A new malicious clicker has emerged onto third-party app stores. Chinese in origin, the malicious app uses heavy obfuscation and poses as a battery optimizer app. We classify is as Android/Trojan.Clicker.hyj.
Hide what’s inside
To obfuscate its code, Clicker.hyj uses an APK inside another APK that hooks into the malicious code — allow me to explain. Let’s call the original APK that gets installed from a third-party app store onto the Android device the shell APK. After installation, the shell APK hooks into another APK, which is held in the shell APK’s data folder — let’s call this the executing APK. The executing APK holds all the malicious code while the shell APK contains simple code that runs some libraries which does the hooking of the executing APK. Looking at the shell APK code, there isn’t much to it. Because of its simplicity, it could easily be overlooked by malware researchers and/or scanners.
It’s important to note that the executing APK cannot be installed on an Android device alone — it must be run via the shell APK.
The meaty badness
The executing APK holds all the meaty badness. Within the executing APK’s assets folder are several JavaScript files. These JavaScript files have base64 encryption along with other encryption to further obfuscate. The JavaScript files are used to perform various actions when URLs are piped to them via code within the executing APK.
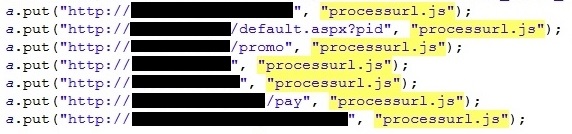
Although the code within the JavaScript files uses obfuscation, the file names are pretty telling of their actions:
- findbutton20161226.js – Find button on webpage
- getcaptcha4numberl.js -Get Captcha on webpage
- processurl.js – Process URL
- setcaptcha4numberl.js – Set Captcha on webpage
- simulationClickYes.js – Click “Yes” on button in webpage
With each URL “clicked”, the malware authors are paid a small amount as a result. Therefore, running the actions from the JavaScript files over and over again on a small list of URLs can accumulate revenue quickly.
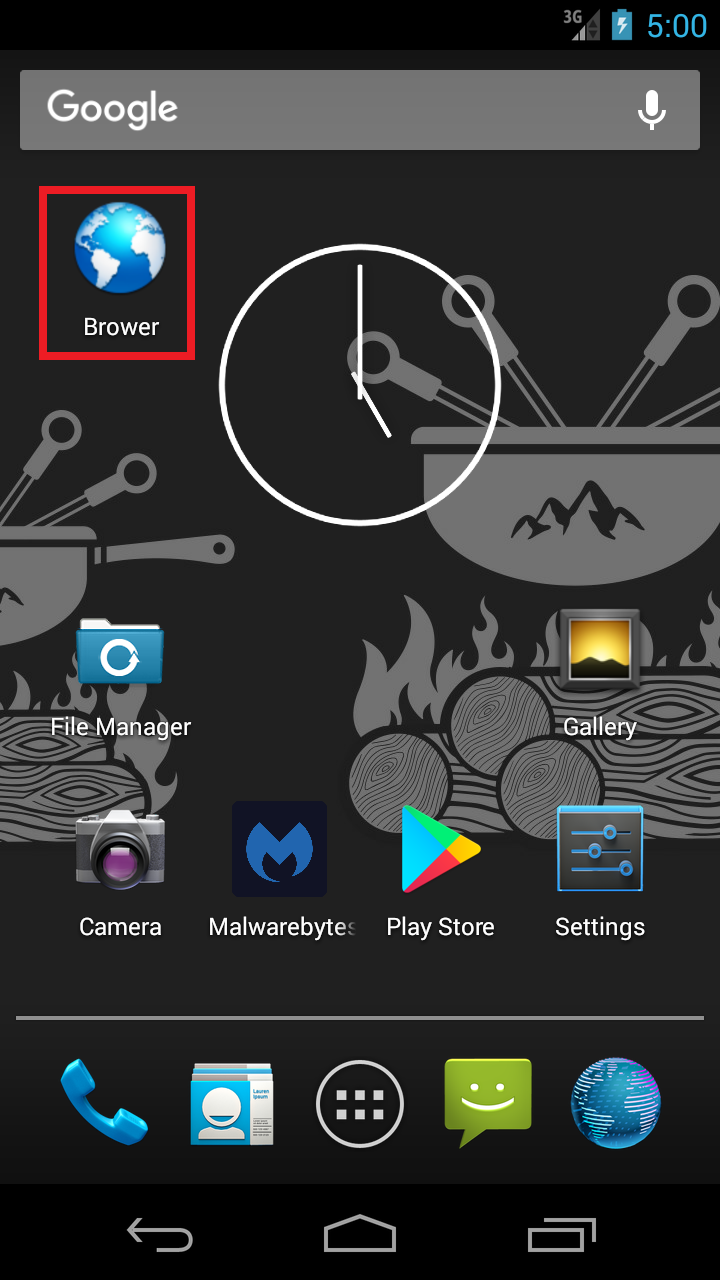
Shortcut to maliciousness
Another trait of Clicker.hyj is creating a shortcut that opens up the default Web browser to a URL that is no longer active — who knows what malicious content it once contained!
Even more money scams
To gain even more revenue, Clicker.hyj sends SMS messages to the affected device’s contact list. These SMS messages attempt to trick the user into subscribing to a pay-for-service via SMS:This application has Asia's largest video library, is now to super preferential price of the massive broadcasting, constantly surprises. Just sms registration can receive various hot video. You want to hear our act in pettish, you want to take a look at the beauty of the hot body, Only INR30.00. immediately at the click of a button, fast join us! Wonderful content is absolutely not to be missed!Subscribe to the
All about the $$$ Crooks know there is real money in mobile malware — consequently, we will continue to see the rise of malware like Clicker.hyj.”>
In conclusion, be wary of installing third-party apps from untrusted app stores. It is also a good idea to always have a scanner installed on your phone like Malwarebytes anti-malware mobile — which, for the record, is FREE.
Stay safe out there!
Nathan Collier










