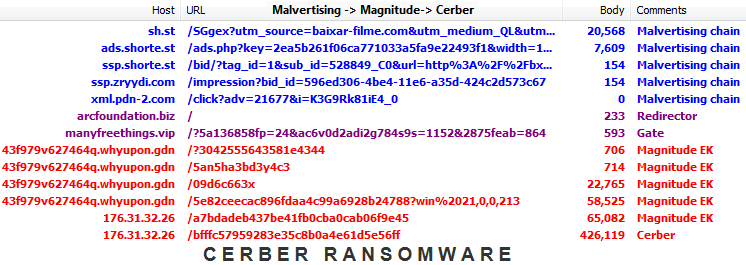
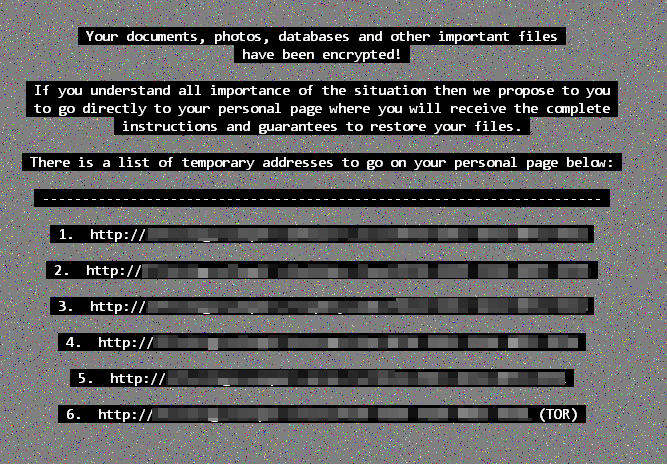
We have been tracking a malvertising campaign distributing the Cerber ransomware linked to the actor behind the Magnitude exploit kit for months.
It will pop on one ad network, then onto another and come back again ad infinitum (no pun intended).
Despite a global slowdown in exploit kit activity, this particular distribution channel has remained active and strong. In this post we take a look at some past and present indicators of compromise that show how fake identities remain an effective way to defeat ad platforms’ security checks (for those that have some anyway).
This activity dates back to last year with Magnitude pushing CryptoWall for a few months, before switching to Teslacrypt briefly and finally settling on Cerber.
One of this attackers’ favourite spot has been on torrent or streaming sites but also via monetized URL shorteners that use a pay per view/click model when people open up a shortened URL and have to wait for an advert to load before getting to their destination.
It is no surprise that more ads – and low quality ones especially – means chances of drive-by downloads are dramatically increased.
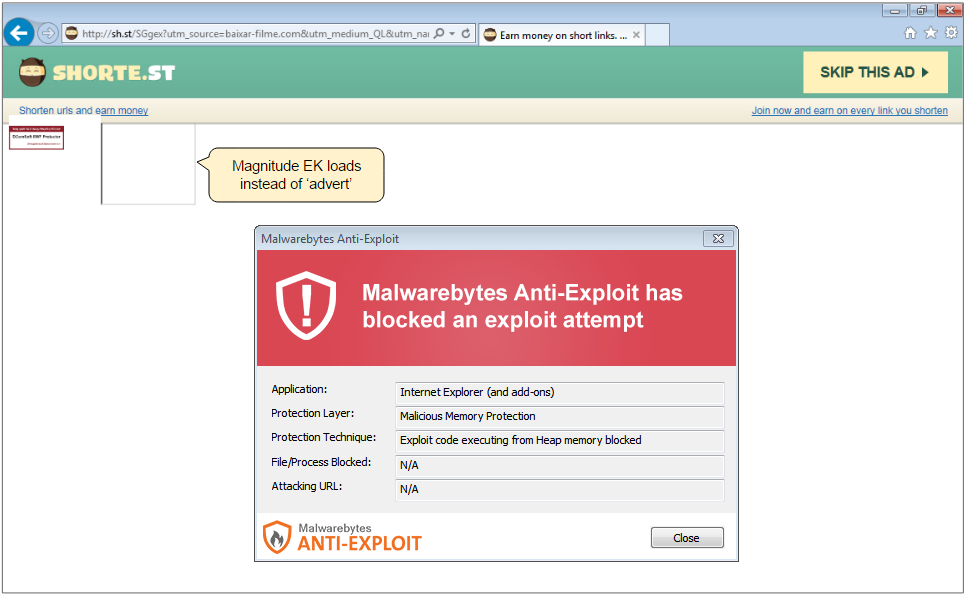
In this case the ad came from one of those infamous third party XML feeds, known for their high risk nature:
Although this malvertising campaign is mostly going after cheap traffic sources (unlike the larger scale attacks against top publishers), it has been running uninterrupted with threat actors playing a game of cat and mouse with ad networks and security researchers. Also, cheap traffic does not necessarily mean low volume, as we often spot larger portals spewing malvertising.
– Streaming site (7 million daily visits): putlocker.is
-> Ad network (malvert): onclickads.net/?auction_id={removed}
-> Ad network (malvert): eclkmpsa.com/adServe/banners?tid=PTLCKR&action=r
-> Redirector: arcfoundation.biz
-> Gate to EK: manyfreethings.vip/?{redacted}
-> Magnitude EK: e52a9wf78.penenough.gdn
For ad networks to stop this continuing onslaught for good would require no longer accepting risky customers and closing up their platform for arbitrage with unknown buyers. Playing whack-a-mole with crooks wearing many different hats is simply an ineffective solution where malicious ads always end up making it through.
IOCs:
Redirectors and gates, with registrant and registrar.cliffordbruce1966@gmail.com PDRLtd.d/b/aPublicDomainRegistry.com
gamez250.info,2016-04-25 electocigsshop.info,2016-04-24 casinobusiness.org,2016-04-21 roundgames.info,2016-04-20 myrealgames.org,2016-04-18 manygames.org,2016-04-18 manygames.org,2016-04-18 investmoneyforyou.org,2016-04-18 gamenode.org,2016-04-18 gamenode.org,2016-04-18 mybestplaycity.net,2016-04-18 mayaecigarette.net,2016-04-18 prosmokestore.info,2016-04-18 elcigonline.info,2016-04-18 cvapor.info,2016-04-18 roundgames.biz,2016-04-18 altsmoke.biz,2016-04-18 301investmoney.biz,2016-04-18 plagamesonlinehere.com,2016-04-17 mayaselcigarette.com,2016-04-17 clicksinvestmoney.com,2016-04-17
zipehohelan@instruction.com AlpnamesLimited
primeschoiceautoparts.biz,2016-06-29 moneysupermarkets.biz,2016-06-29 online-zonegames.org,2016-06-29 myvapourlites.org,2016-06-29 mytucows.org,2016-06-29 301investmoneyonline.org,2016-06-29 listgames.info,2016-06-29 freewarefiles.info,2016-06-29 freewarefiles.org,2016-06-28 mytucows.biz,2016-06-28 money-supermarket.org,2016-06-23 money-supermarket.org,2016-06-23 gamelistonline.org,2016-06-23 game250frees.org,2016-06-23
davewilliams@engineer.com AlpnamesLimited
top4download.org,2016-07-01 arcencielfoundation.org,2016-07-01 softswiss.info,2016-07-01 softswiss.biz,2016-07-01 arcencielfoundation.biz,2016-07-01 1001freefonts.biz,2016-07-01
batesgarner@linuxmail.org AlpnamesLimited
greatfreefonts.org,2016-07-11 arcfoundation.biz,2016-07-11 zonedgameson.org,2016-07-07 manyfreefonts.org,2016-07-07










