great. Thanks for that.
Over 95% of them answered yes to both these questions:
- Would you like to learn more about the technical details of a PUP file and the system changes that happen once it’s installed on a system?
- In relation to blog post content: Would you be interested in knowing how the PUP infection (false promises, bundled, scam etc.) takes place on a system.
So we will include this information, or point you to where it can be found, whenever this is available.
Other questions about the blog posts
Question number 3. Was an open question and we asked our readers: “What other information do you think should be included in PUP Friday posts?” We will try and answer the resulting requests and questions here.
Videos
One of the most common requests, which was also posted in the comments, is the request for videos. After some deliberation, we have decided that this is feasible, but in a lot of cases it is not very useful. What most PUPs do can be captured in a few screenshots, but if it does something extraordinary or requires a special method to be removed we promise we will make videos.
Technical details
Some requests were aimed at the amount of detail that we provide. Some wanted more technical details and others requested the posts to be made easier for the less technical readers. For those of you that are unaware: We do include a link to our removal guides at the forums for almost every PUP we post about. In the removal guides, you will find a section called “Technical details for experts”. Here you can find which folders and files were added and which registry keys were changed or added.
Removal instructions
The people that asked for removal instructions should take a look at our forums as well. The removal guides all have sections “How do I remove this pest?” and “Is there anything else I need to do to get rid of this pest?” which should answer all your questions in this area.
Prevention and method of infection
There were also some readers interested in reading how to prevent these PUPs or wanting to learn how these PUPs got installed. Those two are obviously very much related and we know we provide these details whenever they are available to us. However, if we are not clear enough, do let us know. We are working on something that should satisfy a lot of these and similar desires, and we will be able to link you to it when applicable. Stay tuned for that.
Hashes
People asked us to include hashes for the files we discuss. Whenever possible, we link to the Virus Total reports. You can find all the hashes you like in these reports. We’ll do our best to not only include the report for the installer but for other relevant files as well.
Prevalence of the PUP
Other people were interested in knowing how prevalent certain PUPs are. Although we do have certain parameters that can tell us something about how often they are found “in the wild”, it is very challenging to give exact numbers. For example: many of the families that have very similar variants that frequently change are detected by family name rather than as individual variants. We do try to write about the ones that stand out and those that get posted on our forums about a lot. Sometimes, it’s just a matter of finding an installer for them so we can do some testing and gather the logs.
Wireshark data
We have also received requests to include Wireshark logs. Wireshark is a network protocol analyzer we could use to record the internet traffic generated by the PUP in question. We’ll look into this.
Which OS
Another item of interest is knowing which operating system the PUP would run on or affect. As a rule of thumb, everything we discuss in our PUP Friday posts runs on Windows 7 – 10. If they do not, we make it a point let our readers know explicitly. Also, we mention if certain PUPs are VM-aware.
Related PUPs and sites
Can we include links or names of related PUPs, the websites they hail from, the families they belong to, and other related information? Yes, we can, and we’ll begin including these in future posts.
Other questions about PUPs
Q: Some security products have different criteria to determine what a PUP is than Malwarebytes. Can you explain why the industry sees this issue differently?
A: We can’t speak for other vendors, but our guidelines are posted on our website. What we can and will try to do as much as possible is explain why we find a certain PUP “potentially unwanted.”
Q: Can you include the monetary costs per user/enterprise?
A: Not in dollars per install, but we will include secondary risks (does the PUP lower security settings) and how hard it is to remove the PUP and undo the changes it made to the compromised system.
Q: Can you include how to best prevent PUPs from getting installed, especially in an enterprise environment?
A: We have some general guidelines on our site on how to prevent PUPs, but nothing aimed at enterprise environments. The main points of attention would be:
- Endpoint user education, make sure everyone is aware of the company guidelines.
- Software restrictions, not always easy, especially in a Bring-Your Own-Device (BYOD) environment.
- Protection, make sure updates and security software are working and offer adequeste protection.
If there are any special methods to protect against a PUP, we will include these in our posts. If you are experiencing a lot of problems in your business environment, we advise you to get in touch with our Sales Department.
Q: How do programs install PUPs anyway even when you declined?
A: This user went on to give us an example which told me he was asking about a bundler. Victims that are careful enough to untick every additional offer in a bundler (or use software like Unchecky to do that for them) often find that despite all that, there are some undesired side-effects after the installation. What users should realize is that some bundlers cheat and don’t give them the option to decline all of the “extras”, so one PUP or another will slip through.
Q: What are the big name players of PUPs? How likely can one find them, like Mindspark and Conduit being the typical ones that flood a system with PUPs, while Ask is more quiet with how many pups it throws on?
A: Although this is not a bad question, it contains a few possible misunderstandings that I’d like to clear up first:
- Mindspark and Ask are from the same firm that is called IAC Applications.
- The number of detections is not the same as the number of PUPs. Installing one PUP can lead to hundreds of unwanted changes on an affected system that Malwarebytes Anti-Malware will detect and remove.
In answer to the question, the current “big three” are Yontoo, IAC Applications, and Conduit—mostly the latter two, because they make applications that users find useful after reading about them. Furthermore, they are promoted heavily. Yontoo comes up with new names for almost identical programs every few days, so it is hard to warn users about them. But we do have tabs on all three of these and keep our eyes and ears open to catch any new ones as fast as they come and sometimes even before they are released.
Q: Can Chromium-based browsers be affected by the same unwanted extensions as Google Chrome? And would they get the same PUP treatment?
A: This depends on how the Chromium-based browser was built, but for most of them, we would say yes. They inherit the properties from Chrome that would allow the extensions. And if they do not follow Chrome’s limitations, they are even more vulnerable. As an aside, we have seen Chromium-based browsers that were PUPs in their own right [1], [2].
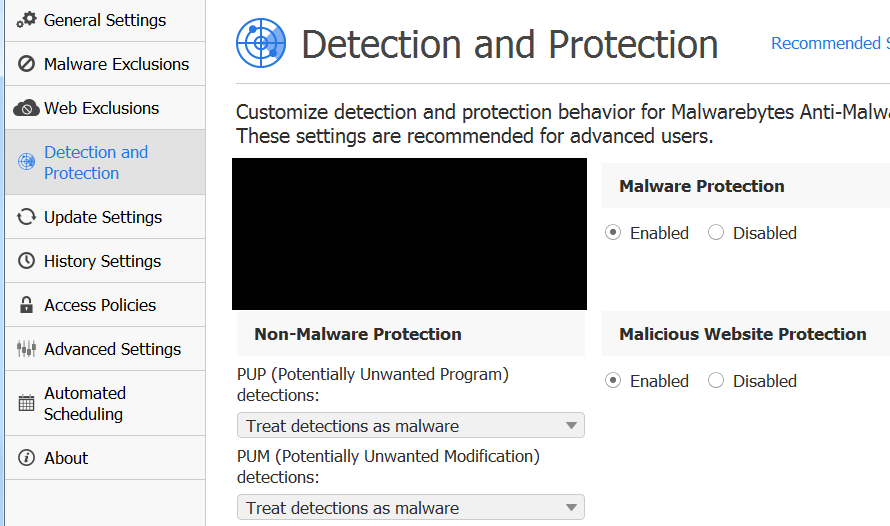
Q: Why can’t your real-time protection stop PUPs being installed on my PC? How did they get through?
A: Sometimes new ones will escape detection, but if it happens more than once, please make sure that your “Protection” settings are optimized. Both “Protection” modules should be set to “Enabled” and “PUP and PUM detections” should be set to “Treat detections as malware”. And, obviously, make sure that Malwarebytes Anti-Malware and the test of your software is fully updated.
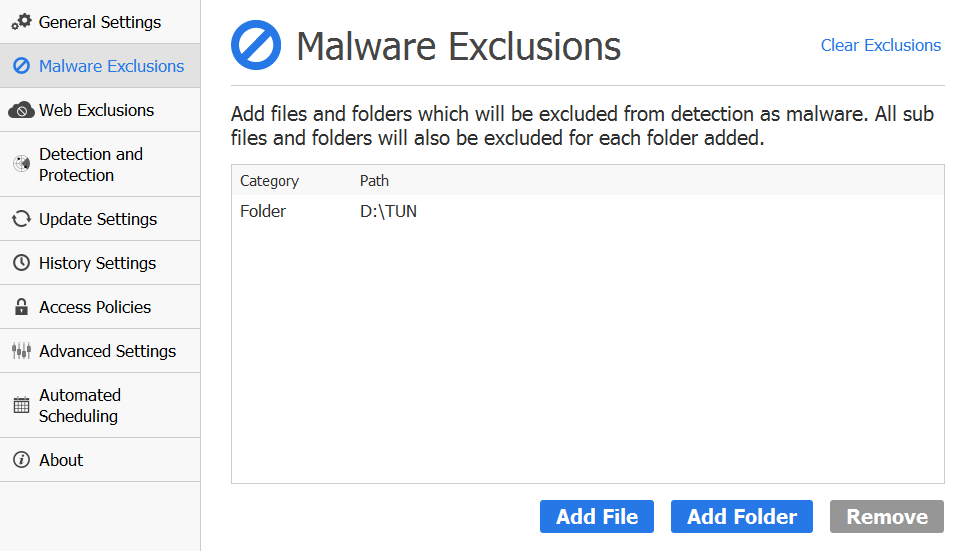
Q: What if I find a particular PUP useful, but I don’t want to disable protection or change the detection setting. What should I do?
A: You can exclude files and folder from being detected as shown below – for the folder where I store my malware samples – by clicking Settings > Malware Exclusions > Add Folder and navigate to the folder (or file) that you don’t want to be detected and removed. In the example below, we have excluded the folder that we use to store our malware samples.
Summary
Again, we’d like to thank you for your feedback and, as a result, we will make the following changes:
- Videos will be made whenever these add something to the content
- You can stay tuned for a change that will help – but not only – with prevention tips
- We will include more hashes of the relevant files.
- We will look into including Wireshark logs.
- We will include mentions of the PUPs family and point out some other members of said family.
- We will point out the secondary risks that PUPs bring with them. (privacy, security, and any others)
Pieter Arntz and Jovi Umawing










