During the past few weeks there has been an increase in malvertising attacks, for example via a series of compromises of open source Revive ad servers which is still continuing. What’s interesting to note is that some compromised sites have more value than others and this is especially true when those sites happen to be used to serve ad banners. The ultimate reach of the malicious code being tied to how much traffic a site will receive, ad servers are the ideal candidate since they are used by hundreds or thousands of other websites relying on advertising.
Today, we take a look at a somewhat similar case (although it did not appear to use the Revive framework) involving a hacked third party ad serving web server. We found several different adult websites that leverage it as an “ad renderer” to display side banners.
The conditionally injected script redirects to the Afraidgate campaign, which in turns pushes the Neutrino exploit kit. We are accustomed to seeing this gate operate directly from ‘typical’ (compromised) websites, but not so much from ad serving ones. This could very well be an ‘accidental’ malvertising case (a hacked site simply happened to be also used to serve ads) or perhaps, and time will tell, attackers are focusing on such infrastructure as they know it will yield a greater return.
In this particular example, users will visit an adult site and see an ad banner on the side. No click is required to start the infection chain that will follow and eventually drop ransomware since the malicious code is loaded instantly when the picture appears. As is the case with malvertising, the malicious version of the ad banner is only served once per IP address in order to make replays of the chain of events more difficult for analysts.
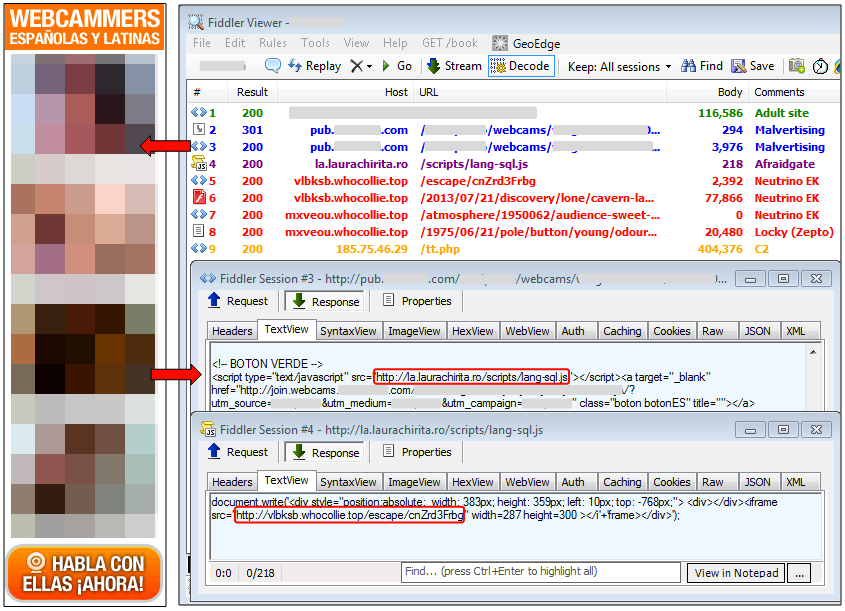
The Adfraidgate name comes from the use of the FreeDNS service at afraid.org which is the case here:
Domain Name: laurachirita.ro Registered On: 2015-03-02 Registrar: ICI - ROTLD Nameserver: ns1.afraid.org
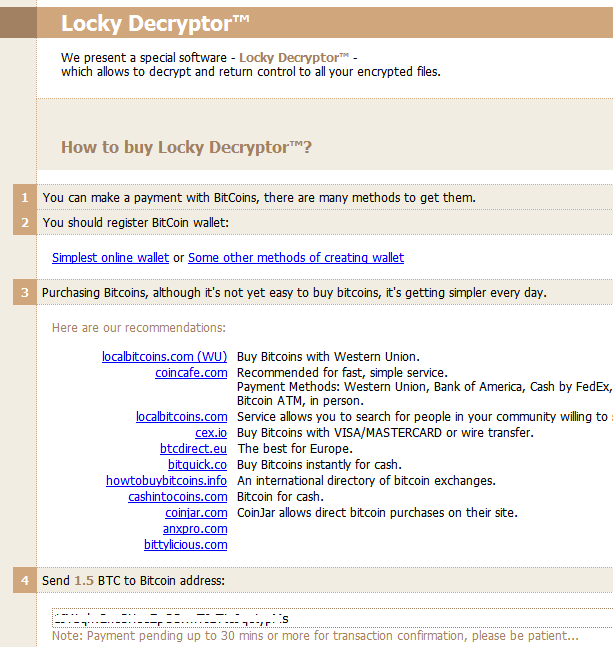
The payload from this Neutrino campaign is Locky (Zepto flavor) that asks for 1.5 BTC (approximately $939.53):
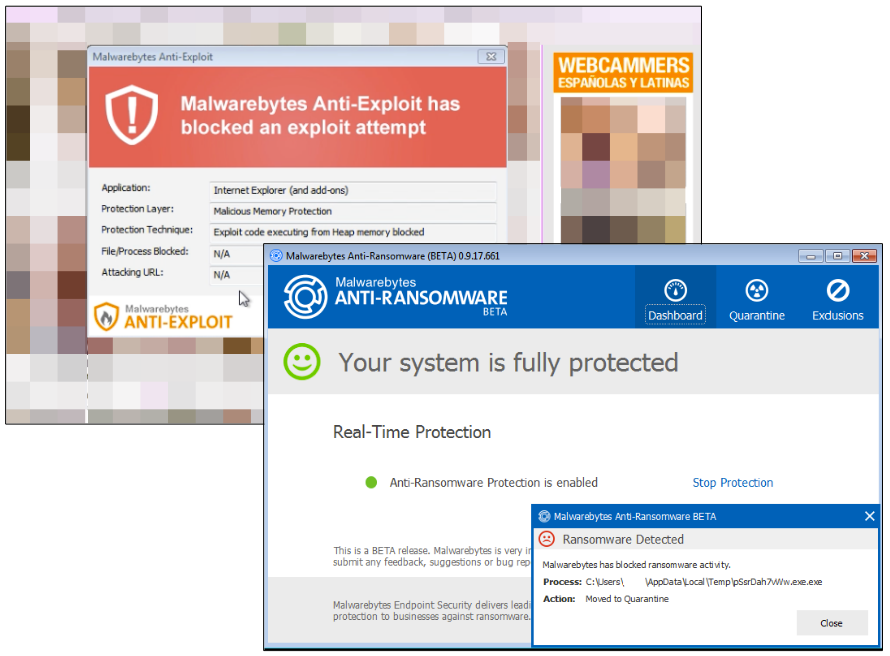
Both Malwarebytes Anti-Exploit and Anti-Ransomware (Beta) can block this attack at their own respective stages.
Indicators of compromise
- Afraidgate: la.laurachirita.ro/scripts/lang-sql.js
- Locky: 06b84f54a3a26931ae875d100918aab5e2631c33d0232871140712277bf7331b
- Locky C2: 185.75.46.29/tt.php










