A new piece of malware for Mac OS X has been discovered, according to a blog post from Bitdefender.
This malware, which Bitdefender is calling Backdoor.MAC.Eleanor, is only the second piece of true Mac malware spotted so far in 2016, the first being the KeRanger ransomware. (Of course, this is not taking the widespread and increasing plague of Mac adware into account.)
The malware was available on MacUpdate, in the form of a free app called EasyDoc Converter. The app purports to convert a couple file formats into Microsoft Word files, but there’s no sign that it actually does this. Instead, it installs a backdoor when run.
The app is not signed with a certificate issued to an Apple developer ID. This is fortunate, in a way, as this makes it more difficult to open. (By default, Mac OS X will not open unsigned apps.) However, it’s also unfortunate, because a determined user will be able to open it anyway, and because there’s no certificate involved, Apple cannot kill the app by revoking the certificate.
When the app is opened, it runs a shell script whose first task is to check for the presence of Little Snitch.
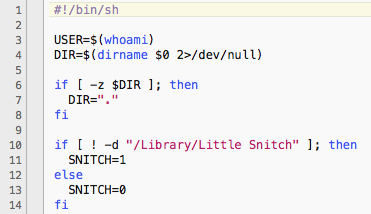
If LittleSnitch is not present, and if the malware has not already been installed, it then installs three LaunchAgents in the user folder plus a hidden folder full of executable files. All these items have names that attempt to make them seem like Dropbox components. The items created by the malware are:
/Users/username/Library/LaunchAgents/com.getdropbox.dropbox.integritycheck.plist /Users/username/Library/LaunchAgents/com.getdropbox.dropbox.timegrabber.plist /Users/username/Library/LaunchAgents/com.getdropbox.dropbox.usercontent.plist /Users/username/Library/.dropbox/
The “.dropbox” folder is a hidden folder, since its name begins with a period, and it contains all the executable files and data used by the malware. The three launch agents load different executables from this folder. Note that there is a legitimate folder named “.dropbox” that gets installed by Dropbox, except it is directly inside the user folder, not the user’s Library folder.
According to Bitdefender, this malware is capable of all manner of backdoor activities, such as access to the file system, remote code execution and webcam access. The three launch agents initiate a Tor hidden service, a web service and a Pastebin agent.
The Tor service sets up an address through which the attacker can establish communications with the web service component. The web service provides the means for the attacker to send commands to the infected machine. The Pastebin agent is used to upload the infected Mac’s Tor address to Pastebin, where the attackers can find it. According to Bitdefender’s report, the first upload to Pastebin by this malware occurred on April 19, about two and a half months ago.
In all, although this is a nasty bit of malware, the good news is that it’s awfully easy to remove. Further, the fact that it was disguised as a file converter meant to convert two relatively obscure file formats, coupled with the lack of any code signature, means that its distribution was probably fairly limited.
Interestingly, this app’s page on MacUpdate has ratings submitted by users between 2014 and March 26, 2016, all but one of which are 4.5 or 5 stars. Since this malware appears to have first “turned on” in April, I suspect that the real EasyDoc Converter may have been abandoned by its developer and somehow obtained by malware authors.
There are a few takeaways from this. First and foremost, if an application doesn’t have a code signature, and Mac OS X doesn’t want you to open it by default, you should pay attention to that. Certainly, not every unsigned app is malicious, and not every signed app is legit, but having that code signature is at least some measure of protection. At a minimum, if the app is found to be malicious, Apple can revoke the certificate used to sign the app, rendering it inoperable.
Second, be cautious about running old, abandoned apps. Again, not all apps that haven’t seen updates in a while are malicious, but it is becoming an increasingly popular thing (especially amongst Chrome extensions in the Chrome store) for unsavory developers to turn abandoned software into adware or malware. This gives the malicious software a hint of legitimacy, by infecting software that has a history. If an app has been abandoned, you probably should think twice about downloading it, and you should be cautious about even running an old copy on your hard drive if the app has a self-updating mechanism.
Finally, be cautious about where you download apps from. When I tried to download EasyDoc Converter from MacUpdate, the first thing I got was a MacUpdate installer that would have, on top of installing the malware, also installed a bunch of other adware. In general, avoid any kind of download aggregation sites, and download software directly from the developer.
If you have Malwarebytes Anti-Malware for Mac, it will detect this malware as OSX.Backdoor.Eleanor.










