Last Friday, I wrote about a set of 6 PUP apps by Nikoff Security. This week, there have been some new developments in the story, some good news and some bad news.
First the good news
Apple finally removed those apps from the Mac App Store. So there is no longer any danger of people visiting the App Store being scammed into purchasing these apps.
Now the bad news
Unfortunately, the bad news is, a couple similar apps reappeared on the App Store, this time made by a “Bartal Breuer”.
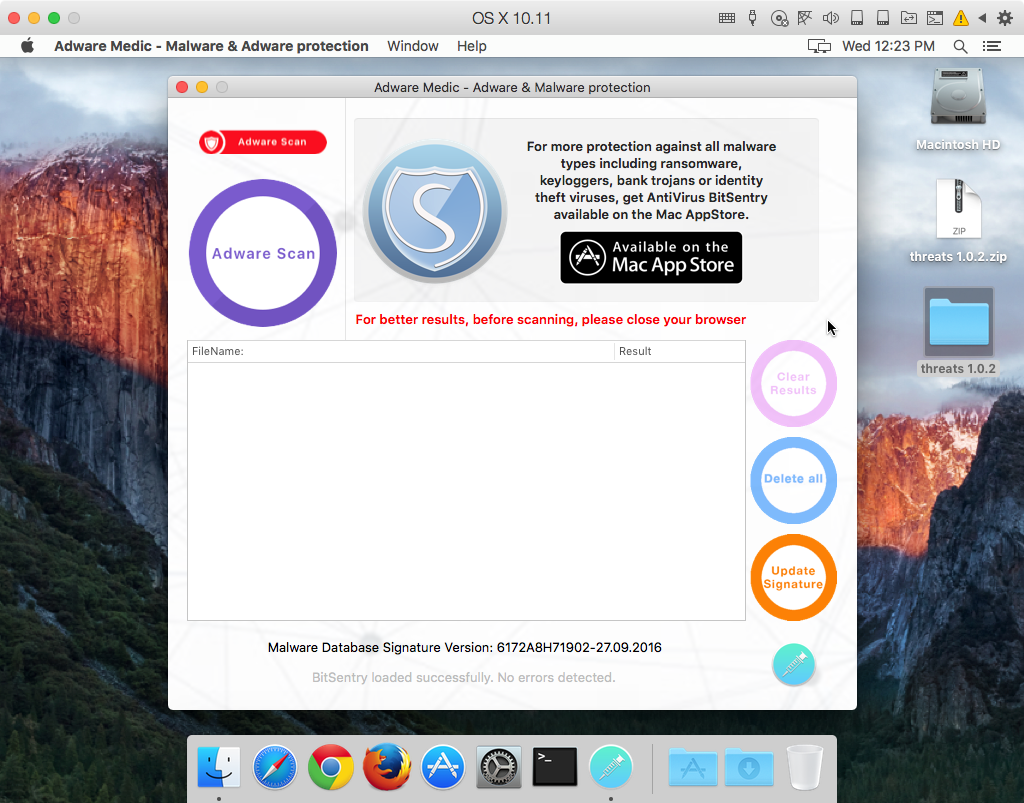
One of these apps was named Adware Medic – again, an attempt to cash in on the name recognition of my old AdwareMedic app (which is now Malwarebytes Anti-Malware for Mac). As with the previous apps, this one displays a prominent ad for it’s “big brother,” AntiVirus BitSentry.
AntiVirus BitSentry was, at that time, free in the App Store, but it was identified as being free “for a limited time only,” just as the previous AntiVirus Spartan Pro was for a short time.
Amusingly, it was identified as being the “#1 Best new AntiVirus software available for macOS,” a completely false claim meant to lure in unsuspecting users.
Interestingly, these apps seem to have completely different interfaces than the previous ones, made by “Nicholas Ebner.” However, there are distinctive similarities.
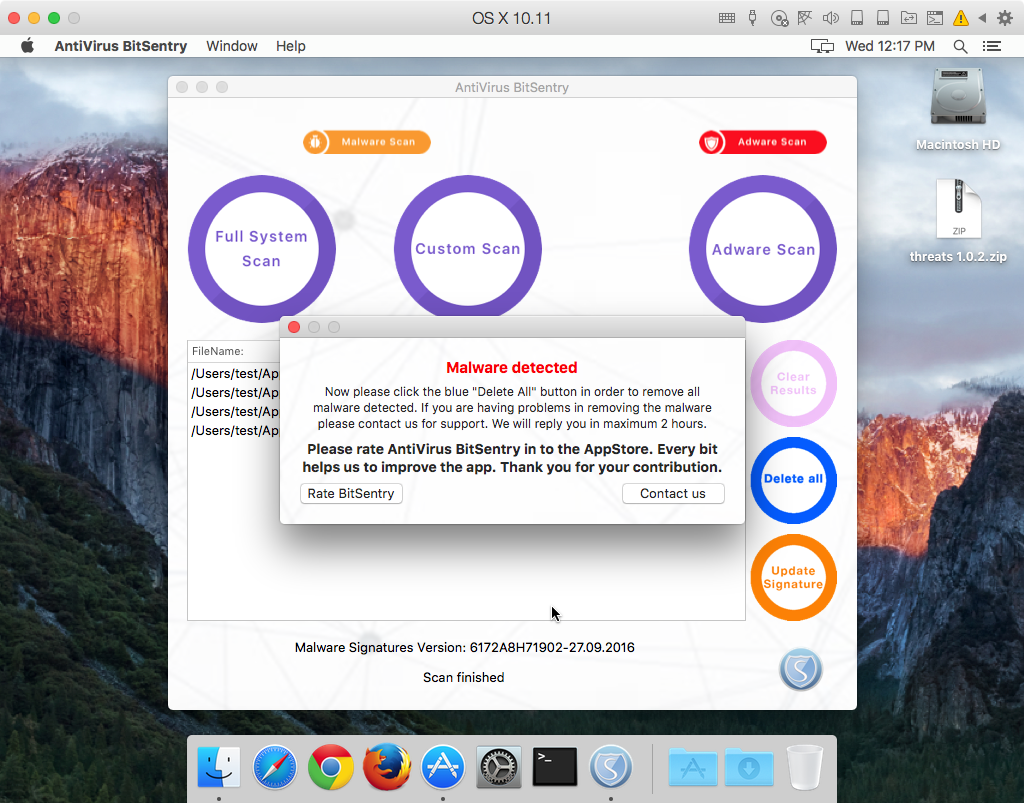
As with the last set of Nikoff Security apps, I installed 53 different threat files into the user folder, including malware, adware, and PUPs, then ran both a “Full System Scan” and an “Adware Scan” to see what was found.
In AntiVirus BitSentry, the “full system” scan (which actually was a bit of a misnomer, as it was only capable of scanning the user folder) found 4 things:
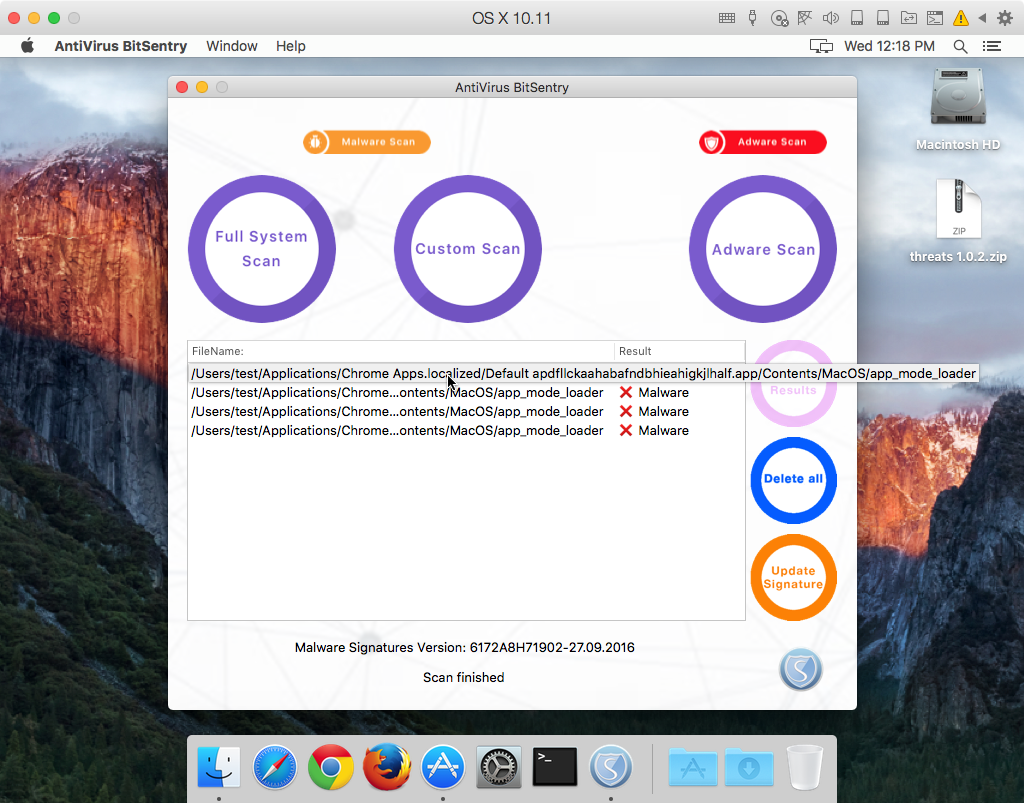
Oddly, none of these four “malware” files are things I added to the system. In fact, they are actually false positives, detecting components of items installed by Google Chrome. None of those files are malicious. Further, note the conspicuous absence of any actual malware that I had added to the system.
The adware scan, in both AntiVirus BitSentry and “Adware Medic,” behaved in exactly the same manner as scans in the old “Nicholas Ebner” apps. They detected a number of strange components inside a flashmall.app bundle, many of which were not at all malicious (such as image files), but they did not detect any of the other items I had installed.
Also similar to the “Nicholas Ebner” apps, both of these new apps will prompt the user to either rate the app or contact the company following each and every scan.
This time, the Contact Us button does not go to the Nikoff Security site. Instead, it goes to securityfocus[dot]eu, supposedly a company by the name Security Focus Europe. Ownership of this domain is again hidden behind an anonymizing service. Unlike last time, when I was able to trace the Nikoff Security domain back to Romania, this site’s location is more well-obscured.
There is more good news, however… as of yesterday morning, Apple has swiftly responded to my report and these two apps are history. They too have been removed from the App Store.
However, it’s evident that the scammer behind these apps is persistent. Less than a week elapsed between the removal of the old apps and the addition of the new ones. That almost seems too fast, given that there’s a review process for new apps that takes time. I won’t be the least bit surprised to see more scam apps appear under other names, using other fake names as the developer.
Conclusion
Everyone using the Mac App Store should keep their eyes peeled for scams like this. If you see something, say something. We welcome any reports of these kinds of apps on our forums. You can also alert me personally to any such apps on Twitter. Unfortunately, it can be difficult for the average user to file a report with Apple without actually downloading the scam apps, which is not something I recommend doing.
Malwarebytes Anti-Malware for Mac will detect these new apps as PUP.NikoffSecurity, just like the older ones.










