The detection name of PUP.Optional.Downloader is probably as non-specific as you can get when it comes to identifying what particular unwanted program that is. Generally, Malwarebytes uses this name to detect Crossrider uninstallers, installers from the CHIP Online download portal, and other bundlers offered as downloaders.
For this blog post, we’re going to look at a bundled program called Internet Download Manager (IDM) for Windows, which we retrieved from a third-party website, as an example of how Malwarebytes uses the PUP.Optional.Downloader detection name. This sample falls under the “other bundlers offered as downloaders” category. For clarification, the IDM program discussed was not obtained directly from https://www.internetdownloadmanager.com/.
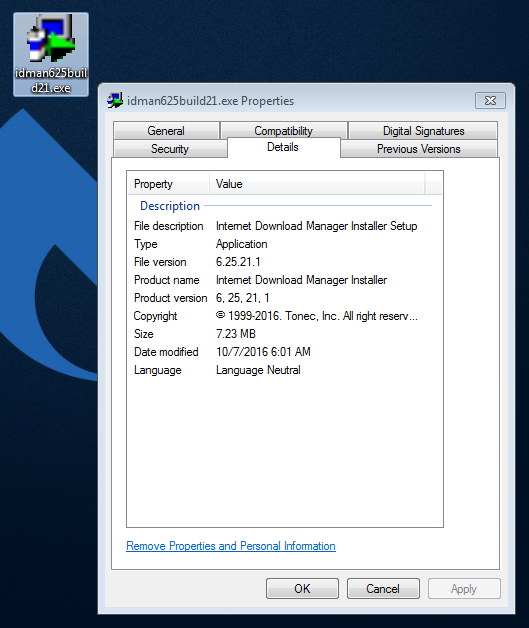
During installation, it displays the following user interfaces—
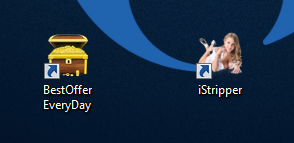
—and creates the following URL shortcut files for BestOffer Everyday and iStripper, as per the latest sample we have retrieved and tested.
IDM also integrates itself into Chrome and Firefox as browser extensions:
After installation, the bundler promising to install IDM then visits two consecutive websites via the Opera browser, the first one triggering Malwarebytes to block a URL it has deemed malicious—

—and the second one prompting us to “update our Adobe Flash Player”:
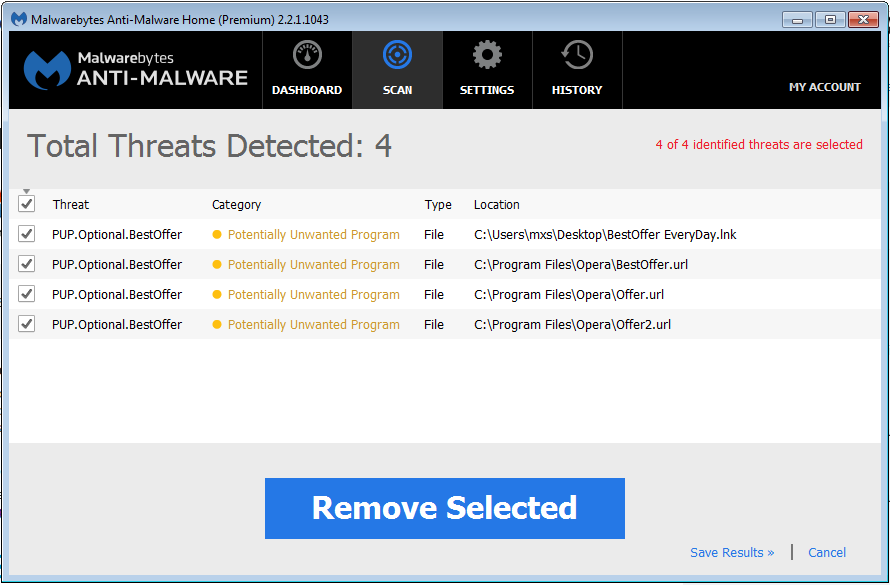
Malwarebytes detects the IDM installer as PUP.Optional.Downloader. We also detect all dropped shortcut files as PUP.Optional.BestOffer.
To read more on the technical details of the sample we just discussed, you can visit our removal instruction page on the forum here.
Jovi Umawing (Thanks to Pieter for additional info)










